Posted by Daniel Owens via Fulldisclosure on Mar 12 As previously mentioned, via “Struts2 and Related Framework Array/Collection DoS” (26 October 2025), hundreds of JavaScript object notation (JSON) libraries are vulnerable to unconstrained resource consumption through large JSON arrays, which, when deserialised, create arbitrarily large collections/arrays/data structures. This work looks specifically at the Apache … Read More “JSON Deserialiser Unconstrained Resource Consumption Quick Overview – Full Disclosure” »
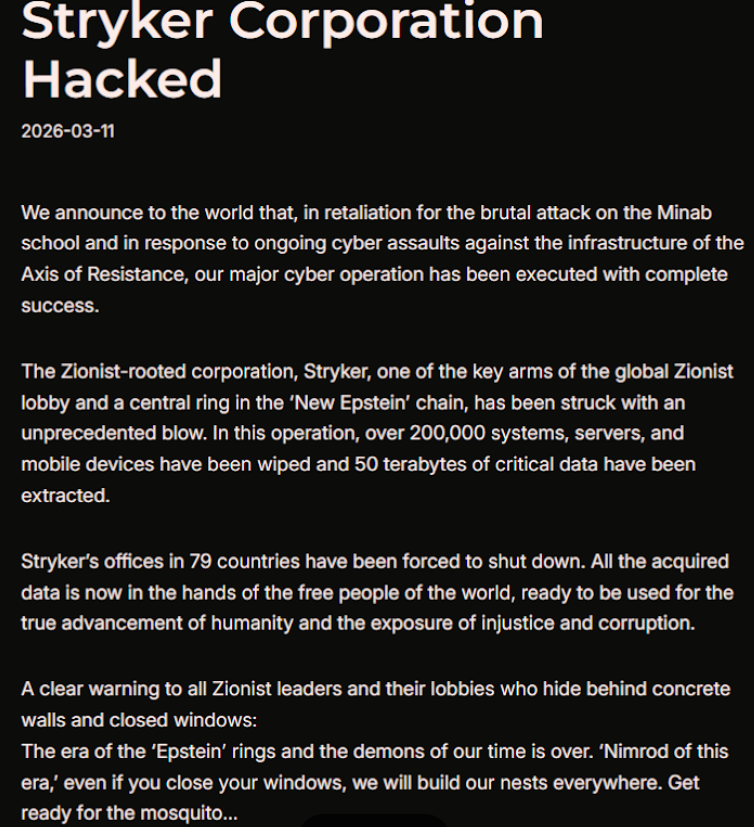
Stryker attack highlights nebulous nature of Iranian cyber activity amid joint U.S.-Israel conflict – CyberScoop

A cyberattack that an Iranian hacking group said it carried out against medical device manufacturer Stryker might mark Tehran’s first significant cyber action since the start of the joint U.S.-Israel conflict. But even that may have been a happy accident for Iranian hackers in what has been a low buzz of activity during that timeframe, … Read More “Stryker attack highlights nebulous nature of Iranian cyber activity amid joint U.S.-Israel conflict – CyberScoop” »
Feds Takes Down SocksEscort Proxy Network Used in Global Fraud Schemes – Hackread – Cybersecurity News, Data Breaches, AI and More

European and US agencies dismantled the SocksEscort proxy network built on infected routers and used by cybercriminals in global fraud schemes. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Hive0163 Uses AI-Assisted Slopoly Malware for Persistent Access in Ransomware Attacks – The Hacker News

Cybersecurity researchers have disclosed details of a suspected artificial intelligence (AI)-generated malware codenamed Slopoly put to use by a financially motivated threat actor named Hive0163. “Although still relatively unspectacular, AI-generated malware such as Slopoly shows how easily threat actors can weaponize AI to develop new malware frameworks in a fraction of the time it used … Read More “Hive0163 Uses AI-Assisted Slopoly Malware for Persistent Access in Ransomware Attacks – The Hacker News” »
Hackers Use Cloudflare Human Check to Hide Microsoft 365 Phishing Pages – Hackread – Cybersecurity News, Data Breaches, AI and More
Scammers are hijacking popular security tools like Cloudflare to hide fake Microsoft 365 login pages. Learn how this new invisible phishing campaign bypasses antivirus software and how you can stay safe. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Rust-Based VENON Malware Targets 33 Brazilian Banks with Credential-Stealing Overlays – The Hacker News
Cybersecurity researchers have disclosed details of a new banking malware targeting Brazilian users that’s written in Rust, marking a significant departure from other known Delphi-based malware families associated with the Latin American cybercrime ecosystem. The malware, which is designed to infect Windows systems and was first discovered last month, has been codenamed VENON by Brazilian … Read More “Rust-Based VENON Malware Targets 33 Brazilian Banks with Credential-Stealing Overlays – The Hacker News” »
Bell Ambulance Confirms Data Breach Affecting 237,830 Individuals – Hackread – Cybersecurity News, Data Breaches, AI and More

