Cybersecurity researchers have warned about the risks posed by low-cost IP KVM (Keyboard, Video, Mouse over Internet Protocol) devices, which can grant attackers extensive control over compromised hosts. The nine vulnerabilities, discovered by Eclypsium, span four different products from GL-iNet Comet RM-1, Angeet/Yeeso ES3 KVM, Sipeed NanoKVM, and JetKVM. The most severe of them allow … Read More “9 Critical IP KVM Flaws Enable Unauthenticated Root Access Across Four Vendors – The Hacker News” »
When a Magecart payload hides inside the EXIF data of a dynamically loaded third-party favicon, no repository scanner will catch it – because the malicious code never actually touches your repo. As teams adopt Claude Code Security for static analysis, this is the exact technical boundary where AI code scanning stops and client-side runtime execution … Read More “Claude Code Security and Magecart: Getting the Threat Model Right – The Hacker News” »
New ClickFix Scam Tricks Users Into Mapping Hacker-Controlled Drives – Hackread – Cybersecurity News, Data Breaches, AI and More
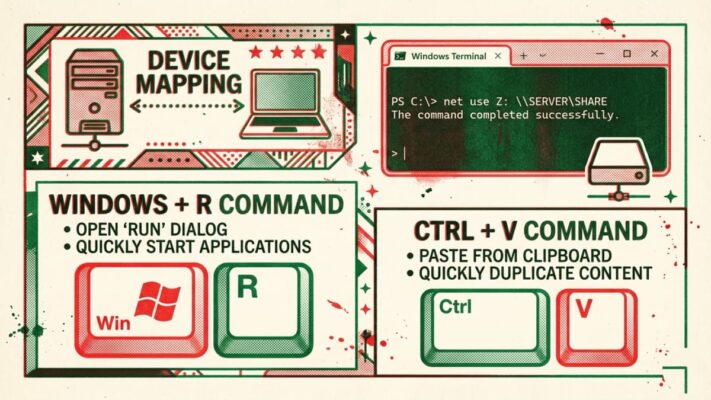
A new ClickFix scam tricks Windows users into running hidden commands that map hacker-controlled drives and load malware… – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Product Walkthrough: How Mesh CSMA Reveals and Breaks Attack Paths to Crown Jewels – The Hacker News

Security teams today are not short on tools or data. They are overwhelmed by both. Yet within the terabytes of alerts, exposures, and misconfigurations – security teams still struggle to understand context: Q: Which exposures, misconfigurations, and vulnerabilities chain together to create viable attack paths to crown jewels? Even the most mature security teams can’t … Read More “Product Walkthrough: How Mesh CSMA Reveals and Breaks Attack Paths to Crown Jewels – The Hacker News” »
The Vidar 2.0 infostealers is deployed through fake free game cheats on GitHub and Reddit – Read More –
Ubuntu CVE-2026-3888 Bug Lets Attackers Gain Root via systemd Cleanup Timing Exploit – The Hacker News

A high-severity security flaw affecting default installations of Ubuntu Desktop versions 24.04 and later could be exploited to escalate privileges to the root level. Tracked as CVE-2026-3888 (CVSS score: 7.8), the issue could allow an attacker to seize control of a susceptible system. “This flaw (CVE-2026-3888) allows an unprivileged local attacker to escalate privileges to … Read More “Ubuntu CVE-2026-3888 Bug Lets Attackers Gain Root via systemd Cleanup Timing Exploit – The Hacker News” »
Gartner has urged security teams to get involved in AI projects from the start to avoid costly incident response – Read More –
Apple Fixes WebKit Vulnerability Enabling Same-Origin Policy Bypass on iOS and macOS – The Hacker News

