Day 3 of Pwn2Own Automotive 2026 is here – the final push. The world’s top security researchers return for their last shots at the latest automotive targets. After two days, $955,750 awarded for 66 unique 0-day vulnerabilities, and the Master of Pwn leaderboard has a clear frontrunner as the competition heads into its final stretch. … Read More “Pwn2Own Automotive 2026 – Day Three Results and the Master of Pwn – Zero Day Initiative – Blog” »
Google to Pay $8.25M Settlement Over Child Data Tracking in Play Store – Hackread – Cybersecurity News, Data Breaches, AI, and More
Is your child’s data safe? Google settles for $8.25M over claims it tracked kids under 13 without parental… – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More
A Russian national pleaded guilty to leading a ransomware conspiracy that targeted at least 50 victims during a four-year period ending in August 2022. Ianis Aleksandrovich Antropenko began participating in ransomware attacks before moving to the United States, but conducted many of his crimes while living in Florida and California, where he’s been out on … Read More “Leader of ransomware crew pleads guilty to four-year crime spree – CyberScoop” »
A nonprofit is suing the federal government for records surrounding a data sharing agreement between the Transportation Security Administration and Immigrations and Customs Enforcement that saw domestic travel data used for immigration enforcement. Government watchdog group American Oversight filed suit against the agencies Thursday in the U.S. District Court for the District of Columbia, a … Read More “Watchdog group sues for TSA data sharing agreement with ICE – CyberScoop” »
Cybersecurity researchers have disclosed details of a new ransomware family called Osiris that targeted a major food service franchisee operator in Southeast Asia in November 2025. The attack leveraged a malicious driver called POORTRY as part of a known technique referred to as bring your own vulnerable driver (BYOVD) to disarm security software, the Symantec … Read More “New Osiris Ransomware Emerges as New Strain Using POORTRY Driver in BYOVD Attack – The Hacker News” »
A vulnerability has been discovered in Cisco Unified Communications Products which could allow for remote code execution. Cisco Unified Communications (UC) Products are an integrated suite of IP-based hardware and software that combine voice, video, messaging, and data into a single platform. Successful exploitation of this vulnerability could allow for remote code execution as root, … Read More “A Vulnerability in Cisco Unified Communications Products Could Allow for Remote Code Execution – Cyber Security Advisories – MS-ISAC” »
Hackers Are Using LinkedIn DMs and PDF Tools to Deploy Trojans – Hackread – Cybersecurity News, Data Breaches, AI, and More
That LinkedIn message pretending to be job offer could just be malwre. – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More
Researchers find Jordan government used Cellebrite phone-cracking tech against activists – CyberScoop

