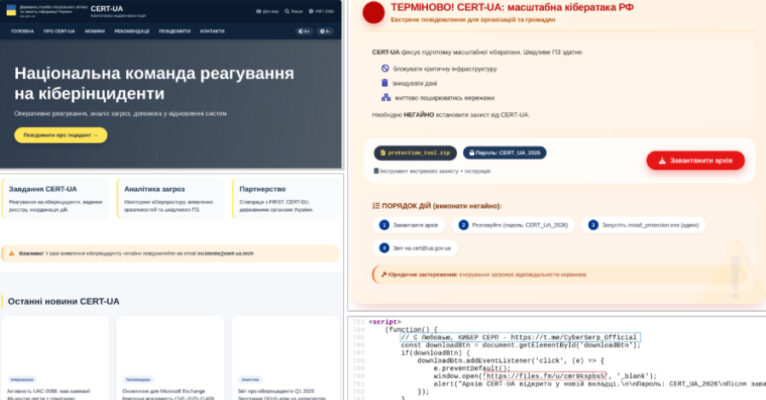
The Computer Emergency Response Team of Ukraine (CERT-UA) has disclosed details of a new phishing campaign in which the cybersecurity agency itself was impersonated to distribute a remote administration tool known as AGEWHEEZE. As part of the attacks, the threat actors, tracked as UAC-0255, sent emails on March 26 and 27, 2026, posing as CERT-UA … Read More “CERT-UA Impersonation Campaign Spread AGEWHEEZE Malware to 1 Million Emails – The Hacker News” »
Anthropic Leaks 512,000 Lines of Claude AI Code in Major Blunder – Hackread – Cybersecurity News, Data Breaches, AI and More
Human error exposed 512,000+ lines of Anthropic Claude AI Code, revealing KAIROS and Capybara secrets, pushing users to switch to the Native Installer. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
A Chinese cyberespionage group has shifted its gaze back to Europe after years of focusing on other parts of the world, Proofpoint research published Wednesday found. The surge began in mid-2025, with a bevy of issues bubbling up between China and Europe, the company said. Proofpoint labels the government-linked group TA416, but other companies track … Read More “European-Chinese geopolitical issues drive renewed cyberespionage campaign – CyberScoop” »
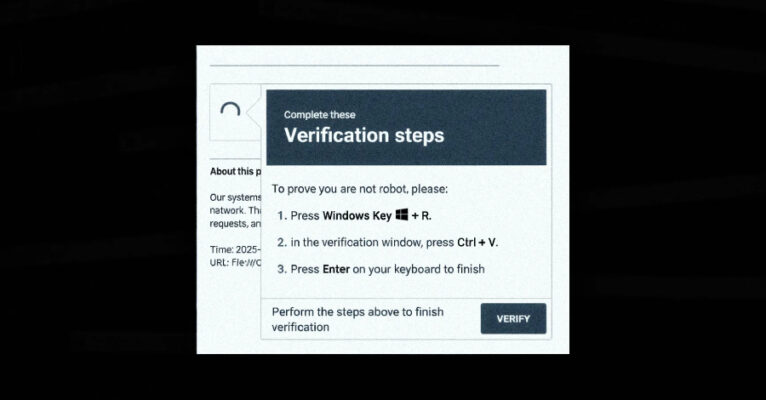
Venom Stealer malware-as-a-service automates ClickFix social engineering, credential and crypto exfiltration – Read More –
Google on Thursday released security updates for its Chrome web browser to address 21 vulnerabilities, including a zero-day flaw that it said has been exploited in the wild. The high-severity vulnerability, CVE-2026-5281 (CVSS score: N/A), concerns a use-after-free bug in Dawn, an open-source and cross-platform implementation of the WebGPU standard. “Use-after-free in Dawn in Google … Read More “New Chrome Zero-Day CVE-2026-5281 Under Active Exploitation — Patch Released – The Hacker News” »
Microsoft Warns of WhatsApp-Delivered VBS Malware Hijacking Windows via UAC Bypass – The Hacker News

Microsoft is calling attention to a new campaign that has leveraged WhatsApp messages to distribute malicious Visual Basic Script (VBS) files. The activity, beginning in late February 2026, leverages these scripts to initiate a multi-stage infection chain for establishing persistence and enabling remote access. It’s currently not known what lures the threat actors use to … Read More “Microsoft Warns of WhatsApp-Delivered VBS Malware Hijacking Windows via UAC Bypass – The Hacker News” »
A multi-pronged phishing campaign is targeting Spanish-speaking users in organizations across Latin America and Europe to deliver Windows banking trojans like Casbaneiro (aka Metamorfo) via another malware called Horabot. The activity has been attributed to a Brazilian cybercrime threat actor tracked as Augmented Marauder and Water Saci. The e-crime group was first documented by Trend … Read More “Casbaneiro Phishing Targets Latin America and Europe Using Dynamic PDF Lures – The Hacker News” »
Ransomware Groups Exploit Legit IT Tools to Bypass Antivirus – Hackread – Cybersecurity News, Data Breaches, AI and More

New research from Seqrite explains the ‘dual-use dilemma,’ where ransomware attackers repurpose legitimate IT tools like IOBit Unlocker… – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
