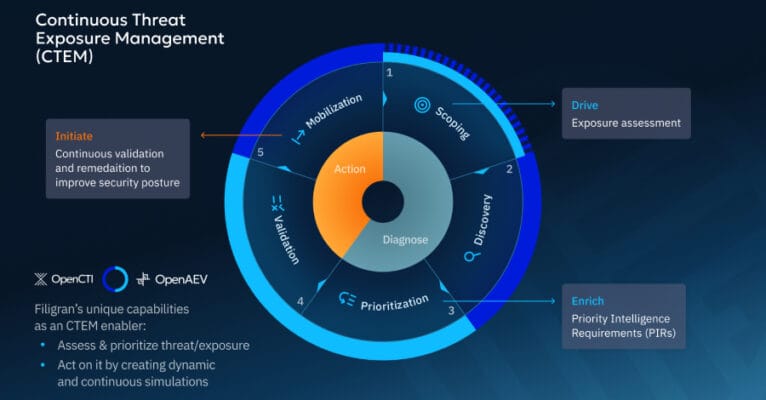
Cybersecurity teams increasingly want to move beyond looking at threats and vulnerabilities in isolation. It’s not only about what could go wrong (vulnerabilities) or who might attack (threats), but where they intersect in your actual environment to create real, exploitable exposure. Which exposures truly matter? Can attackers exploit them? Are our defenses effective? Continuous Threat … Read More “CTEM in Practice: Prioritization, Validation, and Outcomes That Matter – The Hacker News” »
US Charges 31 Suspects in Nationwide ATM Jackpotting Scam – Hackread – Cybersecurity News, Data Breaches, AI, and More

US prosecutors have charged 31 more suspects in a nationwide ATM jackpotting scam, bringing the total number of defendants to 87 across multiple states. – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More
Cybersecurity researchers have discovered a JScript-based command-and-control (C2) framework called PeckBirdy that has been put to use by China-aligned APT actors since 2023 to target multiple environments. The flexible framework has been put to use against Chinese gambling industries and malicious activities targeting Asian government entities and private organizations, according to Trend Micro – Read … Read More “China-Linked Hackers Have Used the PeckBirdy JavaScript C2 Framework Since 2023 – The Hacker News” »
A critical security flaw has been disclosed in Grist‑Core, an open-source, self-hosted version of the Grist relational spreadsheet-database, that could result in remote code execution. The vulnerability, tracked as CVE-2026-24002 (CVSS score: 9.1), has been codenamed Cellbreak by Cyera Research Labs. “One malicious formula can turn a spreadsheet into a Remote Code Execution (RCE) beachhead,” … Read More “Critical Grist-Core Vulnerability Allows RCE Attacks via Spreadsheet Formulas – The Hacker News” »
Microsoft urged customers running Microsoft Office 2016 and 2019 to apply the patch to be protected – Read More –
Nike is investigating after the World Leaks ransomware group posted a 1.4TB data dump – Read More –
Microsoft Office Zero-Day (CVE-2026-21509) – Emergency Patch Issued for Active Exploitation – The Hacker News

Microsoft on Monday issued out-of-band security patches for a high-severity Microsoft Office zero-day vulnerability exploited in attacks. The vulnerability, tracked as CVE-2026-21509, carries a CVSS score of 7.8 out of 10.0. It has been described as a security feature bypass in Microsoft Office. “Reliance on untrusted inputs in a security decision in Microsoft Office allows … Read More “Microsoft Office Zero-Day (CVE-2026-21509) – Emergency Patch Issued for Active Exploitation – The Hacker News” »
With increasing volume of data and regulatory controls that are only tightening, regulated industries have a hard paradox to… The post How Regulated Industries Use Privacy-Enhancing Technologies (PETs) appeared first on JISA Softech Pvt Ltd. – Read More – JISA Softech Pvt Ltd
SEC Consult SA-20260126-0 :: Multiple Critical Vulnerabilities in dormakaba Kaba exos 9300 – Full Disclosure