Jordanian authorities used Cellebrite phone-cracking technology to access the devices of domestic activists and human rights defenders and then extract information from them, according to an investigation published Thursday. The nonconsensual access stood in conflict with international human rights treaties that Jordan ratified, the University of Toronto’s Citizen Lab investigation determined, prompting the research organization … Read More “Researchers find Jordan government used Cellebrite phone-cracking tech against activists – CyberScoop” »
Critical GNU InetUtils telnetd Flaw Lets Attackers Bypass Login and Gain Root Access – The Hacker News
A critical security flaw has been disclosed in the GNU InetUtils telnet daemon (telnetd) that went unnoticed for nearly 11 years. The vulnerability, tracked as CVE-2026-24061, is rated 9.8 out of 10.0 on the CVSS scoring system. It affects all versions of GNU InetUtils from version 1.9.3 up to and including version 2.7. “Telnetd in … Read More “Critical GNU InetUtils telnetd Flaw Lets Attackers Bypass Login and Gain Root Access – The Hacker News” »
Critical vulnerability in Appsmith allows account takeover via flawed password reset process – Read More –
ThreatsDay Bulletin: Pixel Zero-Click, Redis RCE, China C2s, RAT Ads, Crypto Scams & 15+ Stories – The Hacker News

Most of this week’s threats didn’t rely on new tricks. They relied on familiar systems behaving exactly as designed, just in the wrong hands. Ordinary files, routine services, and trusted workflows were enough to open doors without forcing them. What stands out is how little friction attackers now need. Some activity focused on quiet reach … Read More “ThreatsDay Bulletin: Pixel Zero-Click, Redis RCE, China C2s, RAT Ads, Crypto Scams & 15+ Stories – The Hacker News” »
Security flaw in RealHomes CRM plugin allowed file uploads; patches released for 30,000+ sites – Read More –
VoidLink Malware Puts Cloud Systems on High Alert With Custom Built Attacks – Hackread – Cybersecurity News, Data Breaches, AI, and More

Sysdig TRT analysis reveals VoidLink as a revolutionary Linux threat. Using Serverside Rootkit Compilation and Zig code, it targets AWS and Azure with adaptive stealth. – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More
Phoney email alerts suggest users need to backup their LastPass accounts within 24 hours. LastPass says it would never require this action from users – Read More –
VulnCheck analysts found that vulnerabilities exploited before being publicly disclosed rose from 23.6% in 2024 to 28.96% in 2025 – Read More –
Security teams at agile, fast-growing companies often have the same mandate: secure the business without slowing it down. Most teams inherit a tech stack optimized for breakneck growth, not resilience. In these environments, the security team is the helpdesk, the compliance expert, and the incident response team all rolled into one. Securing the cloud office … Read More “Filling the Most Common Gaps in Google Workspace Security – The Hacker News” »
UK Executives Warn They May Not Survive a Major Cyber-Attack, Vodafone Survey Finds – Read More –
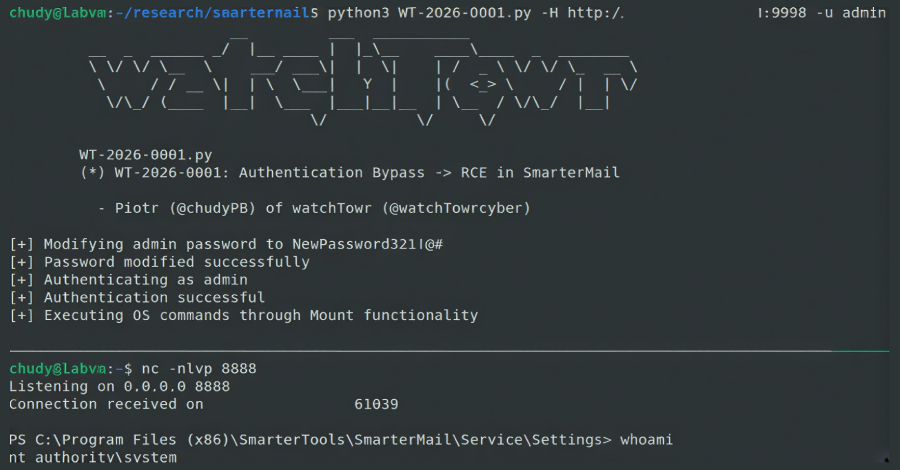
A new security flaw in SmarterTools SmarterMail email software has come under active exploitation in the wild, two days after the release of a patch. The vulnerability, which currently does not have a CVE identifier, is tracked by watchTowr Labs as WT-2026-0001. It was patched by SmarterTools on January 15, 2026, with Build 9511, following … Read More “SmarterMail Auth Bypass Exploited in the Wild Two Days After Patch Release – The Hacker News” »