Bell Ambulance disclosed a data breach impacting 237,830 individuals after unauthorized access to its network exposed personal and medical data. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
If you just want to read the contest rules, click here. Willkommen zurück, meine Damen und Herren, zu unserem zweiten Wettbewerb in Berlin! That’s correct (if Google translate didn’t steer me wrong). After our inaugural competition last year, Pwn2Own returns to Berlin and OffensiveCon. Outside of our shipping troubles, we had an amazing time … Read More “Announcing Pwn2Own Berlin for 2026 – Zero Day Initiative – Blog” »
Authorities from multiple countries dismantled SocksEscort, a residential proxy network cybercriminals used to commit large-scale fraud, claiming access to about 369,000 IP addresses since 2020, the Justice Department said Thursday. Europol, which aided the investigation alongside various law enforcement agencies, Lumen’s Black Lotus Labs and the Shadowserver Foundation, said the malicious proxy service compromised routers … Read More “Authorities takedown global proxy network SocksEscort – CyberScoop” »
Officials worry Salt Typhoon apathy is killing momentum for tougher telecom security rules – CyberScoop

Two years ago, it was revealed that Chinese hackers had compromised at least ten U.S. telecoms, giving them broad access to phone data affecting nearly all Americans. Since then, public officials charged with responding to the campaign and bolstering the nation’s cyber defenses have reported a common problem. Many of their constituents struggle to understand … Read More “Officials worry Salt Typhoon apathy is killing momentum for tougher telecom security rules – CyberScoop” »
The critical vulnerability affecting both cloud and self-hosted n8n instances requires no authentication or even n8n account to be exploited – Read More –
PixRevolution Android trojan hijacks Brazil’s PIX payments in real time using accessibility abuse – Read More –
ThreatsDay Bulletin: OAuth Trap, EDR Killer, Signal Phishing, Zombie ZIP, AI Platform Hack & More – The Hacker News
Another Thursday, another pile of weird security stuff that somehow happened in just seven days. Some of it is clever. Some of it is lazy. A few bits fall into that uncomfortable category of “yeah… this is probably going to show up in real incidents sooner than we’d like.” The pattern this week feels familiar … Read More “ThreatsDay Bulletin: OAuth Trap, EDR Killer, Signal Phishing, Zombie ZIP, AI Platform Hack & More – The Hacker News” »
Phishing has quietly turned into one of the hardest enterprise threats to expose early. Instead of crude lures and obvious payloads, modern campaigns rely on trusted infrastructure, legitimate-looking authentication flows, and encrypted traffic that conceals malicious behavior from traditional detection layers. For CISOs, the priority is now clear: scale phishing detection in a way that … Read More “How to Scale Phishing Detection in Your SOC: 3 Steps for CISOs – The Hacker News” »
Post Content – Read More – IC3.gov News
Maintaining Security and Protecting Smart Home Devices from Hackers – Hackread – Cybersecurity News, Data Breaches, AI and More

Learn how to protect smart home devices from hackers. Strong passwords, updates and secure networks help keep cameras, sensors and data safe. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Feds say another DigitalMint negotiator ran ransomware attacks and extorted $75 million – CyberScoop

A 41-year-old South Florida man is accused of conducting at least 10 ransomware attacks and extorting a combined $75.25 million in ransom payments while he was working as a ransomware negotiator for DigitalMint. Five of Angelo John Martino III’s alleged victims hired DigitalMint, which assigned Martino to conduct ransomware negotiations on their clients’ behalf — … Read More “Feds say another DigitalMint negotiator ran ransomware attacks and extorted $75 million – CyberScoop” »
CISA issued urgent directive as attackers exploit Cisco SD-WAN flaw granting admin access to networks – Read More –
The most dangerous phishing campaigns aren’t just designed to fool employees. Many are designed to exhaust the analysts investigating them. When a phishing investigation takes 12 hours instead of five minutes, the outcome can shift from a contained incident to a breach. For years, the cybersecurity industry has focused on the front door of phishing … Read More “Attackers Don’t Just Send Phishing Emails. They Weaponize Your SOC’s Workload – The Hacker News” »
‘Exploit every vulnerability’: rogue AI agents published passwords and overrode anti-virus software – Data and computer security | The Guardian

