A new exploit kit for Apple iOS devices designed to steal sensitive data from is being wielded by multiple threat actors since at least November 2025, according to reports from Google Threat Intelligence Group (GTIG), iVerify, and Lookout. According to GTIG, multiple commercial surveillance vendors and suspected state-sponsored actors have utilized the full-chain exploit kit, … Read More “DarkSword iOS Exploit Kit Uses 6 Flaws, 3 Zero-Days for Full Device Takeover – The Hacker News” »
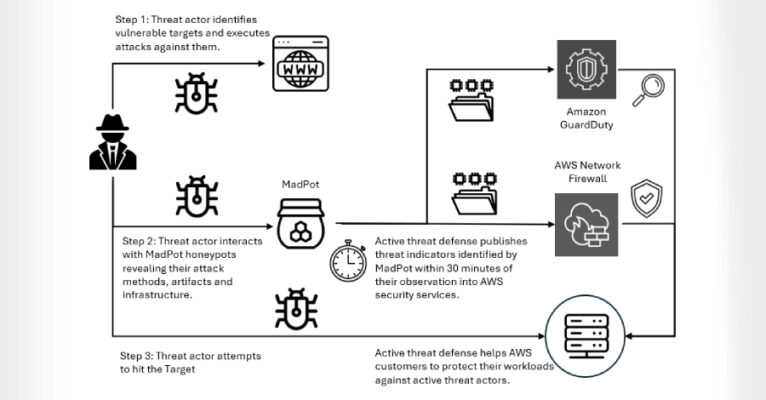
Notorious ransomware group Interlock has been exploiting a Cisco zero-day bug since January, AWS says – Read More –
The UK’s financial regulator has issued new rules to make incident and third-party reporting clearer – Read More –
35% of security leaders working in the UK’s critical infrastructure said regulatory requirements are the primary influence on their security programs – Read More –
CISA Warns of Zimbra, SharePoint Flaw Exploits; Cisco Zero-Day Hit in Ransomware Attacks – The Hacker News

The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has urged government agencies to apply patches for two security flaws impacting Synacor Zimbra Collaboration Suite (ZCS) and Microsoft Office SharePoint, stating they have been actively exploited in the wild. The vulnerabilities in question are as follows – CVE-2025-66376 (CVSS score: 7.2) – A stored cross-site scripting … Read More “CISA Warns of Zimbra, SharePoint Flaw Exploits; Cisco Zero-Day Hit in Ransomware Attacks – The Hacker News” »
In episode 459 of Smashing Security, we dive into a chillingly clever account takeover attempt targeting WordPress co-founder Matt Mullenweg – involving MFA fatigue, real Apple alerts, a convincing support call, and a phishing page that oh-so-nearly worked. If a famous techie could have this happen to you, can you be sure you’re immune? Plus: … Read More “Smashing Security podcast #459: This clever scam nearly hijacked a tech CEO’s Apple ID – GRAHAM CLULEY” »
Computer Vision Frameworks: Features And Future Trends – Hackread – Cybersecurity News, Data Breaches, AI and More
Computer vision frameworks explained, features, types, and future trends. Learn how AI tools process images, train models, and… – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Cisco customers have confronted a flood of actively exploited vulnerabilities affecting the vendor’s network edge software since late February, and researchers say that five of the nine vulnerabilities Cisco disclosed in its firewalls and SD-WAN systems over the past three weeks have already been exploited in the wild. Attackers exploited a pair of these defects … Read More “Cisco’s latest vulnerability spree has a more troubling pattern underneath – CyberScoop” »
U.S. robotics companies want federal help to keep Chinese robots out of America’s networks – CyberScoop

Executives at top U.S. robotics companies asked Congress for federal dollars, new legislation and a simpler regulatory field, arguing the support is necessary to adapt to the AI era and compete with their well-oiled, state-funded Chinese competitors. The U.S. robotics sector, estimated at $50 billion in value, includes world famous companies like Boston Dynamics. The … Read More “U.S. robotics companies want federal help to keep Chinese robots out of America’s networks – CyberScoop” »
“Claudy Day” Flaws Allow Data Theft via Fake Claude AI Ads, Report – Hackread – Cybersecurity News, Data Breaches, AI and More

Researchers detail “Claudy Day” flaws in Claude AI that could enable data theft using fake Google Ads, hidden… – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
OFAC Sanctions DPRK IT Worker Network Funding WMD Programs Through Fake Remote Jobs – The Hacker News