A new malicious package discovered in the Python Package Index (PyPI) has been found to impersonate a popular library for symbolic mathematics to deploy malicious payloads, including a cryptocurrency miner, on Linux hosts. The package, named sympy-dev, mimics SymPy, replicating the latter’s project description verbatim in an attempt to deceive unsuspecting users into thinking that … Read More “Malicious PyPI Package Impersonates SymPy, Deploys XMRig Miner on Linux Hosts – The Hacker News” »
DLA Piper finds 22% increase in breached firms notifying European GDPR regulators – Read More –
European Space Agency’s cybersecurity in freefall as yet another breach exposes spacecraft and mission data – GRAHAM CLULEY

It has just been a few weeks since reports emerged of the Christmas cyber attack suffered by the European Space Agency (ESA), and the situation has already become worse. Read more in my article on the Hot for Security blog. – Read More – GRAHAM CLULEY
Automated FortiGate Attacks Exploit FortiCloud SSO to Alter Firewall Configurations – The Hacker News

Cybersecurity company Arctic Wolf has warned of a “new cluster of automated malicious activity” that involves unauthorized firewall configuration changes on Fortinet FortiGate devices. The activity, it said, commenced on January 15, 2026, adding it shares similarities with a December 2025 campaign in which malicious SSO logins on FortiGate appliances were recorded against the admin … Read More “Automated FortiGate Attacks Exploit FortiCloud SSO to Alter Firewall Configurations – The Hacker News” »
Day Two of Pwn2Own Automotive 2026 is underway, and the stakes are rising. Security researchers are back on the Pwn2Own stage, continuing to probe and challenge the latest automotive systems as the competition intensifies. New exploits, unexpected twists, and standout performances are already emerging – follow along here for daily updates as the race for Master … Read More “Pwn2Own Automotive 2026 – Day Two Results – Zero Day Initiative – Blog” »
Cisco has released fresh patches to address what it described as a “critical” security vulnerability impacting multiple Unified Communications (CM) products and Webex Calling Dedicated Instance that it has been actively exploited as a zero-day in the wild. The vulnerability, CVE-2026-20045 (CVSS score: 8.2), could permit an unauthenticated remote attacker to execute arbitrary commands on … Read More “Cisco Fixes Actively Exploited Zero-Day CVE-2026-20045 in Unified CM and Webex – The Hacker News” »
As enterprises continue their rapid shift toward digital-first operations, data protection has evolved from a technical safeguard into a… The post Tokenization vs Encryption: How to Choose appeared first on JISA Softech Pvt Ltd. – Read More – JISA Softech Pvt Ltd
PwC’s 29th Global CEO Survey shows cyber risk rising to the top of CEO concerns as confidence in short term business growth weakens – Read More –
Smashing Security podcast #451: I hacked the government, and your headphones are next – GRAHAM CLULEY

