Microsoft has rolled out updates to fix a remote code execution vulnerability impacting SharePoint that could be exploited by bad actors in attacks without requiring any specialized conditions to be met. The vulnerability, tracked as CVE-2026-45659, carries a CVSS score of 8.8. It has been assigned an important severity. “Deserialization of untrusted data in Microsoft … Read More “Microsoft Patches SharePoint RCE Flaw CVE-2026-45659 Across Server Versions – The Hacker News” »
Every single day, hackers are finding new ways to crash websites and steal data. But right now, something has changed. Hackers are no longer working alone. They are now using powerful Artificial Intelligence (AI) tools to make their attacks faster, stronger, and much harder to stop. According to recent updates from The Hacker News, bad … Read More “New AI DDoS Attacks Are Smarter. Learn How to Fight Back in This Webinar – The Hacker News” »
Multi-factor authentication (MFA) was supposed to close a critical gap in identity security. It meant that, even if an attacker possessed the account credentials, they couldn’t log in without the second factor. While that logic was sound, attackers have now figured out that they don’t need to steal the second factor: they just need the … Read More “MFA Prompt Bombing: Why Your Second Factor Isn’t Saving You – The Hacker News” »
CERT-In urges 12-hour patching of exposed flaws as AI compresses exploitation timelines – Read More –
CERT-In Mandates 12-Hour Patching for Internet-Facing Flaws Amid AI-Assisted Attacks – The Hacker News
The Indian Computer Emergency Response Team (CERT-In) has issued new guidelines requiring organizations to patch critical security vulnerabilities in internet-exposed systems within 12 hours of being flagged where “feasible” to safeguard against potential threats stemming from threat actors’ abuse of artificial intelligence (AI) tools and large language models (LLMs) to automate vulnerability – Read More … Read More “CERT-In Mandates 12-Hour Patching for Internet-Facing Flaws Amid AI-Assisted Attacks – The Hacker News” »
The Iranian state-sponsored threat actor known as Nimbus Manticore (aka Screening Serpens and UNC1549) has been attributed to a fresh campaign using lures impersonating organizations in the aviation and software sectors across the U.S., Europe, and the Middle East following the joint U.S.-Israeli military campaign against the country in late February 2026. The activity, besides … Read More “Iranian Hackers Deploy MiniFast and MiniJunk V2 via Phishing and SEO Poisoning – The Hacker News” »
Iran’s Nimbus Manticore pushes AI-built MiniFast backdoor via phishing and SEO poisoning – Read More –
A now-patched high-severity security flaw affecting Digital Knowledge KnowledgeDeliver, a Learning Management System (LMS) popular in Japan, was exploited as a zero-day to deliver the Godzilla web shell and ultimately facilitate the deployment of Cobalt Strike Beacon. The vulnerability, tracked as CVE-2026-5426 (CVSS score: 7.5), stems from the use of hard-coded ASP.NET machine keys, leading … Read More “KnowledgeDeliver LMS Flaw Exploited to Deploy Godzilla and Cobalt Strike – The Hacker News” »