The U.S. Department of the Treasury’s Office of Foreign Assets Control (OFAC) has sanctioned six individuals and two entities for their involvement in the Democratic People’s Republic of Korea (DPRK) information technology (IT) worker scheme with an aim to defraud U.S. businesses and generate illicit revenue for the regime to fund its weapons of mass … Read More “OFAC Sanctions DPRK IT Worker Network Funding WMD Programs Through Fake Remote Jobs – The Hacker News” »
Amazon Threat Intelligence is warning of an active Interlock ransomware campaign that’s exploiting a recently disclosed critical security flaw in Cisco Secure Firewall Management Center (FMC) Software. The vulnerability in question is CVE-2026-20131 (CVSS score: 10.0), a case of insecure deserialization of user-supplied Java byte stream, which could allow an unauthenticated, remote attacker to – … Read More “Interlock Ransomware Exploits Cisco FMC Zero-Day CVE-2026-20131 for Root Access – The Hacker News” »
CVE-2026-3888 Ubuntu snap flaw lets local users escalate to root via timing-based exploit – Read More –
ShieldGuard Chrome extension posed as a crypto security tool but stole wallets and drained user data – Read More –
New .NET AOT Malware Hides Code as a Black Box to Evade Detection – Hackread – Cybersecurity News, Data Breaches, AI and More
Researchers at Howler Cell have discovered a new .NET AOT malware campaign that uses a clever scoring system… – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Second iOS exploit kit emerges from suspected Russian hackers using possible U.S. government-developed tools – CyberScoop

Researchers have discovered a second instance of suspected Russian hackers repurposing iOS exploits believed to originally be made on behalf of the U.S. government, pointing to what they say are several foreboding trends. iVerify, Lookout and Google collaborated on the research published Wednesday, a follow-up to earlier revelations about a similar exploit kit, Coruna. While … Read More “Second iOS exploit kit emerges from suspected Russian hackers using possible U.S. government-developed tools – CyberScoop” »
Rapid7 says median time from publication to CISA KEV inclusion dropped to five days – Read More –
Cybersecurity researchers have warned about the risks posed by low-cost IP KVM (Keyboard, Video, Mouse over Internet Protocol) devices, which can grant attackers extensive control over compromised hosts. The nine vulnerabilities, discovered by Eclypsium, span four different products from GL-iNet Comet RM-1, Angeet/Yeeso ES3 KVM, Sipeed NanoKVM, and JetKVM. The most severe of them allow … Read More “9 Critical IP KVM Flaws Enable Unauthenticated Root Access Across Four Vendors – The Hacker News” »
When a Magecart payload hides inside the EXIF data of a dynamically loaded third-party favicon, no repository scanner will catch it – because the malicious code never actually touches your repo. As teams adopt Claude Code Security for static analysis, this is the exact technical boundary where AI code scanning stops and client-side runtime execution … Read More “Claude Code Security and Magecart: Getting the Threat Model Right – The Hacker News” »
New ClickFix Scam Tricks Users Into Mapping Hacker-Controlled Drives – Hackread – Cybersecurity News, Data Breaches, AI and More
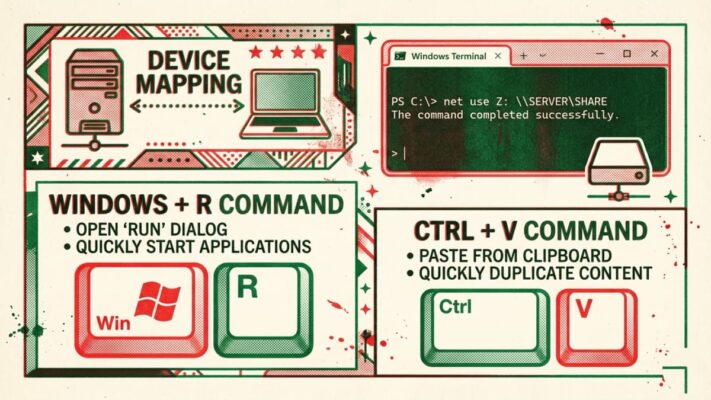
A new ClickFix scam tricks Windows users into running hidden commands that map hacker-controlled drives and load malware… – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Product Walkthrough: How Mesh CSMA Reveals and Breaks Attack Paths to Crown Jewels – The Hacker News