In episode 451 of “Smashing Security,” we meet the cybercriminal who hacked the US Supreme Court, Veterans Affairs, and more – and then helpfully posted screenshots (and even someone’s blood type) on an account called “I hacked the government.” Plus we discuss how researchers uncovered a creepy flaw that lets attackers hijack wireless headphones, listen … Read More “Smashing Security podcast #451: I hacked the government, and your headphones are next – GRAHAM CLULEY” »
The National Institute for Standards and Technology is starting 2026 with a smaller staff, a shrinking budget and some big responsibilities around supporting national security and cybersecurity. At a meeting Wednesday of the Information Security Privacy Advisory Board, NIST officials provided updates on how they’re grappling with several Trump administration priorities, including mandates on AI, … Read More “NIST officials detail impact of staff cuts on encryption and other priorities – CyberScoop” »
Iranian TV Transmission Hacked With Message from Exiled Prince – Hackread – Cybersecurity News, Data Breaches, AI, and More
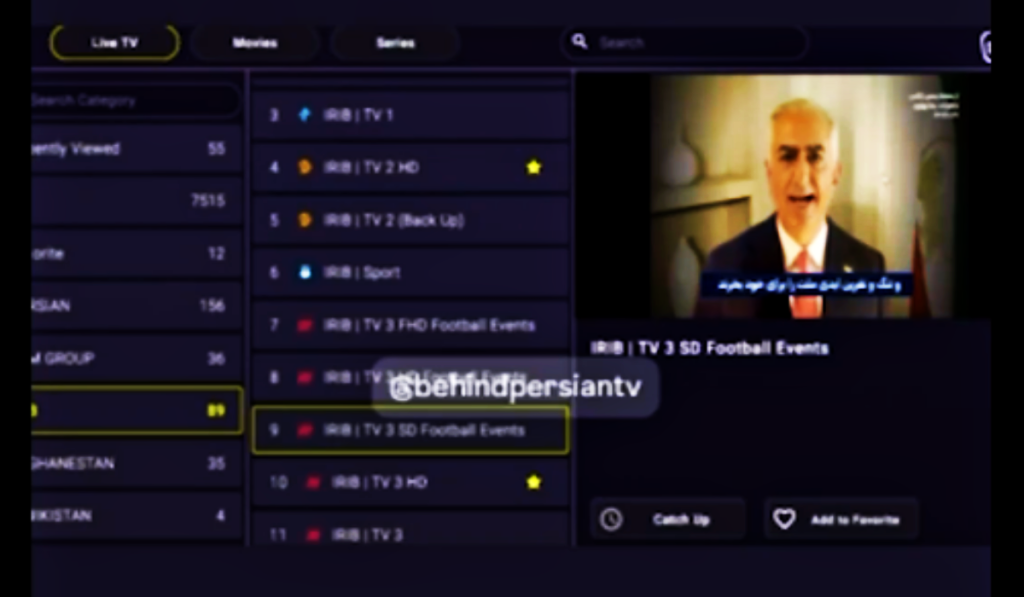
Unidentified hackers disrupted Iranian state television to broadcast messages from exiled Crown Prince Reza Pahlavi. Read about the economic crisis, the internet blackout, and the latest reports on the protest death toll. – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More
The acting head of the Cybersecurity and Infrastructure Security Agency faced pointed questions from lawmakers Wednesday over CISA personnel decisions and staffing levels. Members of the House Homeland Security Committee asked Madhu Gottumukkala about a reported attempt to fire the agency’s chief information officer, efforts to push out a large number of staff and whether … Read More “Lawmakers probe CISA leader over staffing decisions – CyberScoop” »
A European cybersecurity organization has launched a decentralized system for identifying and numbering software security vulnerabilities, introducing a fundamental shift in how the global technology community could track and manage security flaws. The Global CVE Allocation System, or GCVE, will be maintained by The Computer Incident Response Center Luxembourg (CIRCL) as an alternative to the … Read More “GCVE launches as a decentralized system for tracking software vulnerabilities – CyberScoop” »
A European cybersecurity organization has launched a decentralized system for identifying and numbering software security vulnerabilities, introducing a fundamental shift in how the global technology community could track and manage security flaws. The Global CVE Allocation System, or GCVE, will be maintained by The Computer Incident Response Center Luxembourg (CIRCL) as an alternative to the … Read More “GCVE launches as a decentralized system for tracking software vulnerabilities – CyberScoop” »
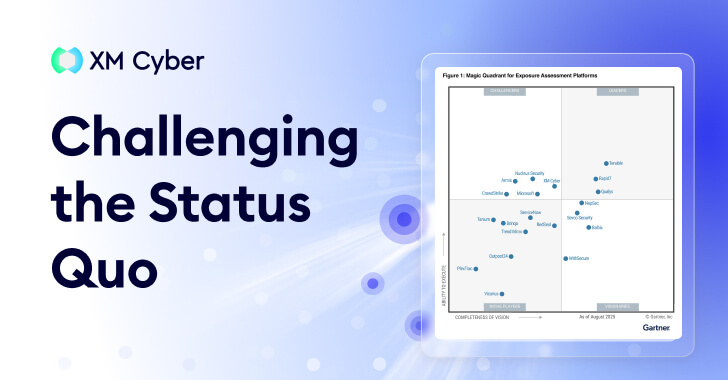
Gartner® doesn’t create new categories lightly. Generally speaking, a new acronym only emerges when the industry’s collective “to-do list” has become mathematically impossible to complete. And so it seems that the introduction of the Exposure Assessment Platforms (EAP) category is a formal admission that traditional Vulnerability Management (VM) is no longer a viable way to … Read More “Exposure Assessment Platforms Signal a Shift in Focus – The Hacker News” »