Posted by Noel Butler via Fulldisclosure on May 25 So when is the fix for dovecot 2.3 source code due to be released? Since by your wording by not including the first detected versions, it must be assumed 2.3 is affected, and as no EOL has been published or announced for 2.3.x, and as … Read More “Re: Dovecot Security Advisory OXDC-2026-0002 – Full Disclosure” »
Posted by Adamczyk Blazej on May 25 ━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━ Multiple vulnerabilities in Sparx Pro Cloud Server and Enterprise Architect ━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━ General… – Read More – Full Disclosure
[SECURITY ADVISORY] CVE-2026-34473 – Unauthenticated DoS in 17+ ZTE Router Models (140K+ Devices) – Full Disclosure
![[SECURITY ADVISORY] CVE-2026-34473 – Unauthenticated DoS in 17+ ZTE Router Models (140K+ Devices) [SECURITY ADVISORY] CVE-2026-34473 – Unauthenticated DoS in 17+ ZTE Router Models (140K+ Devices) – Full Disclosure](https://attackfeed.com/wp-content/uploads/2026/05/fulldisclosure-img-NWuSUV.png)
Posted by m.nageh on May 25 —–BEGIN SECURITY ADVISORY—– Advisory ID: MONX-2026-001 CVE ID: CVE-2026-34473 Title: Unauthenticated Denial of Service via Oversized POST Body in ZTE Router CGILua Parser Affected: 17+ ZTE ZXHN router models (~140,000 publicly exposed devices) CVSS Score: 7.5 (AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H) Date: 2026-05-20 Author: Mina Nageh Salalma (Monx Research) Contact: minanageh379 () … Read More “[SECURITY ADVISORY] CVE-2026-34473 – Unauthenticated DoS in 17+ ZTE Router Models (140K+ Devices) – Full Disclosure” »
[SECURITY ADVISORY] CVE-2026-34472 – ZTE ZXHN H188A V6 Authentication Bypass via Pre-Login Wizard – Full Disclosure
![[SECURITY ADVISORY] CVE-2026-34472 – ZTE ZXHN H188A V6 Authentication Bypass via Pre-Login Wizard [SECURITY ADVISORY] CVE-2026-34472 – ZTE ZXHN H188A V6 Authentication Bypass via Pre-Login Wizard – Full Disclosure](https://attackfeed.com/wp-content/uploads/2026/05/fulldisclosure-img-95vjdr.png)
Posted by m.nageh on May 25 —–BEGIN SECURITY ADVISORY—– Advisory ID: MONX-2026-002 CVE ID: CVE-2026-34472 Title: ZTE ZXHN H188A V6 – Authentication Bypass via Pre-Login Wizard Credential Leakage Affected: ZTE ZXHN H188A V6.0.10P2_TE, V6.0.10P3N3_TE Date: 2026-05-20 Author: Mina Nageh Salalma (Monx Research) Contact: minanageh379 () gmail com Public URL:… – Read More – Full Disclosure
[SECURITY ADVISORY] CVE-2026-34474 – ZTE H298A/H108N Unauthenticated Admin Credential Exposure – Full Disclosure
![[SECURITY ADVISORY] CVE-2026-34474 – ZTE H298A/H108N Unauthenticated Admin Credential Exposure [SECURITY ADVISORY] CVE-2026-34474 – ZTE H298A/H108N Unauthenticated Admin Credential Exposure – Full Disclosure](https://attackfeed.com/wp-content/uploads/2026/05/fulldisclosure-img-rInpGC.png)
Posted by m.nageh on May 25 —–BEGIN SECURITY ADVISORY—– Advisory ID: MONX-2026-003 CVE ID: CVE-2026-34474 Title: ZTE ZXHN H298A / H108N – Unauthenticated Admin Password & WLAN Credential Exposure Affected: ZTE ZXHN H298A 1.1, ZTE ZXHN H108N 2.6 (EOL; no patch planned) Date: 2026-05-20 Author: Mina Nageh Salalma (Monx Research) Contact: minanageh379 () gmail … Read More “[SECURITY ADVISORY] CVE-2026-34474 – ZTE H298A/H108N Unauthenticated Admin Credential Exposure – Full Disclosure” »
[SECURITY ADVISORY] CVE-2021-21735 – ZTE ZXHN H168N V3.5 Unauthenticated Admin Credential Leak – Full Disclosure