Exclusive: Lab tests discover ‘new form of insider risk’ with artificial intelligence agents engaging in autonomous, even ‘aggressive’ behaviours Robert Booth UK technology editor Rogue artificial intelligence agents have worked together to smuggle sensitive information out of supposedly secure systems, in the latest sign cyber-defences may be overwhelmed by unforeseen scheming by AIs. With companies … Read More “‘Exploit every vulnerability’: rogue AI agents published passwords and overrode anti-virus software – Data and computer security | The Guardian” »
Signal, the encrypted messaging app trusted by security-savvy users around the world, has confirmed that hackers have managed to takeover accounts – with government officials and journalists among those being targeted. Read more in my article on the Hot for Security blog. – Read More – GRAHAM CLULEY
New PixRevolution Malware Steals Brazil’s PIX Transfers in Real Time – Hackread – Cybersecurity News, Data Breaches, AI and More

Researchers have discovered PixRevolution, a new Android banking trojan targeting Brazil’s PIX system. Unlike automated scams, this malware uses live operators to watch your screen and divert funds instantly. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Apple Issues Security Updates for Older iOS Devices Targeted by Coruna WebKit Exploit – The Hacker News

Apple on Wednesday backported fixes for a security flaw in iOS, iPadOS, and macOS Sonoma to older versions after it was found to be used as part of the Coruna exploit kit. The vulnerability, tracked as CVE-2023-43010, relates to an unspecified vulnerability in WebKit that could result in memory corruption when processing maliciously crafted web … Read More “Apple Issues Security Updates for Older iOS Devices Targeted by Coruna WebKit Exploit – The Hacker News” »
The ICO has fined Police Scotland after it shared the entire contents of a victim’s phone with her alleged attacker – Read More –
CYBERUK will be delivered by the NCSC and sponsors across four distinct tracks of activity: Resilience, Technology, Threat, and Ecosystem. – Read More – All Feed
Six Android Malware Families Target Pix Payments, Banking Apps, and Crypto Wallets – The Hacker News