Posted by BUG on Jan 21 #### Title:OpenMetadata <= 1.11.3 Authenticated SQL Injection #### Affected versions: <= 1.11.3 #### Credits: echo #### Vendor: https://open-metadata.org/ OpenMetadata versions 1.11.3 and earlier are vulnerable to an authenticated SQL injection issue. Low-privileged users can exploit this vulnerability to gain unauthorized access to the database in the context of … Read More “OpenMetadata” »
Re: Multiple Security Misconfigurations and Customer Enumeration Exposure in Convercent Whistleblowing Platform (EQS Group) – Full Disclosure

Posted by Wade Sparks on Jan 21 Hello Yuffie, Upon further investigation, the VulnCheck CNA determined that these vulnerabilities were not suitable for CVE assignment. The vulnerabilities exist within a SaaS product and are mitigated at the CSP-level which in this case, would be the vendor, EQS Group. Rather than contribute unactionable CVE records, … Read More “Re: Multiple Security Misconfigurations and Customer Enumeration Exposure in Convercent Whistleblowing Platform (EQS Group) – Full Disclosure” »
North Korean PurpleBravo Campaign Targeted 3,136 IP Addresses via Fake Job Interviews – The Hacker News
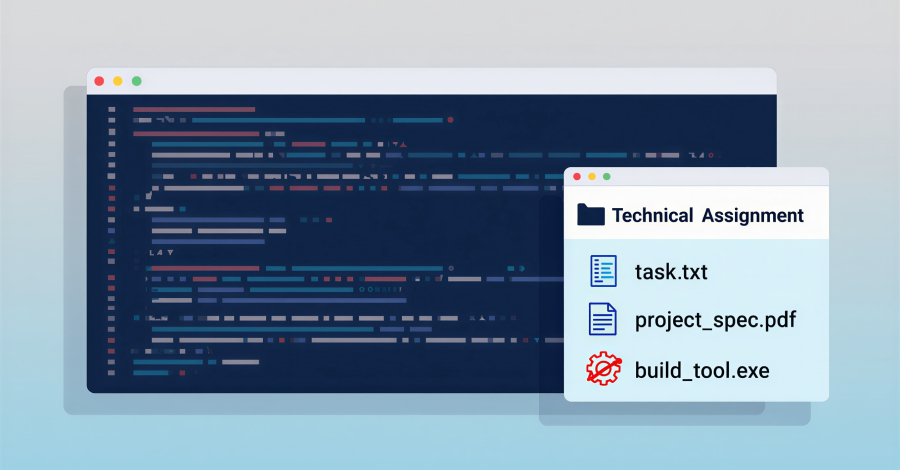
As many as 3,136 individual IP addresses linked to likely targets of the Contagious Interview activity have been identified, with the campaign claiming 20 potential victim organizations spanning artificial intelligence (AI), cryptocurrency, financial services, IT services, marketing, and software development sectors in Europe, South Asia, the Middle East, and Central America. The new findings – … Read More “North Korean PurpleBravo Campaign Targeted 3,136 IP Addresses via Fake Job Interviews – The Hacker News” »
Zoom and GitLab have released security updates to resolve a number of security vulnerabilities that could result in denial-of-service (DoS) and remote code execution. The most severe of the lot is a critical security flaw impacting Zoom Node Multimedia Routers (MMRs) that could permit a meeting participant to conduct remote code execution attacks. The vulnerability, … Read More “Zoom and GitLab Release Security Updates Fixing RCE, DoS, and 2FA Bypass Flaws – The Hacker News” »
Law enforcement agencies from multiple European countries are still pursuing leads on people involved in the Black Basta ransomware group, nearly a year after the group’s internal chat logs were leaked, exposing key details about its operations, and at least six months since the group claimed responsibility for new attacks. Officials in Ukraine and Germany … Read More “Black Basta’s alleged ringleader identified as authorities raid homes of other members – CyberScoop” »
Cyber risks for the Milano-Cortina 2026 Winter Games include phishing and spoofed websites as key threat vectors – Read More –
A security vulnerability has been disclosed in the popular binary-parser npm library that, if successfully exploited, could result in the execution of arbitrary JavaScript. The vulnerability, tracked as CVE-2026-1245 (CVSS score: N/A), affects all versions of the module prior to version 2.3.0, which addresses the issue. Patches for the flaw were released on November 26, … Read More “CERT/CC Warns binary-parser Bug Allows Node.js Privilege-Level Code Execution – The Hacker News” »
