Iranian TV Transmission Hacked With Message from Exiled Prince – Hackread – Cybersecurity News, Data Breaches, AI, and More
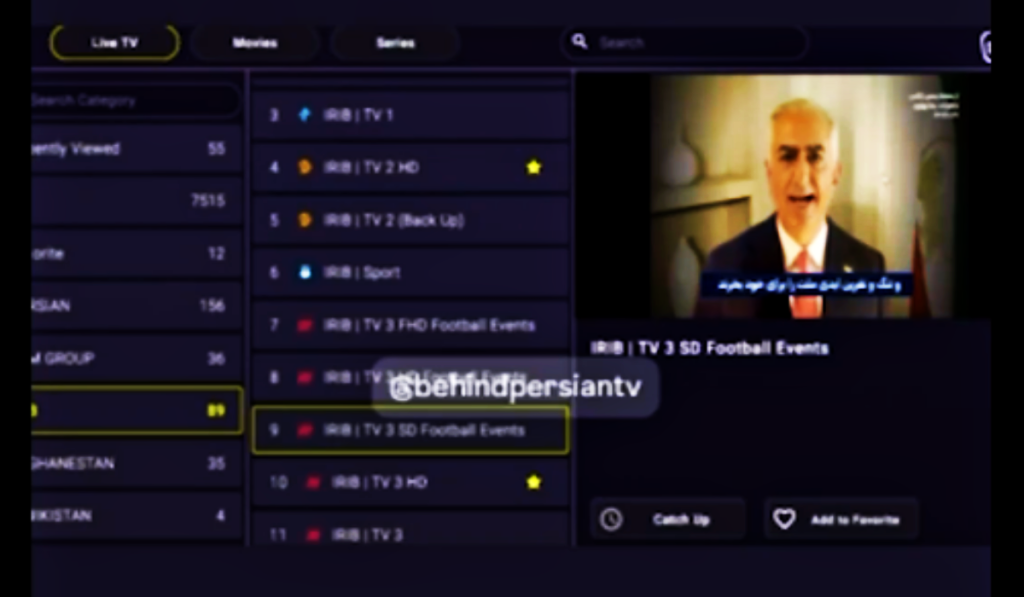
Unidentified hackers disrupted Iranian state television to broadcast messages from exiled Crown Prince Reza Pahlavi. Read about the economic crisis, the internet blackout, and the latest reports on the protest death toll. – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More