Posted by SEC Consult Vulnerability Lab via Fulldisclosure on Jan 26 SEC Consult Vulnerability Lab Security Advisory < 20260126-0 > ======================================================================= title: Multiple Critical Vulnerabilities product: dormakaba Kaba exos 9300 vulnerable version: < 4.4.1 fixed version: 4.4.1 CVE number: CVE-2025-59090, CVE-2025-59091, CVE-2025-59092 CVE-2025-59093, CVE-2025-59094, CVE-2025-59095… – Read More – Full Disclosure
SEC Consult SA-20260126-1 :: Multiple Critical Vulnerabilities in dormakaba Access Manager – Full Disclosure

Posted by SEC Consult Vulnerability Lab via Fulldisclosure on Jan 26 SEC Consult Vulnerability Lab Security Advisory < 20260126-1 > ======================================================================= title: Multiple Critical Vulnerabilities product: dormakaba Access Manager vulnerable version: Multiple firmware and hardware revisions (details below) fixed version: Multiple firmware and hardware revisions (details below) CVE number: CVE-2025-59097,… – … Read More “SEC Consult SA-20260126-1 :: Multiple Critical Vulnerabilities in dormakaba Access Manager – Full Disclosure” »
SEC Consult SA-20260126-2 :: UART Leaking Sensitive Data in dormakaba registration unit 9002 (PIN pad) – Full Disclosure

Posted by SEC Consult Vulnerability Lab via Fulldisclosure on Jan 26 SEC Consult Vulnerability Lab Security Advisory < 20260126-2 > ======================================================================= title: UART Leaking Sensitive Data product: dormakaba registration unit 9002 (PIN pad) vulnerable version: <SW0039 fixed version: SW0039 CVE number: … Read More “SEC Consult SA-20260126-2 :: UART Leaking Sensitive Data in dormakaba registration unit 9002 (PIN pad) – Full Disclosure” »
Re: Multiple Security Misconfigurations and Customer Enumeration Exposure in Convercent Whistleblowing Platform (EQS Group) – Full Disclosure

Posted by Marco Ermini via Fulldisclosure on Jan 26 Hello everyone, Kindly let me introduce myself. This is the first – and potentially, last – message on this mailing list. I am Marco, the CISO of EQS Group. Kindly allow me to address some of the statements expressed publicly here. About the Convercent application … Read More “Re: Multiple Security Misconfigurations and Customer Enumeration Exposure in Convercent Whistleblowing Platform (EQS Group) – Full Disclosure” »
Re: Multiple Security Misconfigurations and Customer Enumeration Exposure in Convercent Whistleblowing Platform (EQS Group) – Full Disclosure

Posted by Yuffie Kisaragi via Fulldisclosure on Jan 26 Dear Art, Thank you for sharing your detailed evaluation and for pointing out the relevant sections of the CNA Rules. Your argument is well reasoned, particularly with respect to the current guidance on SaaS and exclusively hosted services. I have forwarded your evaluation to the … Read More “Re: Multiple Security Misconfigurations and Customer Enumeration Exposure in Convercent Whistleblowing Platform (EQS Group) – Full Disclosure” »
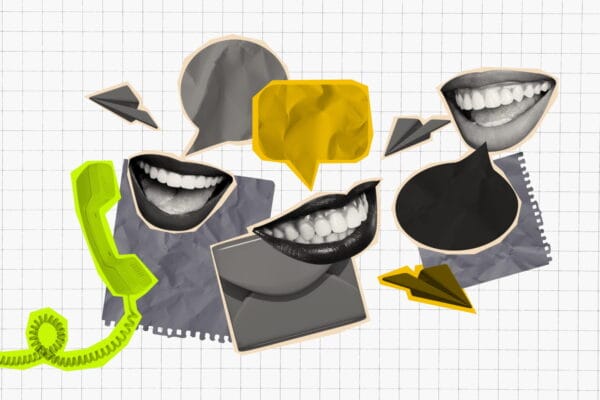
Threat hunters and researchers are racing to contain a wave of voice-phishing attacks targeting single sign-on tools, already leading to data theft and extortion attempts. Multiple cybercrime groups are combining voice calls and advanced phishing kits to trick victims into handing over access — including a group identifying itself as ShinyHunters, which has publicly named alleged … Read More “A new wave of ‘vishing’ attacks is breaking into SSO accounts in real time – CyberScoop” »
CISA publishes a post-quantum shopping list for agencies. Security professionals aren’t sold – CyberScoop