LastPass is alerting users to a new active phishing campaign that’s impersonating the password management service, which aims to trick users into giving up their master passwords. The campaign, which began on or around January 19, 2026, involves sending phishing emails claiming upcoming maintenance and urging them to create a local backup of their password … Read More “LastPass Warns of Fake Maintenance Messages Targeting Users’ Master Passwords – The Hacker News” »
Loan phishing operation in Peru is stealing card info by impersonating financial institutions – Read More –
New Research Exposes Critical Gap: 64% of Third-Party Applications Access Sensitive Data Without Authorization – Hackread – Cybersecurity News, Data Breaches, AI, and More

Boston, MA, USA, 21st January 2026, CyberNewsWire – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More
Sophisticated malware previously thought to be the work of a well-resourced cyber-crime group was built by one person – with the aid of AI tools – Read More –
The UK’s National Cyber Security Centre (NCSC) has issued a warning about the threat posed by distributed denial-of-service (DDoS) attacks from Russia-linked hacking groups who are reported to be continuing to target British organisations. Are you prepared? Read more in my article on the Hot for Security blog. – Read More – GRAHAM CLULEY
Carlsberg Event Wristband Leaked PII, Researcher Told Not to Disclose – Hackread – Cybersecurity News, Data Breaches, AI, and More
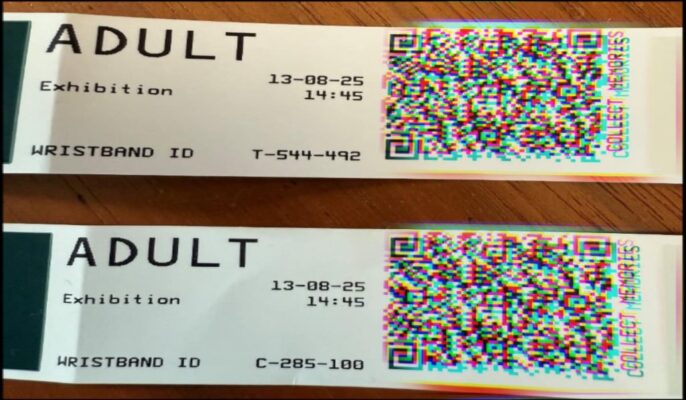
A poorly secured wristband system used at a Carlsberg exhibition allowed access to visitor photos, videos, and full names. Attempts to report the issue were ignored for months. – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More
Every managed security provider is chasing the same problem in 2026 — too many alerts, too few analysts, and clients demanding “CISO-level protection” at SMB budgets. The truth? Most MSSPs are running harder, not smarter. And it’s breaking their margins. That’s where the quiet revolution is happening: AI isn’t just writing reports or surfacing risks … Read More “Webinar: How Smart MSSPs Using AI to Boost Margins with Half the Staff – The Hacker News” »
The EU’s Cybersecurity Act 2.0 will aim to address some of the challenges of the current CSA, including the slow rollout of certification schemes – Read More –
Ransomware negotiation is a dark but widely acknowledged reality in the cybersecurity industry — one that many argue is a necessary practice, even if it largely occurs out of sight. Brokering payments and terms with cybercriminals who hold organizations’ data and operations hostage places security professionals in a fraught position that requires them to balance … Read More “The thin line between saving a company and funding a crime – CyberScoop” »
Ransomware negotiation is a dark but widely acknowledged reality in the cybersecurity industry — one that many argue is a necessary practice, even if it largely occurs out of sight. Brokering payments and terms with cybercriminals who hold organizations’ data and operations hostage places security professionals in a fraught position that requires them to balance … Read More “The thin line between saving a company and funding a crime – CyberScoop” »