Apple on Tuesday released its first round of Background Security Improvements to address a security flaw in WebKit that affects iOS, iPadOS, and macOS. The vulnerability, tracked as CVE-2026-20643 (CVSS score: N/A), has been described as a cross-origin issue in WebKit’s Navigation API that could be exploited to bypass the same-origin policy when processing maliciously … Read More “Apple Fixes WebKit Vulnerability Enabling Same-Origin Policy Bypass on iOS and macOS – The Hacker News” »
Critical Unpatched Telnetd Flaw (CVE-2026-32746) Enables Unauthenticated Root RCE via Port 23 – The Hacker News
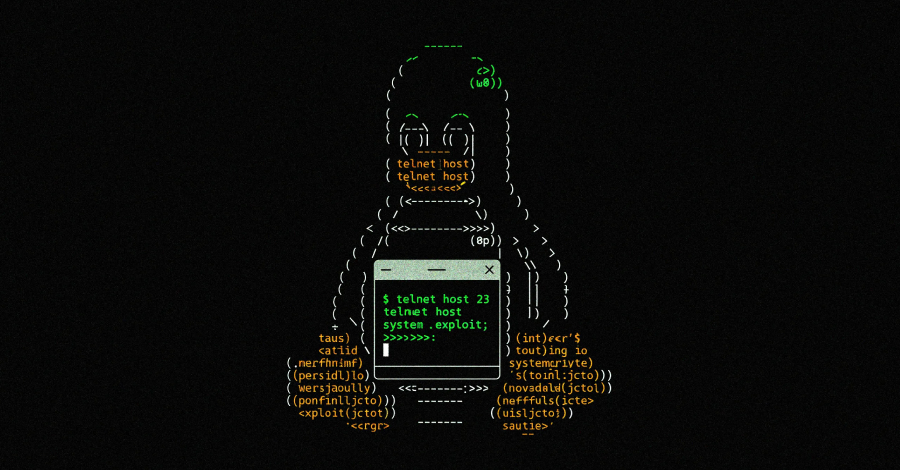
Cybersecurity researchers have disclosed a critical security flaw impacting the GNU InetUtils telnet daemon (telnetd) that could be exploited by an unauthenticated remote attacker to execute arbitrary code with elevated privileges. The vulnerability, tracked as CVE-2026-32746, carries a CVSS score of 9.8 out of 10.0. It has been described as a case of out-of-bounds write … Read More “Critical Unpatched Telnetd Flaw (CVE-2026-32746) Enables Unauthenticated Root RCE via Port 23 – The Hacker News” »
Database Activity Monitoring (DAM) for DPDP & SOC Alignment: Strengthening Data Protection and Insider Threat Detection – JISA Softech Pvt Ltd
With organizations more and more becoming data-driven, databases have become the cornerstone of the current digital ecosystem. There are financial records, healthcare… The post Database Activity Monitoring (DAM) for DPDP & SOC Alignment: Strengthening Data Protection and Insider Threat Detection appeared first on JISA Softech Pvt Ltd. – Read More – JISA Softech Pvt Ltd
Storm-2561 Uses Fake Fortinet, Ivanti VPN Sites to Drop Hyrax Infostealer – Hackread – Cybersecurity News, Data Breaches, AI and More
In mid-January 2026, Microsoft Defender Experts identified a devious way that cybercriminals are tricking people into giving away… – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
CISA official advises agencies not to get too hung up on who takes lead in critical infrastructure sectors – CyberScoop

The U.S. government shouldn’t rigidly stick to traditional designations about which agency takes the lead on engaging with critical infrastructure sectors, the acting director of the Cybersecurity and Infrastructure Security Agency said Tuesday. Sector risk management agency designations have long governed which agency is at the forefront of government efforts to protect each of the … Read More “CISA official advises agencies not to get too hung up on who takes lead in critical infrastructure sectors – CyberScoop” »
Appeals court temporarily pauses order blocking Perplexity’s AI shopping agent on Amazon – CyberScoop

A federal appeals court has temporarily put on hold a California judge’s order that would have blocked Perplexity AI from using an AI-powered shopping agent on Amazon, as the case moves forward in a dispute over who controls automated activity inside customer accounts. The Ninth U.S. Circuit Court of Appeals on Monday granted Perplexity an … Read More “Appeals court temporarily pauses order blocking Perplexity’s AI shopping agent on Amazon – CyberScoop” »
Trump administration isn’t pushing companies to conduct cyber offense, national cyber director says – CyberScoop

National Cyber Director Sean Cairncross said Tuesday that the Trump administration isn’t aspiring to enlist the private sector to conduct offensive cyber operations, but instead to help the government by keeping them abreast of the threats they’re facing. The recently-released national cyber strategy talks about incentivizing companies to disrupt the networks of adversaries. “I’m not … Read More “Trump administration isn’t pushing companies to conduct cyber offense, national cyber director says – CyberScoop” »
ClickFix Attack Targets Devs with MacSync Malware via Fake Claude Tools – Hackread – Cybersecurity News, Data Breaches, AI and More
Cybersecurity researchers at 7AI have revealed a new Claude Fraud campaign in which hackers use fake AI extensions and Google ads to steal data from tech professionals. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
AI Flaws in Amazon Bedrock, LangSmith, and SGLang Enable Data Exfiltration and RCE – The Hacker News

