Multiple vulnerabilities have been discovered in Google Chrome, the most severe of which could allow for arbitrary code execution. Successful exploitation of the most severe of these vulnerabilities could allow for arbitrary code execution in the context of the logged on user. Depending on the privileges associated with the user an attacker could then install … Read More “*DRAFT* MS-ISAC CYBERSECURITY ADVISORY – Multiple Vulnerabilities in Google Chrome Could Allow for Arbitrary Code Execution – PATCH: NOW – TLP: CLEAR – Cyber Security Advisories – MS-ISAC” »
Category: Gov/ISAC Feeds
CISA has added six new vulnerabilities to its Known Exploited Vulnerabilities Catalog, based on evidence of active exploitation. CVE-2025-24983 Microsoft Windows Win32k Use-After-Free Vulnerability CVE-2025-24984 Microsoft Windows NTFS Information Disclosure Vulnerability CVE-2025-24985 Microsoft Windows Fast FAT File System Driver Integer Overflow Vulnerability CVE-2025-24991 Microsoft Windows NTFS Out-Of-Bounds Read Vulnerability CVE-2025-24993 Microsoft Windows NTFS Heap-Based Buffer Overflow … Read More “CISA Adds Six Known Exploited Vulnerabilities to Catalog – All CISA Advisories” »
Optigo Networks Visual BACnet Capture Tool/Optigo Visual Networks Capture Tool – All CISA Advisories
View CSAF 1. EXECUTIVE SUMMARY CVSS v4 9.3 ATTENTION: Exploitable remotely/low attack complexity Vendor: Optigo Networks Equipment: Visual BACnet Capture Tool, Optigo Visual Networks Capture Tool Vulnerabilities: Use of Hard-coded, Security-relevant Constants, Authentication Bypass Using an Alternate Path or Channel 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow an attacker to bypass authentication, … Read More “Optigo Networks Visual BACnet Capture Tool/Optigo Visual Networks Capture Tool – All CISA Advisories” »
View CSAF 1. EXECUTIVE SUMMARY CVSS v4 6.8 ATTENTION: Low attack complexity Vendor: Schneider Electric Equipment: Uni-Telway Driver Vulnerability: Improper Input Validation 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to perform a denial of service. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS Schneider Electric reports the following products are affected: Schneider … Read More “Schneider Electric Uni-Telway Driver – All CISA Advisories” »
CISA released two Industrial Control Systems (ICS) advisories on March 11, 2025. These advisories provide timely information about current security issues, vulnerabilities, and exploits surrounding ICS. ICSA-25-070-01 Schneider Electric Uni-Telway Driver ICSA-25-070-02 Optigo Networks Visual BACnet Capture Tool/Optigo Visual Networks Capture Tool CISA encourages users and administrators to review newly released ICS advisories for technical … Read More “CISA Releases Two Industrial Control Systems Advisories – All CISA Advisories” »
The new algorithm will serve as a backup for the general encryption needed to protect data from quantum computers developed in the future. – Read More – News and Events Feed by Topic
CISA has added five new vulnerabilities to its Known Exploited Vulnerabilities Catalog, based on evidence of active exploitation. CVE-2025-25181 Advantive VeraCore SQL Injection Vulnerability CVE-2024-57968 Advantive VeraCore Unrestricted File Upload Vulnerability CVE-2024-13159 Ivanti Endpoint Manager (EPM) Absolute Path Traversal Vulnerability CVE-2024-13160 Ivanti Endpoint Manager (EPM) Absolute Path Traversal Vulnerability CVE-2024-13161 Ivanti Endpoint Manager (EPM) Absolute Path Traversal Vulnerability These … Read More “CISA Adds Five Known Exploited Vulnerabilities to Catalog – All CISA Advisories” »
The Federal Bureau of Investigation (FBI) Internet Crime Complaint Center (IC3) has released an alert warning of a scam involving criminal actors masquerading as the “BianLian Group.” The cyber criminals target corporate executives by sending extortion letters threatening to release victims’ sensitive information unless payment is received. CISA encourages organizations to review the following FBI Public Service … Read More “FBI Warns of Data Extortion Scam Targeting Corporate Executives – All CISA Advisories” »