Security teams today are not short on tools or data. They are overwhelmed by both. Yet within the terabytes of alerts, exposures, and misconfigurations – security teams still struggle to understand context: Q: Which exposures, misconfigurations, and vulnerabilities chain together to create viable attack paths to crown jewels? Even the most mature security teams can’t … Read More “Product Walkthrough: How Mesh CSMA Reveals and Breaks Attack Paths to Crown Jewels – The Hacker News” »
The Vidar 2.0 infostealers is deployed through fake free game cheats on GitHub and Reddit – Read More –
Ubuntu CVE-2026-3888 Bug Lets Attackers Gain Root via systemd Cleanup Timing Exploit – The Hacker News

A high-severity security flaw affecting default installations of Ubuntu Desktop versions 24.04 and later could be exploited to escalate privileges to the root level. Tracked as CVE-2026-3888 (CVSS score: 7.8), the issue could allow an attacker to seize control of a susceptible system. “This flaw (CVE-2026-3888) allows an unprivileged local attacker to escalate privileges to … Read More “Ubuntu CVE-2026-3888 Bug Lets Attackers Gain Root via systemd Cleanup Timing Exploit – The Hacker News” »
Gartner has urged security teams to get involved in AI projects from the start to avoid costly incident response – Read More –
Apple Fixes WebKit Vulnerability Enabling Same-Origin Policy Bypass on iOS and macOS – The Hacker News

Apple on Tuesday released its first round of Background Security Improvements to address a security flaw in WebKit that affects iOS, iPadOS, and macOS. The vulnerability, tracked as CVE-2026-20643 (CVSS score: N/A), has been described as a cross-origin issue in WebKit’s Navigation API that could be exploited to bypass the same-origin policy when processing maliciously … Read More “Apple Fixes WebKit Vulnerability Enabling Same-Origin Policy Bypass on iOS and macOS – The Hacker News” »
Critical Unpatched Telnetd Flaw (CVE-2026-32746) Enables Unauthenticated Root RCE via Port 23 – The Hacker News
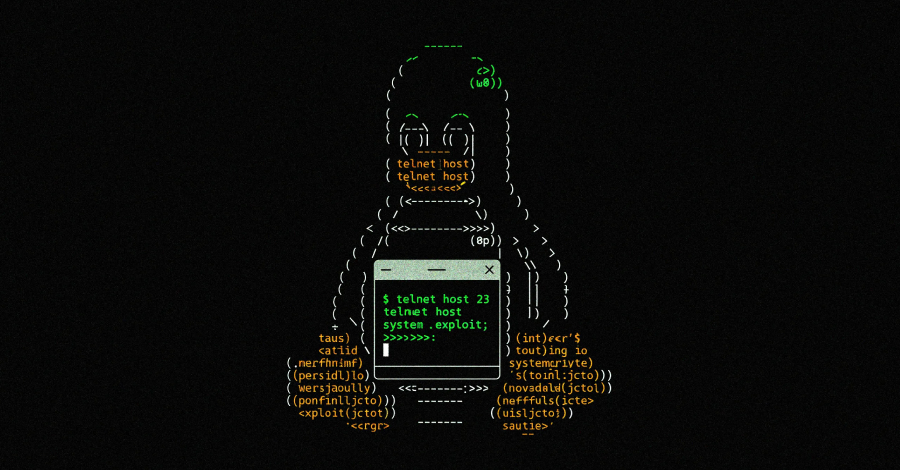
Cybersecurity researchers have disclosed a critical security flaw impacting the GNU InetUtils telnet daemon (telnetd) that could be exploited by an unauthenticated remote attacker to execute arbitrary code with elevated privileges. The vulnerability, tracked as CVE-2026-32746, carries a CVSS score of 9.8 out of 10.0. It has been described as a case of out-of-bounds write … Read More “Critical Unpatched Telnetd Flaw (CVE-2026-32746) Enables Unauthenticated Root RCE via Port 23 – The Hacker News” »
Database Activity Monitoring (DAM) for DPDP & SOC Alignment: Strengthening Data Protection and Insider Threat Detection – JISA Softech Pvt Ltd
With organizations more and more becoming data-driven, databases have become the cornerstone of the current digital ecosystem. There are financial records, healthcare… The post Database Activity Monitoring (DAM) for DPDP & SOC Alignment: Strengthening Data Protection and Insider Threat Detection appeared first on JISA Softech Pvt Ltd. – Read More – JISA Softech Pvt Ltd
Storm-2561 Uses Fake Fortinet, Ivanti VPN Sites to Drop Hyrax Infostealer – Hackread – Cybersecurity News, Data Breaches, AI and More
In mid-January 2026, Microsoft Defender Experts identified a devious way that cybercriminals are tricking people into giving away… – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
CISA official advises agencies not to get too hung up on who takes lead in critical infrastructure sectors – CyberScoop