Cybersecurity researchers have disclosed details of a new method for exfiltrating sensitive data from artificial intelligence (AI) code execution environments using domain name system (DNS) queries. In a report published Monday, BeyondTrust revealed that Amazon Bedrock AgentCore Code Interpreter’s sandbox mode permits outbound DNS queries that an attacker can exploit to enable interactive shells – … Read More “AI Flaws in Amazon Bedrock, LangSmith, and SGLang Enable Data Exfiltration and RCE – The Hacker News” »
Android’s LSPosed-based attack hijacks payment apps via runtime manipulation and SIM-binding bypass – Read More –
Orchid Security Recognized by Gartner® as a Representative Vendor of Guardian Agents – Hackread – Cybersecurity News, Data Breaches, AI and More

New York, United States, 17th March 2026, CyberNewswire – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Enterprise Cloud Network Solutions for Multi-Cloud Environments: Top Platforms – Hackread – Cybersecurity News, Data Breaches, AI and More

Enterprise Cloud Network Solutions secure multi-cloud environments with Zero Trust, visibility, and threat prevention across users, apps, and distributed data systems. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
The ransomware operation known as LeakNet has adopted the ClickFix social engineering tactic delivered through compromised websites as an initial access method. The use of ClickFix, where users are tricked into manually running malicious commands to address non-existent errors, is a departure from relying on traditional methods for obtaining initial access, such as through stolen … Read More “LeakNet Ransomware Uses ClickFix via Hacked Sites, Deploys Deno In-Memory Loader – The Hacker News” »
CursorJack shows how malicious MCP deeplinks in Cursor IDE can trigger user-approved code execution – Read More –
New Vidar 2.0 Infostealer Spreads via Fake Game Cheats on GitHub, Reddit – Hackread – Cybersecurity News, Data Breaches, AI and More

The new infostealer campaign spreads Vidar 2.0 via fake game cheats on GitHub and Reddit, stealing crypto, login tokens, and files while targeting young gamers ignoring security warnings – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
GitGuardian Reports an 81% Surge of AI-Service Leaks as 29M Secrets Hit Public GitHub – Hackread – Cybersecurity News, Data Breaches, AI and More
New York, NY, 17th March 2026, CyberNewswire – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Armis reveals that “mutually assured disruption” is no longer preventing state-backed attacks – Read More –
AI is Everywhere, But CISOs are Still Securing It with Yesterday’s Skills and Tools, Study Finds – The Hacker News
A majority of security leaders are struggling to defend AI systems with tools and skills that are not fit for the challenge, according to the AI and Adversarial Testing Benchmark Report 2026 from Pentera. The report, based on a survey of 300 US CISOs and senior security leaders, examines how organizations are securing AI infrastructure … Read More “AI is Everywhere, But CISOs are Still Securing It with Yesterday’s Skills and Tools, Study Finds – The Hacker News” »
Free parking in Russia after Distributed Denial-of-Service attack knocks city’s parking system offline – GRAHAM CLULEY

Drivers in the Russian city of Perm have been enjoying an unexpected bonus this week: free parking. Not because the city council suddenly decided to embrace generosity – but rather because hackers succeeded in knocking the city’s payment system offline. Read more in my article on the Hot for Security blog. – Read More – … Read More “Free parking in Russia after Distributed Denial-of-Service attack knocks city’s parking system offline – GRAHAM CLULEY” »
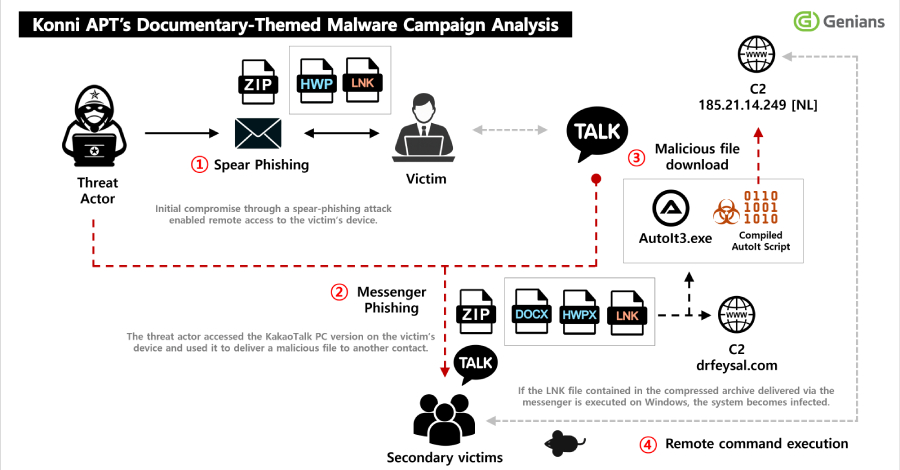
North Korean threat actors have been observed sending phishing to compromise targets and obtain access to a victim’s KakaoTalk desktop application to distribute malicious payloads to certain contacts. The activity has been attributed by South Korean threat intelligence firm Genians to a hacking group referred to as Konni. “Initial access was achieved through a spear-phishing … Read More “Konni Deploys EndRAT Through Phishing, Uses KakaoTalk to Propagate Malware – The Hacker News” »
After decades of development, quantum computing is now becoming increasingly available for advanced scientific and commercial use. The potential marvels range from accelerating drug discovery and materials science, to optimizing complex logistics and financial modeling. But there’s a paradox to this trend: Quantum computing also poses a growing threat to data security. The risk is … Read More “It’s time to get serious about post-quantum security. Here’s where to start. – CyberScoop” »
The US Cyber Monitoring Center should be operational in 2027, said the UK CMC leadership – Read More –
Akamai says 87% of organizations suffered an API-related security incident last year – Read More –
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added a medium-severity security flaw impacting Wing FTP to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation. The vulnerability, CVE-2025-47813 (CVSS score: 4.3), is an information disclosure vulnerability that leaks the installation path of the application under certain conditions – Read More … Read More “CISA Flags Actively Exploited Wing FTP Vulnerability Leaking Server Paths – The Hacker News” »
UPDATE: Ant Group Censors 4 Security Research Articles After Initial Complaint Rejection – Full Disclosure