![[SECURITY ADVISORY] CVE-2021-21735 – ZTE ZXHN H168N V3.5 Unauthenticated Admin Credential Leak [SECURITY ADVISORY] CVE-2021-21735 – ZTE ZXHN H168N V3.5 Unauthenticated Admin Credential Leak – Full Disclosure](https://attackfeed.com/wp-content/uploads/2026/05/fulldisclosure-img-pmdaMB.png)
Posted by m.nageh on May 25 —–BEGIN SECURITY ADVISORY—– Advisory ID: MONX-2021-001 CVE ID: CVE-2021-21735 Title: ZTE ZXHN H168N V3.5 – Unauthenticated Wizard Credential Disclosure to Full Admin Compromise Affected: ZTE ZXHN H168N V3.5 Date: 2026-05-20 Author: Mina Nageh Salalma (Monx Research) Contact: minanageh379 () gmail com Public URL:… – Read More – Full Disclosure
SSRF in Anthropic mcp-server-fetch and Microsoft playwright-mcp — publicly disclosed via GitHub issues – Full Disclosure

Posted by outreach on May 25 —–BEGIN SECURITY ADVISORY—– Title: Server-Side Request Forgery (SSRF) in Anthropic mcp-server-fetch and Microsoft playwright-mcp Author: Syed Anas Mohiuddin <anasmohiuddinsyed () gmail com> Date: May 25, 2026 CVSS: 7.5 (HIGH) — AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N References: Already public via GitHub issues (see below) == AFFECTED PRODUCTS == 1. Anthropic mcp-server-fetch (modelcontextprotocol/servers) All … Read More “SSRF in Anthropic mcp-server-fetch and Microsoft playwright-mcp — publicly disclosed via GitHub issues – Full Disclosure” »
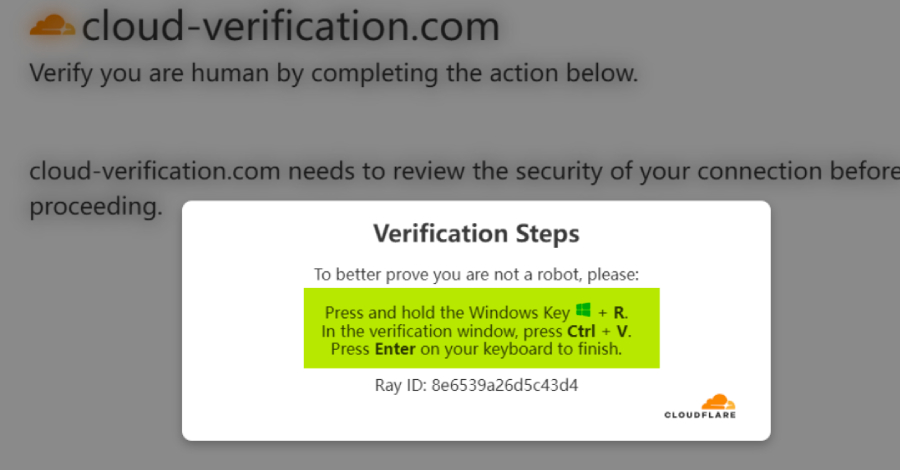
FBI Chief Kash Patel’s Clothing Store Hacked in ClickFix Infostealer Attack – Hackread – Cybersecurity News, Data Breaches, AI and More
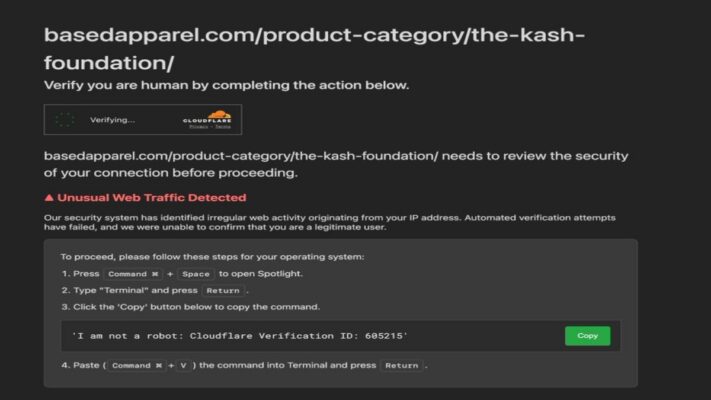
Hackers compromised FBI Chief Kash Patel’s clothing store in a ClickFix attack that tricked macOS users into installing infostealer malware. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
⚡ Weekly Recap: Linux Flaws, Defender 0-Days, Router Botnets, and Supply Chain Chaos – The Hacker News

Monday recap. Same mess, new week. A sketchy dev tool got people pwned, old bugs came back from the dead, and security products somehow needed protecting from themselves. A bunch of companies spent the week checking old boxes and forgotten servers they should’ve patched years ago. Good times. Phishing crews are getting smarter too – … Read More “⚡ Weekly Recap: Linux Flaws, Defender 0-Days, Router Botnets, and Supply Chain Chaos – The Hacker News” »
Nigel Farage’s Russian hack claim ‘without any merit’, former NCSC chief says – Data and computer security | The Guardian

Ciaran Martin says Reform UK leader’s allegation over Guardian report on £5m gift ‘entirely unsubstantiated’ Nigel Farage’s claim that a Russian hack was behind a Guardian report on the £5m gift he received from a crypto billionaire has been described as “without any merit” by a former head of the National Cyber Security Centre. Ciaran … Read More “Nigel Farage’s Russian hack claim ‘without any merit’, former NCSC chief says – Data and computer security | The Guardian” »
Authorities in the Netherlands have arrested the co-owners of two related Internet hosting companies for operating IT infrastructure used by Russia to carry out cyberattacks, influence operations and disinformation campaigns inside the European Union. The two men were the focus of a 2025 KrebsOnSecurity story about how their hosting companies had assumed control over the … Read More “Netherlands Seizes 800 Servers, Arrests 2 for Aiding Cyberattacks – Krebs on Security” »