The Cybersecurity and Infrastructure Security Agency is hoping to guide federal agencies through the murky process of updating their technology stack with quantum-resistant encryption. On Jan. 23, the agency released a list of different IT software and hardware products that are commonly purchased by the federal government and use cryptographic algorithms for encryption or authentication. … Read More “CISA publishes a post-quantum shopping list for agencies. Security professionals aren’t sold – CyberScoop” »
The Trump administration is rescinding a Biden-era memo that was intended to help agencies buy secure software, with the current Office of Management and Budget saying it relied on “unproven and burdensome” processes. A former Biden administration official said the move is “the first major policy step back that I have seen in the administration … Read More “OMB rescinds ‘burdensome’ Biden-era secure software memo – CyberScoop” »
Fake Microsoft Teams Billing Phishing Alerts Reach 6,135 Users via 12,866 Emails – Hackread – Cybersecurity News, Data Breaches, AI, and More

Scammers are abusing Microsoft Teams invitations to send fake billing notices, with 12,866 emails reaching around 6,135 users in a phone-based phishing campaign. – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More
ChatGPT users beware: your browser extensions could be used to steal your accounts and identity. LayerX Research has identified at least 16 Chrome browser extensions for ChatGPT floating around the internet that promise to enhance work productivity. All show signs of being built by the same threat actor and designed for the same purpose: to … Read More “Some ChatGPT browser extensions are stealing your data – CyberScoop” »
Supply chain breach in eScan antivirus distributes multi-stage malware via legitimate updates – Read More –
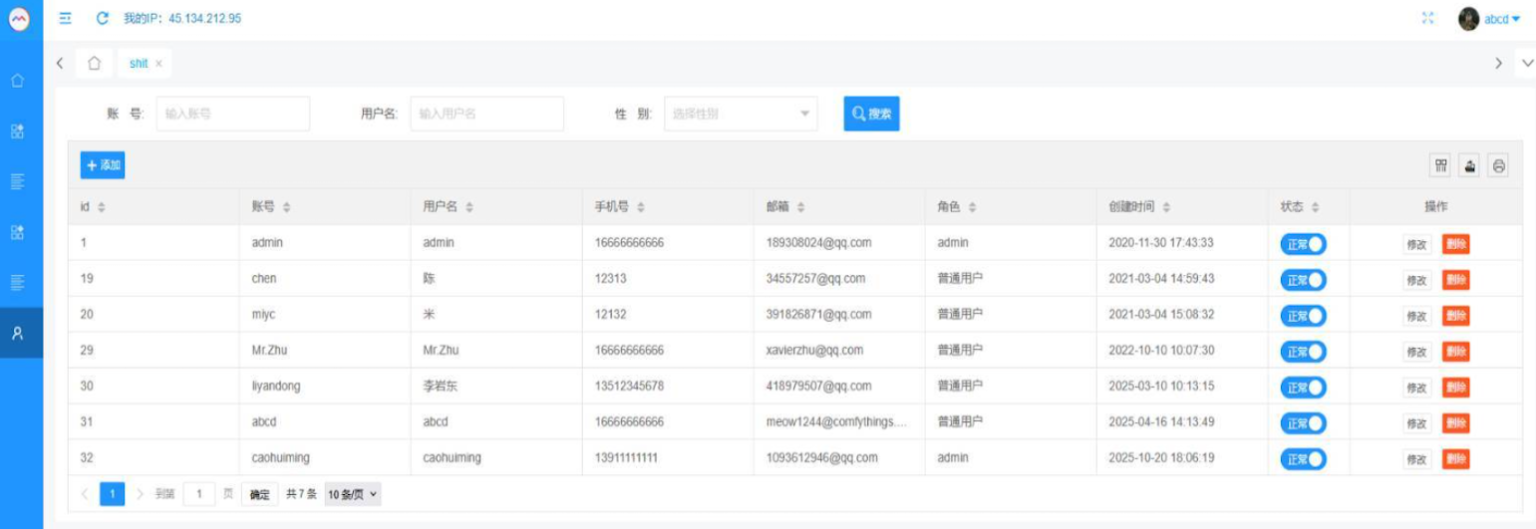
Cybersecurity researchers have discovered an ongoing campaign that’s targeting Indian users with a multi-stage backdoor as part of a suspected cyber espionage campaign. The activity, per the eSentire Threat Response Unit (TRU), involves using phishing emails impersonating the Income Tax Department of India to trick victims into downloading a malicious archive, ultimately granting the threat … Read More “Indian Users Targeted in Tax Phishing Campaign Delivering Blackmoon Malware – The Hacker News” »