Posted by Jiqiang Feng via Fulldisclosure on Mar 16 [This is an update to communications sent March 12-14 regarding Alipay security vulnerabilities.] — On March 15, 2026, four WeChat articles documenting security vulnerabilities in Alipay were forcibly deleted from the public account AI-security-innora. The deletion was carried out by Tencent at the request of … Read More “UPDATE: Ant Group Censors 4 Security Research Articles After Initial Complaint Rejection – Full Disclosure” »
The healthcare ecosystem is currently experiencing a fast-paced shift toward digital technology. The healthcare system now depends on electronic… The post Protecting PHI: Architecture Blueprint for Hospitals & Healthtech appeared first on JISA Softech Pvt Ltd. – Read More – JISA Softech Pvt Ltd
Researchers Find Data Leak Risk in AWS Bedrock AI Code Interpreter – Hackread – Cybersecurity News, Data Breaches, AI and More
AWS Bedrock AI tool flaw allows data leaks via DNS queries in AgentCore Code Interpreter sandbox, exposing sensitive cloud data, researchers warn. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
FBI Investigates Steam Games Linked to Malware and Crypto Wallet Theft – Hackread – Cybersecurity News, Data Breaches, AI and More

FBI warns gamers after malware hidden in several Steam games stole browser data and drained cryptocurrency wallets between May 2024 and January 2026. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Zero lessons learned: Convicted scammer allegedly ran another athlete-focused phishing scam from federal prison – CyberScoop

Professional NBA and NFL athletes were allegedly deceived and victimized by a 34-year-old Georgia man’s sneaky social-engineering scheme that he ran while impersonating a well-known adult film star, the Justice Department said Monday. Kwamaine Jerell Ford allegedly initiated and committed some of the crimes while incarcerated in federal prison for a similar, widespread phishing scam … Read More “Zero lessons learned: Convicted scammer allegedly ran another athlete-focused phishing scam from federal prison – CyberScoop” »
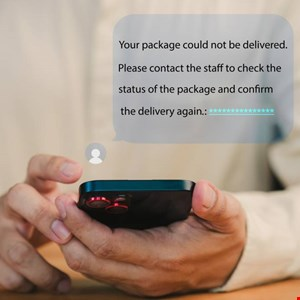
New Phishing Scam Uses LiveChat to Pose as Amazon and PayPal in Real Time – Hackread – Cybersecurity News, Data Breaches, AI and More