Netherlands Busts Bulletproof Hosting Network Linked to Disinformation and Cybercrime – Hackread – Cybersecurity News, Data Breaches, AI and More

Dutch authorities arrested two suspects after dismantling a bulletproof hosting network linked to cybercrime, disinfo, and Russian sanctions evasion. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Ask a cybersecurity pro about Network Detection and Response (NDR) and you might still hear “Noisy,” “Too much data.” But ask the teams running NDR that includes agentic AI capabilities and you’ll hear they’re actually using it to catch threats earlier, triage faster, and chase fewer false positives. The old complaint lingers in part because … Read More “The Alert Firehose Finally Meets Its Match – The Hacker News” »
Threat actors are exploiting a recently disclosed critical security flaw in Ghost CMS to inject malicious JavaScript code with an aim to fuel ClickFix attacks. According to QiAnXin XLab, the activity involves the exploitation of CVE-2026-26980 (CVSS score: 9.4), an SQL injection vulnerability in Ghost’s Content API that could allow an unauthenticated attacker to read … Read More “Ghost CMS CVE-2026-26980 Exploited to Hijack 700+ Sites for ClickFix Attacks – The Hacker News” »
Cybersecurity researchers have shed light on a cross-platform malware called RemotePE that has been put to use by the North Korea-linked Lazarus Group in attacks targeting financial and cryptocurrency organizations. RemotePE, per NCC Group subsidiary Fox-IT, is part of a multi-stage attack chain that involves two loaders tracked as DPAPILoader and RemotePELoader. “DPAPILoader decrypts and … Read More “Lazarus Deploys RemotePE Memory-Only RAT Against Financial and Crypto Firms – The Hacker News” »
The Kali365 phishing-as-a-service platform lowers the barrier of entry for cybercriminals, said the FBI – Read More –
From fake F1 streams to counterfeit merch, fraudsters are exploiting fans online and the Bitdefender Cybersecurity Grand Prix Fan Threat Index details how – Read More –
TrapDoor Supply Chain Attack Spreads Credential-Stealing Malware via npm, PyPI, and CratesIO – The Hacker News
A new coordinated cross-ecosystem software supply chain attack campaign has targeted npm, PyPI, and Crates.io to distribute credential-stealing malware. The campaign, codenamed TrapDoor, spans more than 34 malicious packages across over 384 versions. The earliest activity was recorded on May 22, 2026, at 8:20 p.m. UTC, with new packages published to the ecosystems in waves … Read More “TrapDoor Supply Chain Attack Spreads Credential-Stealing Malware via npm, PyPI, and CratesIO – The Hacker News” »
Hacker Selling 340 Million OnlyFans User Records Built From Old Breaches – Hackread – Cybersecurity News, Data Breaches, AI and More

A hacker is selling a 340M OnlyFans user database allegedly built by matching old breach data and public profiles to real OnlyFans accounts. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Packagist Supply Chain Attack Infects 8 Packages Using GitHub-Hosted Linux Malware – The Hacker News