There is a character that keeps appearing in enterprise security departments, and most CISOs know exactly who that is. It doesn’t build. It doesn’t enable. Its entire function is to say “No.” No to ChatGPT. No to DeepSeek. No to the file-sharing tool the product team swears by. For years, this looked like security. But … Read More “Block the Prompt, Not the Work: The End of “Doctor No” – The Hacker News” »
Chinese state-backed group TA416 had suspended its cyber espionage operations in Europe since 2023, noted Proofpoint – Read More –
Defending Encryption in the Post Quantum Era – Hackread – Cybersecurity News, Data Breaches, AI and More
Post-quantum cryptography explained, risks of quantum attacks, and steps to secure data, systems, and infrastructure for a quantum-resilient… – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Cybersecurity Firm TAC Security Hits 10,000 Clients, Enters Top 5 in Global VM & AppSec – Hackread – Cybersecurity News, Data Breaches, AI and More

New York, New York, April 1st, 2026, CyberNewswire – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
ImageMagick Zero-Day Enables RCE on Linux and WordPress Servers – Hackread – Cybersecurity News, Data Breaches, AI and More
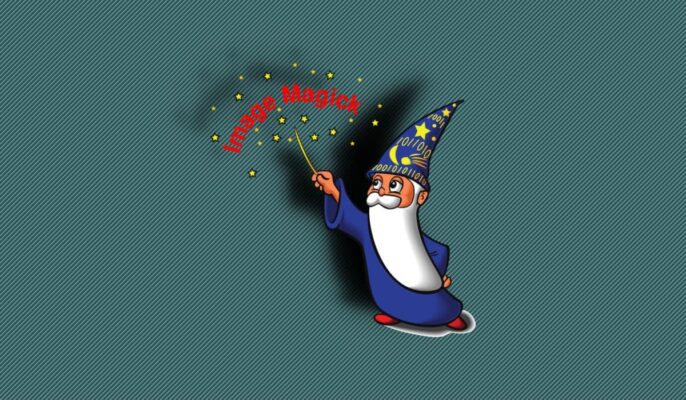
New research from Octagon Networks reveals a critical zero-day ImageMagick vulnerability that allows Remote Code Execution (RCE) via simple image uploads affecting Ubuntu, Amazon Linux, and WordPress. This magic byte shift bypasses even the most secure policies. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
3 Reasons Attackers Are Using Your Trusted Tools Against You (And Why You Don’t See It Coming) – The Hacker News

For years, cybersecurity has followed a familiar model: block malware, stop the attack. Now, attackers are moving on to what’s next. Threat actors now use malware less frequently in favor of what’s already inside your environment, including abusing trusted tools, native binaries, and legitimate admin utilities to move laterally, escalate privileges, and persist without raising … Read More “3 Reasons Attackers Are Using Your Trusted Tools Against You (And Why You Don’t See It Coming) – The Hacker News” »
A man has appeared in federal court in Austin, Texas, after being extradited to the United States to face charges related to his alleged role as a key developer of the notorious RedLine malware. Read more in my article on the Hot for Security blog. – Read More – GRAHAM CLULEY
Threat actors hijacked the popular npm package axios to spread RAT malware after compromising an open‑source maintainer’s account, researchers warn – Read More –
Most UK manufacturers compromised last year suffered financial loss, says ESET – Read More –
Google has formally attributed the supply chain compromise of the popular Axios npm package to a financially motivated North Korean threat activity cluster tracked as UNC1069. “We have attributed the attack to a suspected North Korean threat actor we track as UNC1069,” John Hultquist, chief analyst at Google Threat Intelligence Group (GTIG), told The Hacker … Read More “Google Attributes Axios npm Supply Chain Attack to North Korean Group UNC1069 – The Hacker News” »
Anthropic on Tuesday confirmed that internal code for its popular artificial intelligence (AI) coding assistant, Claude Code, had been inadvertently released due to a human error. “No sensitive customer data or credentials were involved or exposed,” an Anthropic spokesperson said in a statement shared with CNBC News. “This was a release packaging issue caused by … Read More “Claude Code Source Leaked via npm Packaging Error, Anthropic Confirms – The Hacker News” »