Using differential privacy can help organizations glean useful insights from databases while protecting individuals’ data. – Read More – News and Events Feed by Topic
Using differential privacy can help organizations glean useful insights from databases while protecting individuals’ data. – Read More – News and Events Feed by Topic
Post Content – Read More – IC3.gov News
View CSAF 1. EXECUTIVE SUMMARY CVSS v3 7.5 ATTENTION: Exploitable remotely/low attack complexity Vendor: Hitachi Energy Equipment: PCU400, PCULogger Vulnerabilities: Access of Resource Using Incompatible Type (‘Type Confusion’), NULL Pointer Dereference, Use After Free, Double Free, Observable Discrepancy, Out-of-bounds Read 2. RISK EVALUATION Exploitation of these vulnerabilities could allow an attacker to access or decrypt … Read More “Hitachi Energy PCU400 – All CISA Advisories” »
CISA released three Industrial Control Systems (ICS) advisories on March 6, 2025. These advisories provide timely information about current security issues, vulnerabilities, and exploits surrounding ICS. ICSA-25-065-01 Hitachi Energy PCU400 ICSA-25-065-02 Hitachi Energy Relion 670/650/SAM600-IO ICSA-25-037-02 Schneider Electric EcoStruxure (Update A) CISA encourages users and administrators to review newly released ICS advisories for technical details … Read More “CISA Releases Three Industrial Control Systems Advisories – All CISA Advisories” »
View CSAF 1. EXECUTIVE SUMMARY CVSS v4 8.6 ATTENTION: Exploitable remotely/low attack complexity Vendor: Hitachi Energy Equipment: Relion 670/650/SAM600-IO Vulnerability: Improper Handling of Insufficient Privileges 2. RISK EVALUATION Successful exploitation of this vulnerability could allow anyone with user credentials to bypass the security controls enforced by the product. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS Hitachi … Read More “Hitachi Energy Relion 670/650/SAM600-IO – All CISA Advisories” »
Post Content – Read More – IC3.gov News
Remote system administration provides powerful and flexible access to systems and services. – Read More – NCSC Feed
How NCSC guidance can help organisations detect and protect themselves from credential abuse. – Read More – NCSC Feed
Vulnerability Scanning solutions offer a cost-effective way to discover and manage common security issues. – Read More – NCSC Feed
We publish the results of our ACD 2.0 external attack surface management (EASM) trials – Read More – NCSC Feed
Phishing is one of the most common types of cyber crime. These scams use convincing emails or other messages, such as text messages or social media messages, to trick users into opening harmful links, downloading malicious software, or submitting – Read More – News and Events Feed by Topic
Post Content – Read More – IC3.gov News
Compromise of your software build pipeline can have wide-reaching impact; here’s how to tackle the problem. – Read More – NCSC Feed
Zero trust architecture design principles 1.0 launched. – Read More – NCSC Feed
Chris Ensor highlights some important elements of the NCSC’s new Technology Assurance strategy. – Read More – NCSC Feed
Multiple vulnerabilities have been discovered in VMware ESXi, Workstation, and Fusion could allow for local code execution. VMware ESXi, Workstation, and Fusion are all virtualization products that allow users to run virtual machines (VMs) on their computers. Successful exploitation of these vulnerability could allow for local code execution in the context of the administrator account. An … Read More “Multiple vulnerabilities have been discovered in VMware ESXi, Workstation, and Fusion which could allow for local code execution. – Cyber Security Advisories – MS-ISAC” »
Simon Arnell, co-founder of Configured Things, describes how the NCSC For Startups programme helped the company solve an intelligence community challenge. – Read More – NCSC Feed