A new “coordinated” supply chain attack campaign has impacted eight packages on Packagist including malicious code designed to run a Linux binary retrieved from a GitHub Releases URL. “Although the affected packages were all Composer packages, the malicious code was not added to composer.json,” Socket said. “Instead, it was inserted into package.json, targeting projects that … Read More “Packagist Supply Chain Attack Infects 8 Packages Using GitHub-Hosted Linux Malware – The Hacker News” »
npm Adds 2FA-Gated Publishing and Package Install Controls Against Supply Chain Attacks – The Hacker News

GitHub has rolled out new controls for npm to improve the security of the software supply chain, giving maintainers the ability to explicitly approve a release prior to the packages becoming publicly available for installation. Called staged publishing, the feature is now generally available on npm. It mandates that a human maintainer pass a two-factor … Read More “npm Adds 2FA-Gated Publishing and Package Install Controls Against Supply Chain Attacks – The Hacker News” »
Anthropic on Friday disclosed that Project Glasswing has helped uncover more than 10,000 high- or critical-severity vulnerabilities across some of the most “systemically” important software across the world since the cybersecurity initiative went live last month. Project Glasswing is an effort led by the artificial intelligence (AI) company, as part of which a small set … Read More “Claude Mythos AI Finds 10,000 High-Severity Flaws in Widely Used Software – The Hacker News” »
RondoDox Botnet Exploits Critical 2018 Vulnerability to Hijack ASUS Routers – Hackread – Cybersecurity News, Data Breaches, AI and More
Cybersecurity firm VulnCheck reveals hackers are using a critical 2018 vulnerability to bypass authentication and hack over a million ASUS routers. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Laravel-Lang PHP Packages Compromised to Deliver Cross-Platform Credential Stealer – The Hacker News
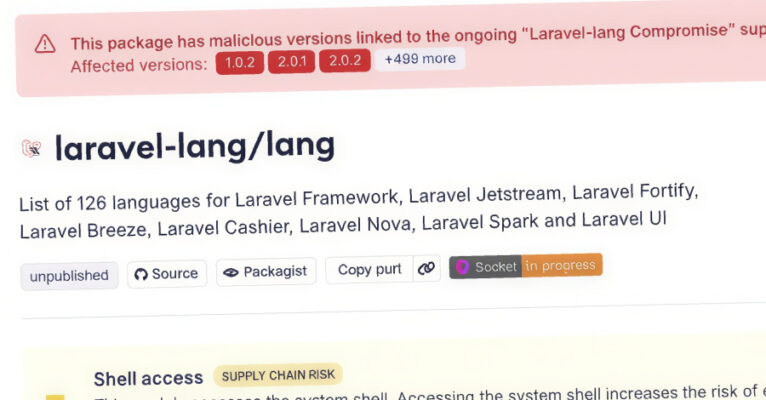
Cybersecurity researchers have flagged a fresh software supply chain attack campaign that has targeted multiple PHP packages belonging to Laravel-Lang to deliver a comprehensive credential-stealing framework. The affected packages include – laravel-lang/lang laravel-lang/http-statuses laravel-lang/attributes laravel-lang/actions “The timing and pattern of the newly published tags – Read More – The Hacker News
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a recently patched critical security flaw impacting Drupal Core to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation. The vulnerability in question is CVE-2026-9082 (CVSS score: 6.5), an SQL injection vulnerability affecting all supported versions of Drupal Core. “Drupal Core – … Read More “Drupal Core SQL Injection Bug Actively Exploited, Added to CISA KEV – The Hacker News” »
A maximum-severity security vulnerability impacting LiteSpeed User-End cPanel Plugin has come under active exploitation in the wild. The flaw, tracked as CVE-2026-48172 (CVSS score: 10.0), relates to an instance of incorrect privilege assignment that an attacker could abuse to run arbitrary scripts with elevated permissions. “Any cPanel user (including an attacker or a compromised account) … Read More “LiteSpeed cPanel Plugin CVE-2026-48172 Exploited to Run Scripts as Root – The Hacker News” »
FBI Warns of Kali365 Phishing Service Targeting Microsoft 365 Account – Hackread – Cybersecurity News, Data Breaches, AI and More