Phantom Stealer .NET harvests browser credentials, cookies, cards, sessions, as stealer-as-a-service – Read More –
Maryland man accused of $53m Uranium Finance hack, exploited smart contract flaws, laundered funds – Read More –
White House executive order purports to limit mail-in voting, mandate federal voter lists – CyberScoop

President Donald Trump signed an executive order Tuesday that purports to limit mail-in voting, though critics say the move will almost certainly be challenged in court on constitutional grounds. The order instructs the Homeland Security secretary, the director of U.S. Citizenship and Immigrations Services and the commissioner of the Social Security Administration to compile lists … Read More “White House executive order purports to limit mail-in voting, mandate federal voter lists – CyberScoop” »
Google on Monday said it’s officially rolling out Android developer verification to all developers to combat the problem of bad actors distributing harmful apps while “hiding behind anonymity.” The development comes ahead of a planned verification mandate that goes into effect in Brazil, Indonesia, Singapore, and Thailand this September, before it expands globally next year. … Read More “Android Developer Verification Rollout Begins Ahead of September Enforcement – The Hacker News” »
A high-severity security flaw in the TrueConf client video conferencing software has been exploited in the wild as a zero-day as part of a campaign targeting government entities in Southeast Asia dubbed TrueChaos. The vulnerability in question is CVE-2026-3502 (CVSS score: 7.8), a lack of integrity check when fetching application update code, allowing an attacker … Read More “TrueConf Zero-Day Exploited in Attacks on Southeast Asian Government Networks – The Hacker News” »
A hacker briefly delivered malware this week through a popular open-source project for software developers that has an estimated 100 million weekly downloads, raising the possibility of compromises spreading widely through a supply-chain attack. Axios is a JavaScript client library used in web requests. The unknown attacker hijacked the npm account — npm being a … Read More “Attack on axios software developer tool threatens widespread compromises – CyberScoop” »
The NCSC has issued actions for individuals at risk of targeted attacks against messaging apps. – Read More – All Feed
Hackers Poison Axios npm Package with 100 Million Weekly Downloads – Hackread – Cybersecurity News, Data Breaches, AI and More
Axios npm Package compromised in a supply chain attack, exposing developers to malware, data theft, and full system takeover risks worldwide. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Post Content – Read More – IC3.gov News
Cybersecurity researchers have disclosed a security “blind spot” in Google Cloud’s Vertex AI platform that could allow artificial intelligence (AI) agents to be weaponized by an attacker to gain unauthorized access to sensitive data and compromise an organization’s cloud environment. According to Palo Alto Networks Unit 42, the issue relates to how the Vertex AI … Read More “Vertex AI Vulnerability Exposes Google Cloud Data and Private Artifacts – The Hacker News” »