CISA has added five new vulnerabilities to its Known Exploited Vulnerabilities Catalog, based on evidence of active exploitation. CVE-2023-20118 Cisco Small Business RV Series Routers Command Injection Vulnerability CVE-2022-43939 Hitachi Vantara Pentaho BA Server Authorization Bypass Vulnerability CVE-2022-43769 Hitachi Vantara Pentaho BA Server Special Element Injection Vulnerability CVE-2018-8639 Microsoft Windows Win32k Improper Resource Shutdown or Release Vulnerability CVE-2024-4885 Progress WhatsUp Gold … Read More “CISA Adds Five Known Exploited Vulnerabilities to Catalog – All CISA Advisories” »
Post Content – Read More – IC3.gov News
View CSAF 1. EXECUTIVE SUMMARY CVSS v3 9.8 ATTENTION: Exploitable remotely/low attack complexity Vendor: Schneider Electric Equipment: Communication modules for Modicon M580 and Quantum controllers Vulnerability: Out-of-bounds Write 2. RISK EVALUATION Successful exploitation of this vulnerability could allow a stack overflow attack, which could result in loss of confidentiality, integrity, and denial of service of … Read More “Schneider Electric Communication Modules for Modicon M580 and Quantum Controllers – All CISA Advisories” »
CISA released two Industrial Control Systems (ICS) advisories on February 27, 2025. These advisories provide timely information about current security issues, vulnerabilities, and exploits surrounding ICS. ICSA-25-058-01 Schneider Electric Communication Modules for Modicon M580 and Quantum Controllers ICSMA-25-058-01 Dario Health USB-C Blood Glucose Monitoring System Starter Kit Android Application CISA encourages users and administrators to … Read More “CISA Releases Two Industrial Control Systems Advisories – All CISA Advisories” »
View CSAF 1. EXECUTIVE SUMMARY CVSS v4 8.7 ATTENTION: Exploitable remotely/low attack complexity Vendor: Dario Health Equipment: USB-C Blood Glucose Monitoring System Starter Kit Android Application, Application Database and Internet-based Server Infrastructure Vulnerabilities: Exposure of Private Personal Information to an Unauthorized Actor, Improper Output Neutralization For Logs, Storage of Sensitive Data In a Mechanism Without … Read More “Dario Health USB-C Blood Glucose Monitoring System Starter Kit Android Application – All CISA Advisories” »
Post Content – Read More – IC3.gov News
CISA released two Industrial Control Systems (ICS) advisories on February 25, 2025. These advisories provide timely information about current security issues, vulnerabilities, and exploits surrounding ICS. ICSA-25-056-01 Rockwell Automation PowerFlex 755 ICSMA-25-030-01 Contec Health CMS8000 Patient Monitor (Update A) CISA encourages users and administrators to review newly released ICS advisories for technical details and mitigations. … Read More “CISA Releases Two Industrial Control Systems Advisories – All CISA Advisories” »
View CSAF 1. EXECUTIVE SUMMARY CVSS v4 8.7 ATTENTION: Exploitable remotely/Low attack complexity Vendor: Rockwell Automation Equipment: PowerFlex 755 Vulnerability: Cleartext Transmission of Sensitive Information 2. RISK EVALUATION Successful exploitation of this vulnerability could result in exposure of sensitive data. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following version of PowerFlex 755, a motor application … Read More “Rockwell Automation PowerFlex 755 – All CISA Advisories” »
CISA has added two new vulnerabilities to its Known Exploited Vulnerabilities Catalog, based on evidence of active exploitation. CVE-2024-49035 Microsoft Partner Center Improper Access Control Vulnerability CVE-2023-34192 Synacor Zimbra Collaboration Suite (ZCS) Cross-Site Scripting (XSS) Vulnerability Users and administrators are also encouraged to review the Palo Alto Threat Brief: Operation Lunar Peek related to CVE-2024-0012, the Palo Alto … Read More “CISA Adds Two Known Exploited Vulnerabilities to Catalog – All CISA Advisories” »
CISA has added two new vulnerabilities to its Known Exploited Vulnerabilities Catalog, based on evidence of active exploitation. CVE-2017-3066 Adobe ColdFusion Deserialization Vulnerability CVE-2024-20953 Oracle Agile Product Lifecycle Management (PLM) Deserialization Vulnerability These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing … Read More “CISA Adds Two Known Exploited Vulnerabilities to Catalog – All CISA Advisories” »