FBI warns of Kali365, a PaaS scam kit that lets cybercriminals bypass MFA and hijack Microsoft 365 accounts without passwords. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
The FBI is warning organizations and defenders about Kali365, a growing phishing-as-a-service platform that retrieves Microsoft 365 access tokens, issuing a public service announcement Thursday. The toolkit bypasses multi-factor authentication and abuses OAuth device code authorizations via phishing lures impersonating common enterprise services. This technique grants cybercriminal-controlled applications access to Microsoft 365 accounts, opening victims … Read More “FBI warns about fast-growing phishing kit targeting Microsoft 365 users – CyberScoop” »
Authorities in Europe and North America have announced the dismantling of a criminal virtual private network (VPN) service used by criminal actors to obscure the origins of ransomware attacks, data theft, scanning, and denial-of-service attacks. The disruption of First VPN Service was led by France and the Netherlands, with several other nations supporting the investigation … Read More “First VPN Dismantled in Global Takedown Over Use by 25 Ransomware Groups – The Hacker News” »
The Belarus-aligned threat actor known as Ghostwriter (aka UAC-0057 and UNC1151Ukraine’s National Security and Defense Council) has been observed using lures related to Prometheus, a Ukrainian online learning platform, to target government organizations in the country. The activity, per the Computer Emergency Response Team of Ukraine (CERT-UA), involves sending phishing emails to government – Read … Read More “Ghostwriter Targets Ukraine Government Entities with Prometheus Phishing Malware – The Hacker News” »
Lawmakers in both houses of Congress are demanding answers from the U.S. Cybersecurity & Infrastructure Security Agency (CISA) after KrebsOnSecurity reported this week that a CISA contractor intentionally published AWS GovCloud keys and a vast trove of other agency secrets on a public GitHub account. The inquiry comes as CISA is still struggling to contain … Read More “Lawmakers Demand Answers as CISA Tries to Contain Data Leak – Krebs on Security” »
5,561 GitHub Repositories Hit by Megalodon Supply Chain Attack in Six Hours – Hackread – Cybersecurity News, Data Breaches, AI and More
SafeDep uncovered the Megalodon attack targeting 5,561 GitHub repositories with malicious CI workflows and cloud credential theft. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
1 Introduction This article provides a technical analysis of how many Windows kernel mode drivers can be interacted with from user mode without the hardware they were developed for. This work was motivated by driver-oriented vulnerability research and the need to evaluate the exploitability of individual findings, which frequently affect code whose reachability is hardware-gated. … Read More “Making Vulnerable Drivers Exploitable Without Hardware – The BYOVD Perspective – The Hacker News” »
Cybersecurity researchers have disclosed details of a new automated campaign called Megalodon that has pushed 5,718 malicious commits to 5,561 GitHub repositories within a six-hour window. “Using throwaway accounts and forged author identities (build-bot, auto-ci, ci-bot, pipeline-bot), the attacker injected GitHub Actions workflows containing base64-encoded bash payloads that exfiltrate CI – Read More – The … Read More “Megalodon GitHub Attack Targets 5,561 Repos with Malicious CI/CD Workflows – The Hacker News” »