The U.S. government shouldn’t rigidly stick to traditional designations about which agency takes the lead on engaging with critical infrastructure sectors, the acting director of the Cybersecurity and Infrastructure Security Agency said Tuesday. Sector risk management agency designations have long governed which agency is at the forefront of government efforts to protect each of the … Read More “CISA official advises agencies not to get too hung up on who takes lead in critical infrastructure sectors – CyberScoop” »
Appeals court temporarily pauses order blocking Perplexity’s AI shopping agent on Amazon – CyberScoop

A federal appeals court has temporarily put on hold a California judge’s order that would have blocked Perplexity AI from using an AI-powered shopping agent on Amazon, as the case moves forward in a dispute over who controls automated activity inside customer accounts. The Ninth U.S. Circuit Court of Appeals on Monday granted Perplexity an … Read More “Appeals court temporarily pauses order blocking Perplexity’s AI shopping agent on Amazon – CyberScoop” »
Trump administration isn’t pushing companies to conduct cyber offense, national cyber director says – CyberScoop

National Cyber Director Sean Cairncross said Tuesday that the Trump administration isn’t aspiring to enlist the private sector to conduct offensive cyber operations, but instead to help the government by keeping them abreast of the threats they’re facing. The recently-released national cyber strategy talks about incentivizing companies to disrupt the networks of adversaries. “I’m not … Read More “Trump administration isn’t pushing companies to conduct cyber offense, national cyber director says – CyberScoop” »
ClickFix Attack Targets Devs with MacSync Malware via Fake Claude Tools – Hackread – Cybersecurity News, Data Breaches, AI and More
Cybersecurity researchers at 7AI have revealed a new Claude Fraud campaign in which hackers use fake AI extensions and Google ads to steal data from tech professionals. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
AI Flaws in Amazon Bedrock, LangSmith, and SGLang Enable Data Exfiltration and RCE – The Hacker News

Cybersecurity researchers have disclosed details of a new method for exfiltrating sensitive data from artificial intelligence (AI) code execution environments using domain name system (DNS) queries. In a report published Monday, BeyondTrust revealed that Amazon Bedrock AgentCore Code Interpreter’s sandbox mode permits outbound DNS queries that an attacker can exploit to enable interactive shells – … Read More “AI Flaws in Amazon Bedrock, LangSmith, and SGLang Enable Data Exfiltration and RCE – The Hacker News” »
Android’s LSPosed-based attack hijacks payment apps via runtime manipulation and SIM-binding bypass – Read More –
Orchid Security Recognized by Gartner® as a Representative Vendor of Guardian Agents – Hackread – Cybersecurity News, Data Breaches, AI and More

New York, United States, 17th March 2026, CyberNewswire – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Enterprise Cloud Network Solutions for Multi-Cloud Environments: Top Platforms – Hackread – Cybersecurity News, Data Breaches, AI and More

Enterprise Cloud Network Solutions secure multi-cloud environments with Zero Trust, visibility, and threat prevention across users, apps, and distributed data systems. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
The ransomware operation known as LeakNet has adopted the ClickFix social engineering tactic delivered through compromised websites as an initial access method. The use of ClickFix, where users are tricked into manually running malicious commands to address non-existent errors, is a departure from relying on traditional methods for obtaining initial access, such as through stolen … Read More “LeakNet Ransomware Uses ClickFix via Hacked Sites, Deploys Deno In-Memory Loader – The Hacker News” »
CursorJack shows how malicious MCP deeplinks in Cursor IDE can trigger user-approved code execution – Read More –
New Vidar 2.0 Infostealer Spreads via Fake Game Cheats on GitHub, Reddit – Hackread – Cybersecurity News, Data Breaches, AI and More

The new infostealer campaign spreads Vidar 2.0 via fake game cheats on GitHub and Reddit, stealing crypto, login tokens, and files while targeting young gamers ignoring security warnings – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
GitGuardian Reports an 81% Surge of AI-Service Leaks as 29M Secrets Hit Public GitHub – Hackread – Cybersecurity News, Data Breaches, AI and More
New York, NY, 17th March 2026, CyberNewswire – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Armis reveals that “mutually assured disruption” is no longer preventing state-backed attacks – Read More –
AI is Everywhere, But CISOs are Still Securing It with Yesterday’s Skills and Tools, Study Finds – The Hacker News
A majority of security leaders are struggling to defend AI systems with tools and skills that are not fit for the challenge, according to the AI and Adversarial Testing Benchmark Report 2026 from Pentera. The report, based on a survey of 300 US CISOs and senior security leaders, examines how organizations are securing AI infrastructure … Read More “AI is Everywhere, But CISOs are Still Securing It with Yesterday’s Skills and Tools, Study Finds – The Hacker News” »
Free parking in Russia after Distributed Denial-of-Service attack knocks city’s parking system offline – GRAHAM CLULEY