Cofense researchers warn of a phishing scam where attackers use LiveChat to impersonate Amazon and PayPal agents and steal credit card and MFA codes. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
GlassWorm Attack Uses Stolen GitHub Tokens to Force-Push Malware Into Python Repos – The Hacker News
The GlassWorm malware campaign is being used to fuel an ongoing attack that leverages the stolen GitHub tokens to inject malware into hundreds of Python repositories. “The attack targets Python projects — including Django apps, ML research code, Streamlit dashboards, and PyPI packages — by appending obfuscated code to files like setup.py, main.py, and app.py,” … Read More “GlassWorm Attack Uses Stolen GitHub Tokens to Force-Push Malware Into Python Repos – The Hacker News” »
Companies House Restores WebFiling After Flaw Exposed Director Details – Hackread – Cybersecurity News, Data Breaches, AI and More
Companies House fixed a WebFiling flaw that allowed users to view director details and alter company records before the service was taken offline and restored. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Adobe to Pay $150 Million Over Hidden Fees and Hard-to-Cancel Subscriptions – Hackread – Cybersecurity News, Data Breaches, AI and More
The Justice Department says Adobe buried the real cost of cancelling a subscription where most customers would never think to look. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Some weeks in security feel normal. Then you read a few tabs and get that immediate “ah, great, we’re doing this now” feeling. This week has that energy. Fresh messes, old problems getting sharper, and research that stops feeling theoretical real fast. A few bits hit a little too close to real life, too. There’s … Read More “⚡ Weekly Recap: Chrome 0-Days, Router Botnets, AWS Breach, Rogue AI Agents & More – The Hacker News” »
Some of these campaigns are linked to Darcula, a Chinese-language phishing-as-a-service platform – Read More –
CrackArmor AppArmor flaws let local Linux users gain root, break containers and enable DoS attacks – Read More –
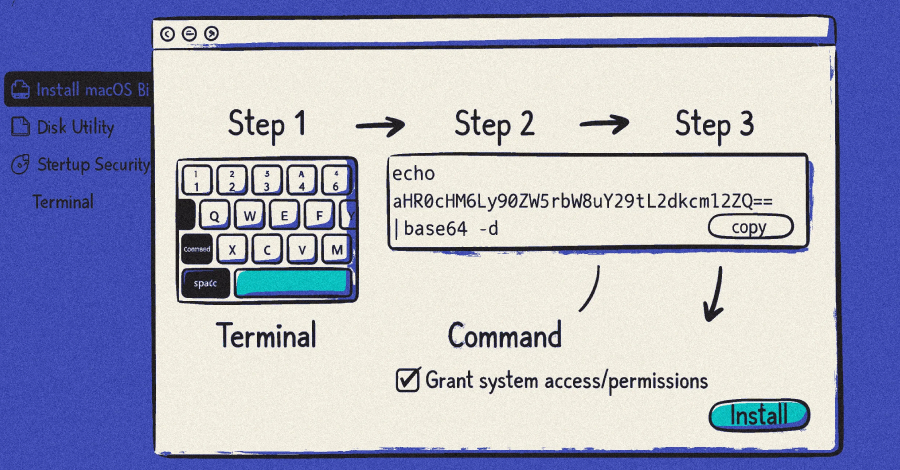
Three different ClickFix campaigns have been found to act as a delivery vector for the deployment of a macOS information stealer called MacSync. “Unlike traditional exploit-based attacks, this method relies entirely on user interaction – usually in the form of copying and executing commands – making it particularly effective against users who may not appreciate … Read More “ClickFix Campaigns Spread MacSync macOS Infostealer via Fake AI Tool Installers – The Hacker News” »
If you run security at any reasonably complex organization, your validation stack probably looks something like this: a BAS tool in one corner. A pentest engagement, or maybe an automated pentesting product, in another. A vulnerability scanner feeding an attack surface management platform somewhere else. Each tool gives you a slice of the picture. None … Read More “Why Security Validation Is Becoming Agentic – The Hacker News” »
DNS-based attack in AWS Bedrock AgentCore lets AI sandboxes exfiltrate cloud data – Read More –
Kevuru Games Outlines the Shift Toward Flexible Art Production in the Games Industry – Hackread – Cybersecurity News, Data Breaches, AI and More

Kyiv, Ukraine, 16th March 2026, CyberNewswire – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
New XWorm 7.1 and Remcos RAT Attacks Abuse Windows Tools to Evade Detection – Hackread – Cybersecurity News, Data Breaches, AI and More
New XWorm 7.1 and Remcos RAT campaigns abuse trusted Windows tools to evade detection. The attacks exploit a WinRAR flaw and use process hollowing to spy on victims. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
The FBI wants to hear from gamers who have downloaded Steam titles containing malware – Read More –
DRILLAPP Backdoor Targets Ukraine, Abuses Microsoft Edge Debugging for Stealth Espionage – The Hacker News

Ukrainian entities have emerged as the target of a new campaign likely orchestrated by threat actors linked to Russia, according to a report from S2 Grupo’s LAB52 threat intelligence team. The campaign, observed in February 2026, has been assessed to share overlaps with a prior campaign mounted by Laundry Bear (aka UAC-0190 or Void Blizzard) … Read More “DRILLAPP Backdoor Targets Ukraine, Abuses Microsoft Edge Debugging for Stealth Espionage – The Hacker News” »