Cybersecurity researchers have discovered an ongoing campaign that’s targeting Indian users with a multi-stage backdoor as part of a suspected cyber espionage campaign. The activity, per the eSentire Threat Response Unit (TRU), involves using phishing emails impersonating the Income Tax Department of India to trick victims into downloading a malicious archive, ultimately granting the threat … Read More “Indian Users Targeted in Tax Phishing Campaign Delivering Blackmoon Malware – The Hacker News” »
Malicious VS Code AI Extensions with 1.5 Million Installs Steal Developer Source Code – The Hacker News
Cybersecurity researchers have discovered two malicious Microsoft Visual Studio Code (VS Code) extensions that are advertised as artificial intelligence (AI)-powered coding assistants, but also harbor covert functionality to siphon developer data to China-based servers. The extensions, which have 1.5 million combined installs and are still available for download from the official Visual Studio – Read … Read More “Malicious VS Code AI Extensions with 1.5 Million Installs Steal Developer Source Code – The Hacker News” »
CISA released initial list of PQC-capable hardware and software to guide companies amid quantum threats – Read More –
The cybercriminals in control of Kimwolf — a disruptive botnet that has infected more than 2 million devices — recently shared a screenshot indicating they’d compromised the control panel for Badbox 2.0, a vast China-based botnet powered by malicious software that comes pre-installed on many Android TV streaming boxes. Both the FBI and Google say … Read More “Who Operates the Badbox 2.0 Botnet? – Krebs on Security” »
Fortra researchers have discovered a new SEO poisoning operation known as “HaxorSEO” – Read More –
Nike Data Breach Claims Surface as WorldLeaks Leaks 1.4TB of Files Online – Hackread – Cybersecurity News, Data Breaches, AI, and More
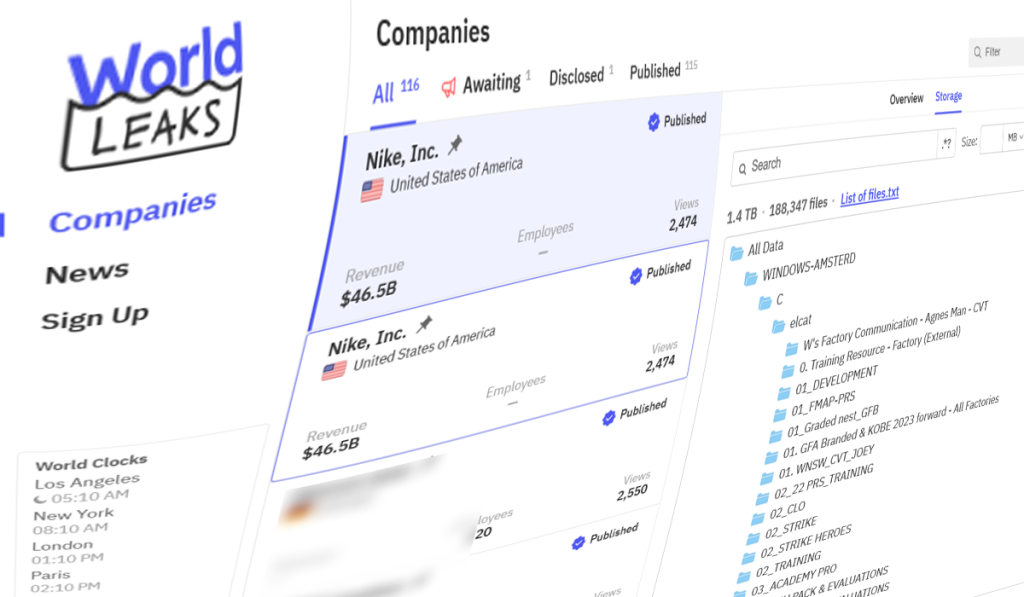
As users continue to assess the Under Armour data breach, WorldLeaks, the rebranded version of the Hunters International… – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More
An international effort to create voluntary standards for the commercial cyber intrusion industry is wrestling with questions like who they should apply to, how to incentivize and measure compliance and what to do with companies with a checkered past. The first round of the Pall Mall Process focused on a code of conduct for government … Read More “Industry, government, nonprofits weigh voluntary rules for commercial hacking tools – CyberScoop” »
New Fake CAPTCHA Scam Abuses Microsoft Tools to Install Amatera Stealer – Hackread – Cybersecurity News, Data Breaches, AI, and More

