Almost half a million Lloyds customers had personal data exposed in IT glitch – Data and computer security | The Guardian

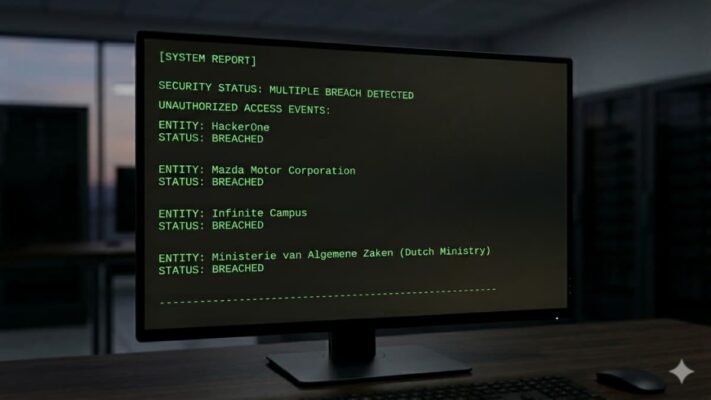
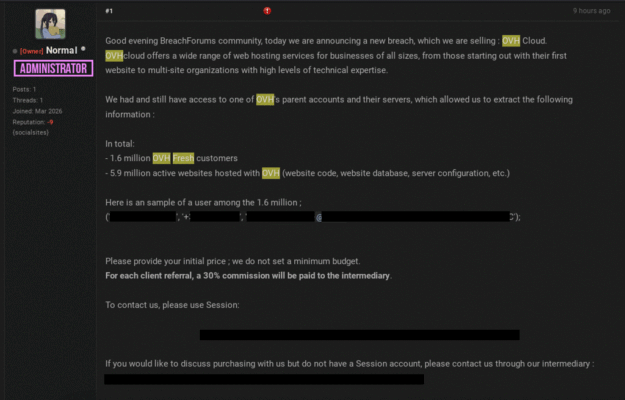
Letter from group published by MPs blames 12 March glitch on software update to its mobile banking apps Lloyds Banking Group exposed the personal data of nearly 500,000 customers in an IT glitch that left people’s payments, account details and national insurance numbers visible to other users, a committee of MPs has revealed. A letter … Read More “Almost half a million Lloyds customers had personal data exposed in IT glitch – Data and computer security | The Guardian” »












![[Webinar] Stop Guessing. Learn to Validate Your Defenses Against Real Attacks – The Hacker News](https://attackfeed.com/wp-content/uploads/2026/03/validate-3lC6Rk.jpg)