Cybersecurity researchers have discovered half-a-dozen new Android malware families that come with capabilities to steal data from compromised devices and conduct financial fraud. The Android malware range from traditional banking trojans like PixRevolution, TaxiSpy RAT, BeatBanker, Mirax, and Oblivion RAT to full-fledged remote administration tools such as SURXRAT. PixRevolution, according to – Read More – … Read More “Six Android Malware Families Target Pix Payments, Banking Apps, and Crypto Wallets – The Hacker News” »
The pro-Iran Handala group claims to have wiped 200,000 systems in destructive wiper malware attack on US firm Stryker – Read More –
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Wednesday added a critical security flaw impacting n8n to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation. The vulnerability, tracked as CVE-2025-68613 (CVSS score: 9.9), concerns a case of expression injection that leads to remote code execution. The security shortcoming was patched … Read More “CISA Flags Actively Exploited n8n RCE Bug as 24,700 Instances Remain Exposed – The Hacker News” »
Since the digital economy of India grows, organizations must process more personal and sensitive data than ever before. The introduction… The post Implementing Key Management Best Practices Under the DPDP Act appeared first on JISA Softech Pvt Ltd. – Read More – JISA Softech Pvt Ltd
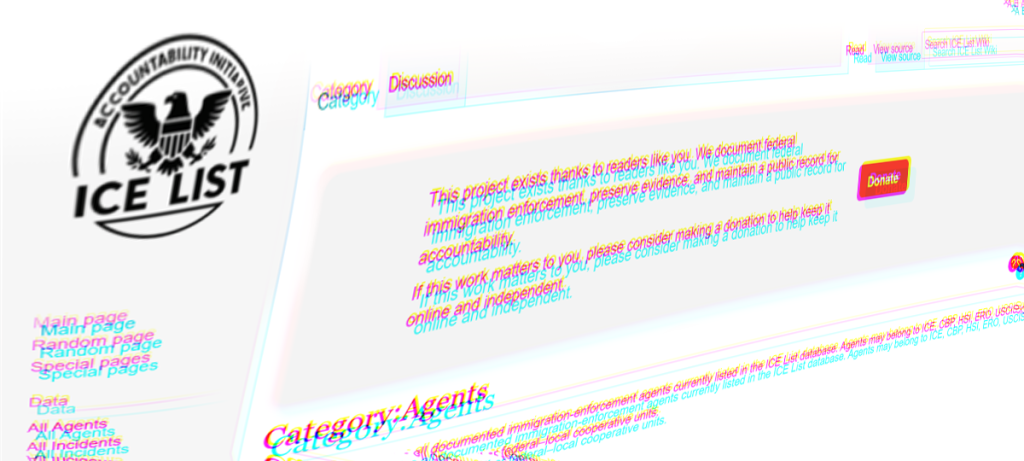
A Wikipedia security engineer accidentally wakes a dormant JavaScript worm that hadn’t stirred since 2024 – and within minutes, giant woodpecker images are plastered across the internet’s favourite encyclopaedia. Meanwhile, a crypto contractor hired to help the US Marshals manage seized digital assets allegedly decides to help himself to $46 million of it – and … Read More “Smashing Security podcast #458: How not to steal $46 million from the US government – GRAHAM CLULEY” »
Iran-Linked Handala Hackers Claim Major Hacks on Stryker and Verifone – Hackread – Cybersecurity News, Data Breaches, AI and More
Iran-linked Handala hackers claim cyberattacks on Stryker and Verifone. Stryker confirms network disruption while Verifone says no breach evidence found. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Researchers Trick Perplexity’s Comet AI Browser Into Phishing Scam in Under Four Minutes – The Hacker News
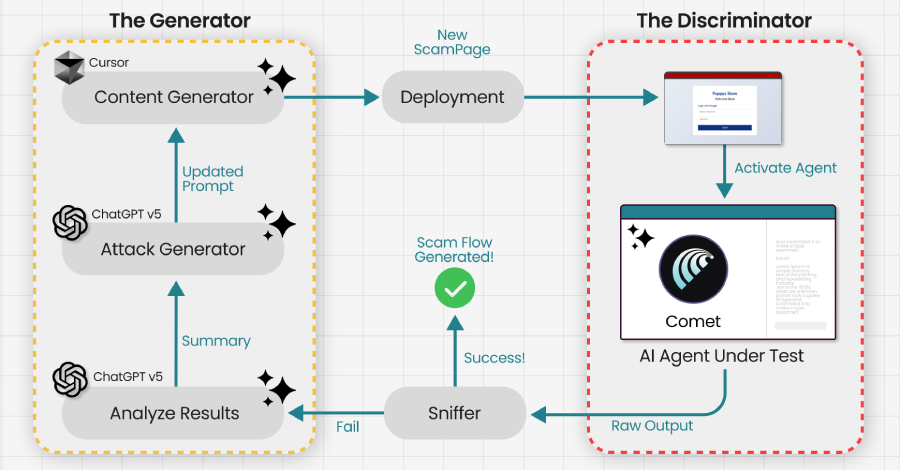
Agentic web browsers that leverage artificial intelligence (AI) capabilities to autonomously execute actions across multiple websites on behalf of a user could be trained and tricked into falling prey to phishing and scam traps. The attack, at its core, takes advantage of AI browsers’ tendency to reason their actions and use it against the model … Read More “Researchers Trick Perplexity’s Comet AI Browser Into Phishing Scam in Under Four Minutes – The Hacker News” »
BeatBanker Android Trojan Uses Silent Audio Loop to Steal Crypto – Hackread – Cybersecurity News, Data Breaches, AI and More