Another day, another fake CAPTCHA scam, but this one abuses Microsoft’s signed tools. – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More
The US law firm Hagens Berman will lead a class action lawsuit against Coupang over security failures that led to a June 2025 data breach – Read More –
⚡ Weekly Recap: Firewall Flaws, AI-Built Malware, Browser Traps, Critical CVEs & More – The Hacker News

Security failures rarely arrive loudly. They slip in through trusted tools, half-fixed problems, and habits people stop questioning. This week’s recap shows that pattern clearly. Attackers are moving faster than defenses, mixing old tricks with new paths. “Patched” no longer means safe, and every day, software keeps becoming the entry point. What follows is a … Read More “⚡ Weekly Recap: Firewall Flaws, AI-Built Malware, Browser Traps, Critical CVEs & More – The Hacker News” »
Threat actors posing as IT support teams use phishing kits to generate fake login sites in real-time to trick victims into handing over credentials – Read More –
$6,000 “Stanley” Toolkit Sold on Russian Forums Fakes Secure URLs in Chrome – Hackread – Cybersecurity News, Data Breaches, AI, and More
Say hello to Stanley, a new malicious toolkit that guarantees bypassing Google’s Chrome Web Store review process. – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More
If there’s a constant in cybersecurity, it’s that adversaries are always innovating. The rise of offensive AI is transforming attack strategies and making them harder to detect. Google’s Threat Intelligence Group, recently reported on adversaries using Large Language Models (LLMs) to both conceal code and generate malicious scripts on the fly, letting malware shape-shift in … Read More “Winning Against AI-Based Attacks Requires a Combined Defensive Approach – The Hacker News” »
A destructive cyber attack targeting Poland’s energy sector has been linked to Russian APT group Sandworm – Read More –
Konni Hackers Deploy AI-Generated PowerShell Backdoor Against Blockchain Developers – The Hacker News

The North Korean threat actor known as Konni has been observed using PowerShell malware generated using artificial intelligence (AI) tools to target developers and engineering teams in the blockchain sector. The phishing campaign has targeted Japan, Australia, and India, highlighting the adversary’s expansion of the targeting scope beyond South Korea, Russia, Ukraine, and European nations, … Read More “Konni Hackers Deploy AI-Generated PowerShell Backdoor Against Blockchain Developers – The Hacker News” »
7 Top Endpoint Security Platforms for 2026 – Hackread – Cybersecurity News, Data Breaches, AI, and More
Endpoints remain primary entry for attacks. In 2026, endpoint platforms must deliver behavior context, automation, investigations, and integrations. – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More
FBI Accessed Windows Laptops After Microsoft Shared BitLocker Recovery Keys – Hackread – Cybersecurity News, Data Breaches, AI, and More