The AI Arms Race – Why Unified Exposure Management Is Becoming a Boardroom Priority – The Hacker News
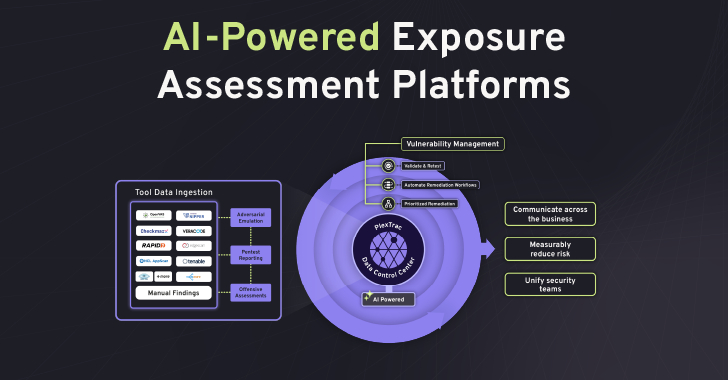
The cybersecurity landscape is accelerating at an unprecedented rate. What is emerging is not simply a rise in the number of vulnerabilities or tools, but a dramatic increase in speed. Speed of attack, speed of exploitation, and speed of change across modern environments. This is the defining challenge of the new era of digital warfare: … Read More “The AI Arms Race – Why Unified Exposure Management Is Becoming a Boardroom Priority – The Hacker News” »
Critical F5 BIG-IP Flaw Upgraded to 9.8 RCE, Exploited in the Wild – Hackread – Cybersecurity News, Data Breaches, AI and More

F5 BIG-IP APM flaw CVE-2025-53521 escalates to critical 9.8 RCE, actively exploited. Patch now, check IoCs, and secure vulnerable systems immediately. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Chinese-speaking users are the target of an active campaign that uses typosquatted domains impersonating trusted software brands to deliver a previously undocumented remote access trojan named AtlasCross RAT. “The operation covers VPN clients, encrypted messengers, video conferencing tools, cryptocurrency trackers, and e-commerce applications, with eleven confirmed delivery domains impersonating – Read More – The Hacker … Read More “Silver Fox Expands Asia Cyber Campaign with AtlasCross RAT and Fake Domains – The Hacker News” »
TeamPCP is exploring ways to monetize the secrets harvested during supply chain attacks, with identified ties to the Lapsus$ and Vect ransomware gangs – Read More –
OpenAI has patched vulnerability, which Check Point said was because of a DNS loophole – Read More –
Analysis from law firm Nockolds suggests non-cyber incidents are driving up employee data breaches – Read More –
The Digital Personal Data Protection (DPDP) Act, India is gradually changing from a mere policy to a practical guide…. The post Top 10 questions CISOs and DPOs are asking about DPDP in 2026 appeared first on JISA Softech Pvt Ltd. – Read More – JISA Softech Pvt Ltd
The National Cyber Security Centre wants UK firms to patch CVE-2025-53521 – Read More –
Iranian hackers breach FBI director’s personal email, and post his CV and photos online – GRAHAM CLULEY
It’s not every day that you read that the head of America’s top law enforcement agency has been hacked, but then – these aren’t ordinary times. Read more in my article on the Hot for Security blog. – Read More – GRAHAM CLULEY
The popular HTTP client known as Axios has suffered a supply chain attack after two newly published versions of the npm package introduced a malicious dependency. Versions 1.14.1 and 0.30.4 of Axios have been found to inject “plain-crypto-js” version 4.2.1 as a fake dependency. According to StepSecurity, the two versions were published using the compromised … Read More “Axios Supply Chain Attack Pushes Cross-Platform RAT via Compromised npm Account – The Hacker News” »
Lloyds app glitch exposed up to 447,936 customers’ transactions and personal data during update – Read More –
Tax-season phishing floods deliver RMM malware, credential theft, BEC and tax-form scams – Read More –
Kernel-level visibility reveals hidden data movement in breaches, exposing gaps in modern security tools and improving detection, compliance, and system behavior tracking. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