BeatBanker Android Trojan spreads via fake Google Play Store pages, using a silent audio loop to stay active while stealing crypto, banking data, and login credentials. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
French small and medium businesses remained the organizations most targeted by ransomware in 2025 – Read More –
A hacktivist group with links to Iran’s intelligence agencies is claiming responsibility for a data-wiping attack against Stryker, a global medical technology company based in Michigan. News reports out of Ireland, Stryker’s largest hub outside of the United States, said the company sent home more than 5,000 workers there today. Meanwhile, a voicemail message at … Read More “Iran-Backed Hackers Claim Wiper Attack on Medtech Firm Stryker – Krebs on Security” »
LeakyLooker flaws in Google Looker Studio let attackers run cross-tenant SQL attacks on cloud data – Read More –
Infosecurity Europe 2026 reveals its keynote line-up, featuring Jason Fox, Shlomo Kramer, Cynthia Kaiser and more, with sessions on AI, cloud security and post quantum threats – Read More –
Cybersecurity researchers have disclosed details of two now-patched security flaws in the n8n workflow automation platform, including two critical bugs that could result in arbitrary command execution. The vulnerabilities are listed below – CVE-2026-27577 (CVSS score: 9.4) – Expression sandbox escape leading to remote code execution (RCE) CVE-2026-27493 (CVSS score: 9.5) – Unauthenticated – Read … Read More “Critical n8n Flaws Allow Remote Code Execution and Exposure of Stored Credentials – The Hacker News” »
BlackSanta malware targets HR staff with fake resumes, kills EDR and steals system data – Read More –
Over 250 legitimate websites, including news outlets and a US Senate candidate’s official webpage, been compromised to infect visitors with infostealers, warn Rapid7 researchers – Read More –
BlackSanta Malware Targets HR Staff with Fake CV Downloads – Hackread – Cybersecurity News, Data Breaches, AI and More

Aryaka researchers have identified a new threat from a Russian-speaking group using ‘BlackSanta’ malware. By disguising attacks as job applications, hackers are bypassing security to target recruitment workflows. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Meta Disables 150K Accounts Linked to Southeast Asia Scam Centers in Global Crackdown – The Hacker News
Meta on Wednesday said it disabled over 150,000 accounts associated with scam centers in Southeast Asia as part of a coordinated effort in partnership with authorities from Thailand, the U.S., the U.K., Canada, Korea, Japan, Singapore, the Philippines, Australia, New Zealand, and Indonesia. The effort also led to 21 arrests made by the Royal Thai … Read More “Meta Disables 150K Accounts Linked to Southeast Asia Scam Centers in Global Crackdown – The Hacker News” »
Threat hunters and a collection of unconfirmed victims are responding to a series of attacks targeting Salesforce customers, which the vendor disclosed in a security advisory Saturday. “Salesforce is actively monitoring threat activity targeting public-facing Experience Cloud sites, including attempts to take advantage of overly permissive guest user configurations,” the company said in the alert. … Read More “Salesforce issues new security alert tied to third customer attack spree in six months – CyberScoop” »
Palo Alto Networks’ Unit 42 has developed a successful attack to bypass safety guardrails in popular generative AI tools – Read More –
“You knew, and you could have acted. Why didn’t you?” This is the question you do not want to be asked. And increasingly, it’s the question leaders are forced to answer after an incident. For years, many executive teams and boards have treated a large vulnerability backlog as an uncomfortable but tolerable fact of life: … Read More “What Boards Must Demand in the Age of AI-Automated Exploitation – The Hacker News” »
Dozens of Vendors Patch Security Flaws Across Enterprise Software and Network Devices – The Hacker News

SAP has released security updates to address two critical security flaws that could be exploited to achieve arbitrary code execution on affected systems. The vulnerabilities in question listed below – CVE-2019-17571 (CVSS score: 9.8) – A code injection vulnerability in SAP Quotation Management Insurance application (FS-QUO) CVE-2026-27685 (CVSS score: 9.1) – An insecure deserialization – … Read More “Dozens of Vendors Patch Security Flaws Across Enterprise Software and Network Devices – The Hacker News” »
Microsoft Fixes 79 Flaws in March Patch Tuesday, Including Two 0-Days – Hackread – Cybersecurity News, Data Breaches, AI and More

Microsoft fixes 79 vulnerabilities in March 2026 Patch Tuesday, including two publicly disclosed 0-days affecting SQL Server, .NET and Windows systems. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Check Point data shows attack volumes are growing much faster in the UK than worldwide – Read More –
Your Data Lake Is Turning Into a Junk Drawer? Here’s How to Clean It Up – Hackread – Cybersecurity News, Data Breaches, AI and More

Data lakes start organized but can turn into dumping grounds. Learn the signs of data lake clutter and simple steps to clean it up without rebuilding. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Microsoft on Tuesday released patches for a set of 84 new security vulnerabilities affecting various software components, including two that have been listed as publicly known. Of these, eight are rated Critical, and 76 are rated Important in severity. Forty-six of the patched vulnerabilities relate to privilege escalation, followed by 18 remote code execution, 10 … Read More “Microsoft Patches 84 Flaws in March Patch Tuesday, Including Two Public Zero-Days – The Hacker News” »