CISA has added one new vulnerability to its Known Exploited Vulnerabilities Catalog, based on evidence of active exploitation. CVE-2025-24989 Microsoft Power Pages Improper Access Control Vulnerability These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of … Read More “CISA Adds One Known Exploited Vulnerability to Catalog – All CISA Advisories” »
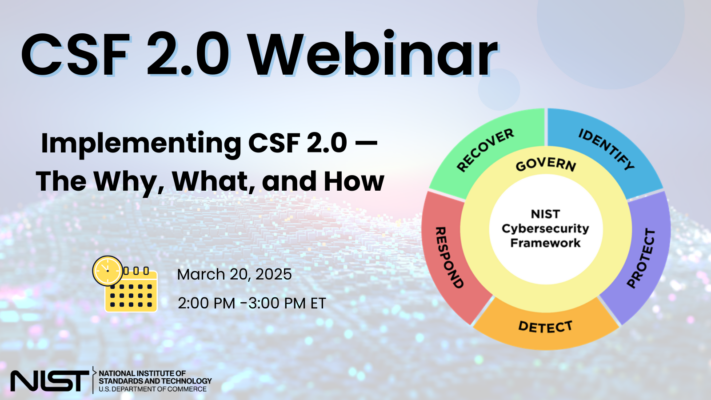
To address the ever-evolving cybersecurity landscape and equip organizations with information and resources to more quickly and effectively manage cybersecurity risk and improve their cybersecurity posture, NIST published a significant update to the – Read More – News and Events Feed by Topic
CISA released eight Industrial Control Systems (ICS) advisories on February 20, 2025. These advisories provide timely information about current security issues, vulnerabilities, and exploits surrounding ICS. ICSA-25-051-01 ABB ASPECT-Enterprise, NEXUS, and MATRIX Series ICSA-25-051-02 ABB FLXEON Controllers ICSA-25-051-03 Carrier Block Load ICSA-25-051-04 Siemens SiPass Integrated ICSA-25-051-05 Rapid Response Monitoring My Security Account App ICSA-25-051-06 Elseta … Read More “CISA Releases Eight Industrial Control Systems Advisories – All CISA Advisories” »
View CSAF 1. EXECUTIVE SUMMARY CVSS v4 9.3 ATTENTION: Exploitable remotely/low attack complexity Vendor: ABB Equipment: ASPECT-Enterprise, NEXUS, and MATRIX series Vulnerability: Use of Hard-coded Credentials 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to obtain access to devices without proper authentication. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS ABB reports the … Read More “ABB ASPECT-Enterprise, NEXUS, and MATRIX Series – All CISA Advisories” »
As of January 10, 2023, CISA will no longer be updating ICS security advisories for Siemens product vulnerabilities beyond the initial advisory. For the most up-to-date information on vulnerabilities in this advisory, please see Siemens’ ProductCERT Security Advisories (CERT Services | Services | Siemens Global). View CSAF 1. EXECUTIVE SUMMARY CVSS v4 9.3 ATTENTION: Exploitable remotely/low attack … Read More “Siemens SiPass Integrated – All CISA Advisories” »
View CSAF 1. EXECUTIVE SUMMARY CVSS v4 10.0 ATTENTION: Exploitable remotely/low attack complexity Vendor: ABB Equipment: FLXEON Controllers Vulnerabilities: Improper Control of Filename for Include/Require Statement in PHP Program (‘PHP Remote File Inclusion’), Missing Origin Validation in WebSockets, Insertion of Sensitive Information into Log File 2. RISK EVALUATION Successful exploitation of these vulnerabilities could allow … Read More “ABB FLXEON Controllers – All CISA Advisories” »
View CSAF 1. EXECUTIVE SUMMARY CVSS v4 5.7 ATTENTION: Low attack complexity Vendor: Medixant Equipment: RadiAnt DICOM Viewer Vulnerability: Improper Certificate Validation 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to perform a machine-in-the-middle attack (MITM), resulting in malicious updates being delivered to the user. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS … Read More “Medixant RadiAnt DICOM Viewer – All CISA Advisories” »
View CSAF 1. EXECUTIVE SUMMARY CVSS v4 8.7 ATTENTION: Exploitable remotely/low attack complexity Vendor: Rapid Response Monitoring Equipment: My Security Account App Vulnerability: Authorization Bypass Through User-Controlled Key 2. RISK EVALUATION Successful exploitation of this vulnerability could allow attacker to access sensitive information of other users. 3. TECHNICAL DETAILS 3.1 AFFECTED PRODUCTS The following Rapid … Read More “Rapid Response Monitoring My Security Account App – All CISA Advisories” »
View CSAF 1. EXECUTIVE SUMMARY CVSS v4 9.4 ATTENTION: Exploitable remotely/low attack complexity Vendor: Elseta Equipment: Vinci Protocol Analyzer Vulnerability: Improper Neutralization of Special Elements used in an OS Command (‘OS Command Injection’) 2. RISK EVALUATION Successful exploitation of this vulnerability could allow an attacker to escalate privileges and perform code execution on the affected … Read More “Elseta Vinci Protocol Analyzer – All CISA Advisories” »