The Caracas operation suggests cyber was part of the plan – just not the whole operation – CyberScoop

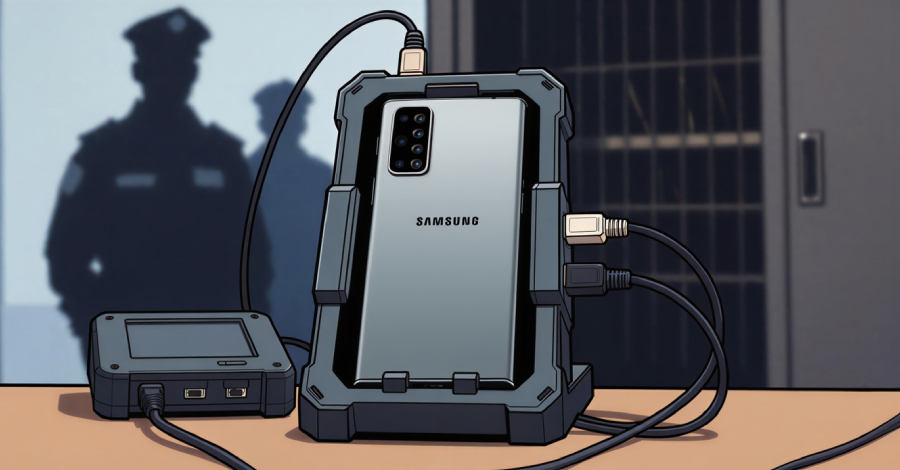
The dominant narrative has framed the Jan. 3 Caracas power outage during the mission to capture Venezuelan leader Nicolás Maduro as a “precision cyberattack.” But publicly available information points to a more complicated picture: videos, photographs, and accounts published from Caracas show significant physical damage to at least three Venezuelan substations. Experts who reviewed that … Read More “The Caracas operation suggests cyber was part of the plan – just not the whole operation – CyberScoop” »