The infostealer payload in this campaign collect a vast amount of data, from collaboration authentication keys to cryptocurrency wallets – Read More –
Total figure for fraudulent transactions Apple has blocked since 2020 now stands at over $11bn – Read More –
The U.S. Department of Justice (DoJ) on Thursday announced the arrest of a Canadian man in connection with allegedly operating a distributed denial-of-service (DDoS) botnet known as Kimwolf. In tandem, Jacob Butler (aka Dort), 23, Ottawa, Canada, has been charged with offenses related to the development and operation of the botnet. Kimwolf is assessed to … Read More “Kimwolf DDoS Botnet Operator Arrested in Canada Over DDoS-for-Hire Attacks – The Hacker News” »
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added two security flaws impacting Langflow and Trend Micro Apex One to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation. The vulnerabilities in question are listed below – CVE-2025-34291 (CVSS score: 9.4) – An origin validation error vulnerability in Langflow that could … Read More “CISA Adds Exploited Langflow and Trend Micro Apex One Vulnerabilities to KEV – The Hacker News” »
Cisco has rolled out updates for a maximum-severity security flaw impacting Secure Workload that could allow an unauthenticated, remote attacker to access sensitive data. Tracked as CVE-2026-20223 (CVSS score: 10.0), the vulnerability arises from insufficient validation and authentication when accessing REST API endpoints. “An attacker could exploit this vulnerability if they are able to send … Read More “Cisco Patches CVSS 10.0 Secure Workload REST API Flaw Enabling Data Access – The Hacker News” »
Authorities arrested and unsealed charges against a Canadian man accused of running Kimwolf, one of the most far-reaching DDoS botnets on record, the Justice Department said Thursday. Jacob Butler was arrested Wednesday in Ottawa, Canada, and awaits extradition to the United States where he is charged with aiding and abetting computer intrusions and, if convicted, … Read More “Alleged leader of Kimwolf, a sweeping botnet for cybercriminals, arrested in Canada – CyberScoop” »
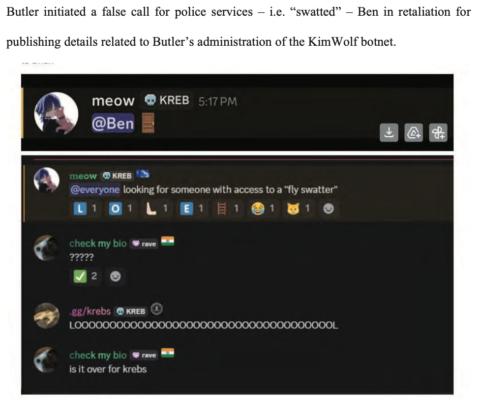
Canadian authorities on Wednesday arrested a 23-year-old Ottawa man on suspicion of building and operating Kimwolf, a fast spreading Internet-of-Things botnet that enslaved millions of devices for use in a series of massive distributed denial-of-service (DDoS) attacks over the past six months. KrebsOnSecurity publicly named the suspect in February 2026 after the accused launched a … Read More “Alleged Kimwolf Botmaster ‘Dort’ Arrested, Charged in U.S. and Canada – Krebs on Security” »
Two cybersecurity-focused members of Congress agreed Thursday that reductions to the Cybersecurity and Infrastructure Security Agency have done too much damage to an agency essential to defending civilian networks against foreign adversaries. Rep. Don Bacon, R-Neb., and Rep. James Walkinshaw, D-Va., spoke during a discussion at the National Cyber Innovation Forum. Despite representing different parties, … Read More “Lawmakers from both parties say CISA cuts have gone too far – CyberScoop” »