AI Agents Are Democratizing Finance but Also Redefining Risk – Hackread – Cybersecurity News, Data Breaches, AI and More
AI agents are transforming finance, enabling automated trading and payments, but introduce new risks around keys, data inputs and secure execution control. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
What is really slowing Tier 1 down: the threat itself or the process around it? In many SOCs, the biggest delays do not come from the threat alone. They come from fragmented workflows, manual triage steps, and limited visibility early in the investigation. Fixing those process gaps can help Tier 1 move faster, reduce unnecessary … Read More “3 SOC Process Fixes That Unlock Tier 1 Productivity – The Hacker News” »
OpenAI Codex Vulnerability Allowed Attackers to Steal GitHub Tokens – Hackread – Cybersecurity News, Data Breaches, AI and More
OpenAI Codex vulnerability allowed attackers to steal GitHub tokens via malicious branch names using hidden Unicode command injection flaw. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Wave Browser Brings Gaming Tools and Ocean Cleanup into the Same Tab – Hackread – Cybersecurity News, Data Breaches, AI and More
Wave Browser for gaming: built for multitasking, streaming, and tabs, with tools for gamers plus ocean cleanup support tied to everyday browsing activity. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
OpenAI Patches ChatGPT Data Exfiltration Flaw and Codex GitHub Token Vulnerability – The Hacker News
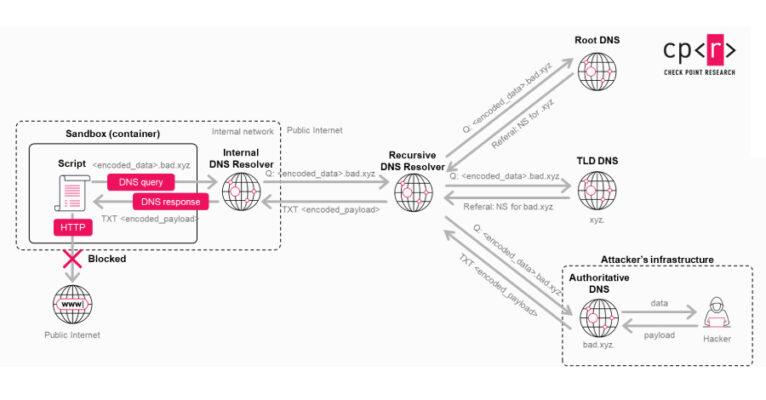
A previously unknown vulnerability in OpenAI ChatGPT allowed sensitive conversation data to be exfiltrated without user knowledge or consent, according to new findings from Check Point. “A single malicious prompt could turn an otherwise ordinary conversation into a covert exfiltration channel, leaking user messages, uploaded files, and other sensitive content,” the cybersecurity company said in … Read More “OpenAI Patches ChatGPT Data Exfiltration Flaw and Codex GitHub Token Vulnerability – The Hacker News” »
A new malware-based credential-stealing campaign, which researchers are calling “DeepLoad,” has been infecting enterprise business IT environments over the past In a report released Monday, ReliaQuest AI researchers Thassanai McCabe and Andrew Currie say the most relevant feature of this attack is the way it uses artificial intelligence and other engineering “to defeat the controls … Read More “Researchers say credential-stealing campaign used AI to build evasion ‘at every stage’ – CyberScoop” »
A new campaign has leveraged the ClickFix social engineering tactic as a way to distribute a previously undocumented malware loader referred to as DeepLoad. “It likely uses AI-assisted obfuscation and process injection to evade static scanning, while credential theft starts immediately and captures passwords and sessions even if the primary loader is blocked,” ReliaQuest researchers … Read More “DeepLoad Malware Uses ClickFix and WMI Persistence to Steal Browser Credentials – The Hacker News” »
24/7 Payments for 24/7 Agents: The Case for Crypto in the Machine Economy – Hackread – Cybersecurity News, Data Breaches, AI and More

Crypto enables 24/7 payments for AI agents, replacing fiat limits with scalable machine-to-machine transactions and powering the emerging machine economy. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More