If you are using a Windows PC, your privacy and security are nothing short of a myth, and this incident proves it. – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More
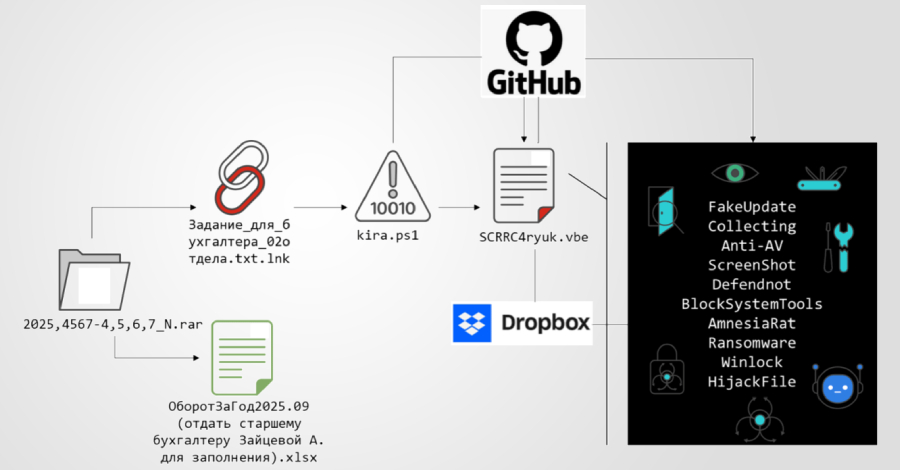
A new multi-stage phishing campaign has been observed targeting users in Russia with ransomware and a remote access trojan called Amnesia RAT. “The attack begins with social engineering lures delivered via business-themed documents crafted to appear routine and benign,” Fortinet FortiGuard Labs researcher Cara Lin said in a technical breakdown published this week. “These documents … Read More “Multi-Stage Phishing Campaign Targets Russia with Amnesia RAT and Ransomware – The Hacker News” »
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday added a critical security flaw affecting Broadcom VMware vCenter Server that was patched in June 2024 to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation in the wild. The vulnerability in question is CVE-2024-37079 (CVSS score: 9.8), which refers to a heap … Read More “CISA Adds Actively Exploited VMware vCenter Flaw CVE-2024-37079 to KEV Catalog – The Hacker News” »
Who Approved This Agent? Rethinking Access, Accountability, and Risk in the Age of AI Agents – The Hacker News

AI agents are accelerating how work gets done. They schedule meetings, access data, trigger workflows, write code, and take action in real time, pushing productivity beyond human speed across the enterprise. Then comes the moment every security team eventually hits: “Wait… who approved this?” Unlike users or applications, AI agents are often deployed quickly, shared … Read More “Who Approved This Agent? Rethinking Access, Accountability, and Risk in the Age of AI Agents – The Hacker News” »
The Russian nation-state hacking group known as Sandworm has been attributed to what has been described as the “largest cyber attack” targeting Poland’s power system in the last week of December 2025. The attack was unsuccessful, the country’s energy minister, Milosz Motyka, said last week. “The command of the cyberspace forces has diagnosed in the … Read More “New DynoWiper Malware Used in Attempted Sandworm Attack on Polish Power Sector – The Hacker News” »
149M Logins from Roblox, TikTok, Netflix, Crypto Wallets Found Online – Hackread – Cybersecurity News, Data Breaches, AI, and More

Another day, another trove of login credentials in plain text found online. – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More
Venezuelan Nationals Face Deportation After Multi State ATM Jackpotting Scheme – Hackread – Cybersecurity News, Data Breaches, AI, and More

