Why Image Format Conversion Is Becoming a Practical Issue in Web Security and Performance – Hackread – Cybersecurity News, Data Breaches, AI and More
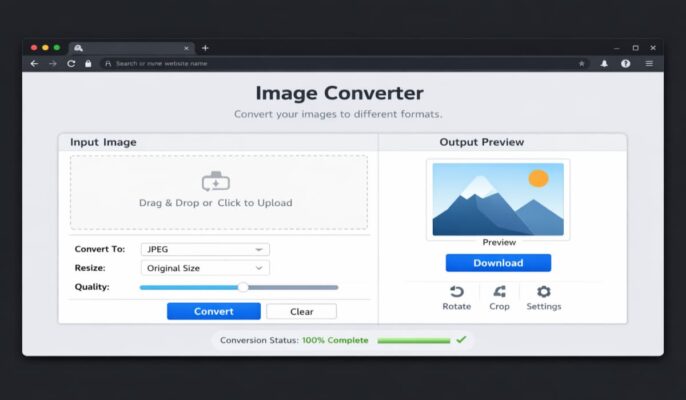
WebP boosts performance raises compatibility issues, making image format conversion to PNG essential for secure, flexible, and efficient web workflows today. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More