Drivers in the Russian city of Perm have been enjoying an unexpected bonus this week: free parking. Not because the city council suddenly decided to embrace generosity – but rather because hackers succeeded in knocking the city’s payment system offline. Read more in my article on the Hot for Security blog. – Read More – … Read More “Free parking in Russia after Distributed Denial-of-Service attack knocks city’s parking system offline – GRAHAM CLULEY” »
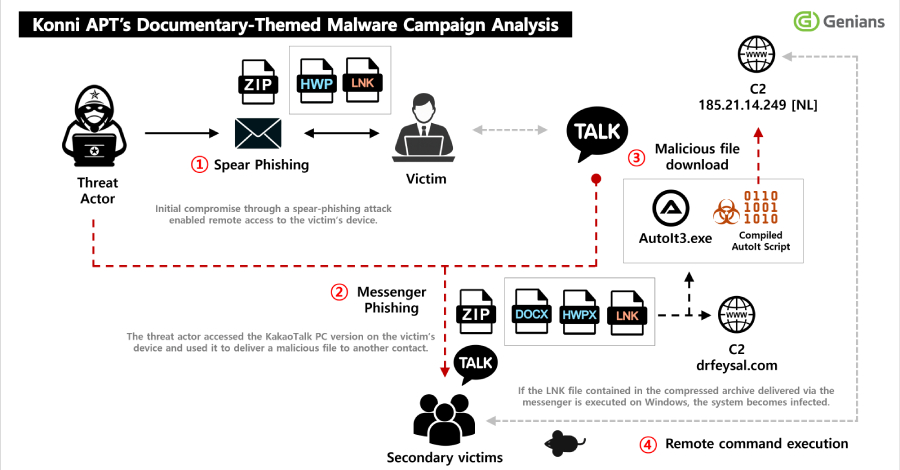
North Korean threat actors have been observed sending phishing to compromise targets and obtain access to a victim’s KakaoTalk desktop application to distribute malicious payloads to certain contacts. The activity has been attributed by South Korean threat intelligence firm Genians to a hacking group referred to as Konni. “Initial access was achieved through a spear-phishing … Read More “Konni Deploys EndRAT Through Phishing, Uses KakaoTalk to Propagate Malware – The Hacker News” »
After decades of development, quantum computing is now becoming increasingly available for advanced scientific and commercial use. The potential marvels range from accelerating drug discovery and materials science, to optimizing complex logistics and financial modeling. But there’s a paradox to this trend: Quantum computing also poses a growing threat to data security. The risk is … Read More “It’s time to get serious about post-quantum security. Here’s where to start. – CyberScoop” »
The US Cyber Monitoring Center should be operational in 2027, said the UK CMC leadership – Read More –
Akamai says 87% of organizations suffered an API-related security incident last year – Read More –
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added a medium-severity security flaw impacting Wing FTP to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation. The vulnerability, CVE-2025-47813 (CVSS score: 4.3), is an information disclosure vulnerability that leaks the installation path of the application under certain conditions – Read More … Read More “CISA Flags Actively Exploited Wing FTP Vulnerability Leaking Server Paths – The Hacker News” »
UPDATE: Ant Group Censors 4 Security Research Articles After Initial Complaint Rejection – Full Disclosure

Posted by Jiqiang Feng via Fulldisclosure on Mar 16 [This is an update to communications sent March 12-14 regarding Alipay security vulnerabilities.] — On March 15, 2026, four WeChat articles documenting security vulnerabilities in Alipay were forcibly deleted from the public account AI-security-innora. The deletion was carried out by Tencent at the request of … Read More “UPDATE: Ant Group Censors 4 Security Research Articles After Initial Complaint Rejection – Full Disclosure” »
The healthcare ecosystem is currently experiencing a fast-paced shift toward digital technology. The healthcare system now depends on electronic… The post Protecting PHI: Architecture Blueprint for Hospitals & Healthtech appeared first on JISA Softech Pvt Ltd. – Read More – JISA Softech Pvt Ltd