According to authorities, both suspects were in the United States unlawfully. – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More
Halo Security Achieves SOC 2 Type II Compliance, Demonstrating Sustained Security Excellence Over Time – Hackread – Cybersecurity News, Data Breaches, AI, and More

Halo Security, a leading provider of external attack surface management and penetration testing services, today announced it has… – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added four security flaws to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation in the wild. The list of vulnerabilities is as follows – CVE-2025-68645 (CVSS score: 8.8) – A PHP remote file inclusion vulnerability in Synacor Zimbra Collaboration Suite (ZCS) that … Read More “CISA Updates KEV Catalog with Four Actively Exploited Software Vulnerabilities – The Hacker News” »
Open letter by NHS technology leaders outlines plans to identify risks to software supply chain security across health and social are system – Read More –
ShinyHunters Leak Alleged Data of Millions From SoundCloud, Crunchbase and Betterment – Hackread – Cybersecurity News, Data Breaches, AI, and More

ShinyHunters claim more data breaches and leaks are coming soon! – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More
Fortinet Confirms Active FortiCloud SSO Bypass on Fully Patched FortiGate Firewalls – The Hacker News

Fortinet has officially confirmed that it’s working to completely plug a FortiCloud SSO authentication bypass vulnerability following reports of fresh exploitation activity on fully-patched firewalls. “In the last 24 hours, we have identified a number of cases where the exploit was to a device that had been fully upgraded to the latest release at the … Read More “Fortinet Confirms Active FortiCloud SSO Bypass on Fully Patched FortiGate Firewalls – The Hacker News” »
Phishing Attack Uses Stolen Credentials to Install LogMeIn RMM for Persistent Access – The Hacker News
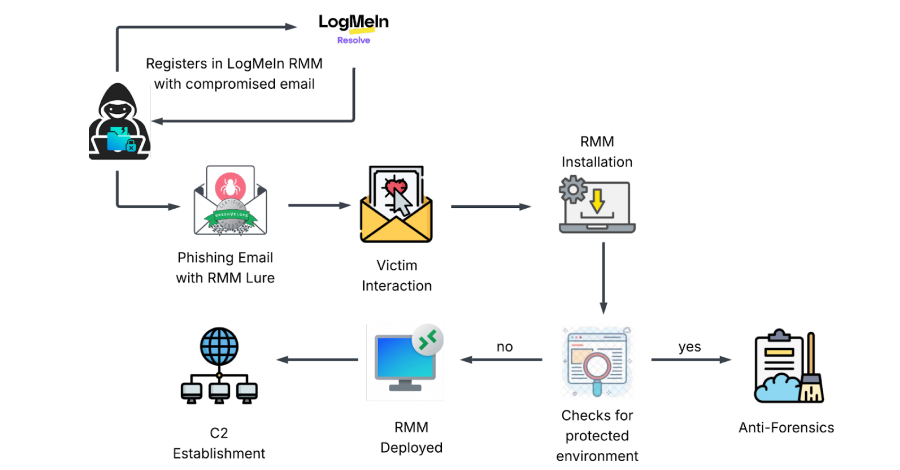
Cybersecurity researchers have disclosed details of a new dual-vector campaign that leverages stolen credentials to deploy legitimate Remote Monitoring and Management (RMM) software for persistent remote access to compromised hosts. “Instead of deploying custom viruses, attackers are bypassing security perimeters by weaponizing the necessary IT tools that administrators trust,” KnowBe4 Threat – Read More – … Read More “Phishing Attack Uses Stolen Credentials to Install LogMeIn RMM for Persistent Access – The Hacker News” »
TikTok on Friday officially announced that it formed a joint venture that will allow the hugely popular video-sharing application to continue operating in the U.S. The new venture, named TikTok USDS Joint Venture LLC, has been established in compliance with the Executive Order signed by U.S. President Donald Trump in September 2025, the platform said. … Read More “TikTok Forms U.S. Joint Venture to Continue Operations Under 2025 Executive Order – The Hacker News” »