Drift has revealed that the April 1, 2026, attack that led to the theft of $285 million was the culmination of a months-long targeted and meticulously planned social engineering operation undertaken by the Democratic People’s Republic of Korea (DPRK) that began in the fall of 2025. The Solana-based decentralized exchange described it as “an attack six months in the – … Read More “$285 Million Drift Hack Traced to Six-Month DPRK Social Engineering Operation – The Hacker News” »
Category: Attack Feeds
Microsoft Details Cookie-Controlled PHP Web Shells Persisting via Cron on Linux Servers – The Hacker News
Threat actors are increasingly using HTTP cookies as a control channel for PHP-based web shells on Linux servers and to achieve remote code execution, according to findings from the Microsoft Defender Security Research Team. “Instead of exposing command execution through URL parameters or request bodies, these web shells rely on threat actor-supplied cookie values to gate execution, … Read More “Microsoft Details Cookie-Controlled PHP Web Shells Persisting via Cron on Linux Servers – The Hacker News” »
BrowserGate: LinkedIn Tracks 6,000+ Browser Extensions on Users’ PCs – Hackread – Cybersecurity News, Data Breaches, AI and More
LinkedIn is accused in the BrowserGate report of tracking 6,000+ browser extensions on users’ PCs, raising concerns over privacy and data collection practices. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Fortinet has released out-of-band patches for a critical security flaw impacting FortiClient EMS that it said has been exploited in the wild. The vulnerability, tracked as CVE-2026-35616 (CVSS score: 9.1), has been described as a pre-authentication API access bypass leading to privilege escalation. “An improper access control vulnerability [CWE-284] in FortiClient EMS may allow an – Read More … Read More “Fortinet Patches Actively Exploited CVE-2026-35616 in FortiClient EMS – The Hacker News” »
36 Malicious npm Packages Exploited Redis, PostgreSQL to Deploy Persistent Implants – The Hacker News
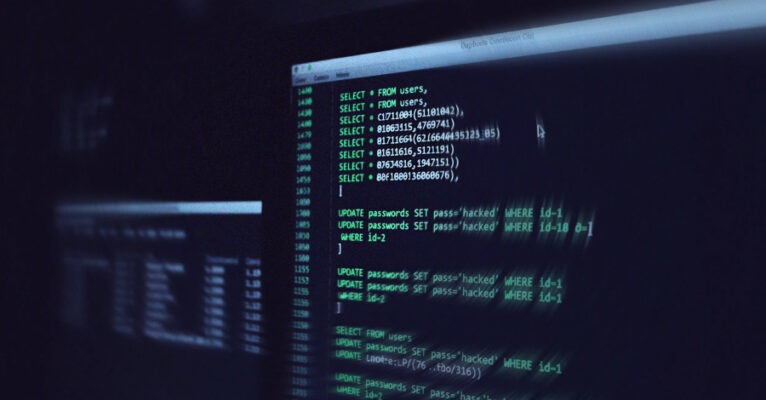
Cybersecurity researchers have discovered 36 malicious packages in the npm registry that are disguised as Strapi CMS plugins but come with different payloads to facilitate Redis and PostgreSQL exploitation, deploy reverse shells, harvest credentials, and drop a persistent implant. “Every package contains three files (package.json, index.js, postinstall.js), has no description, repository, – Read More – The … Read More “36 Malicious npm Packages Exploited Redis, PostgreSQL to Deploy Persistent Implants – The Hacker News” »
UNC1069 Targets Node.js Maintainers via Fake LinkedIn, Slack Profiles – Hackread – Cybersecurity News, Data Breaches, AI and More

North Korean group UNC1069 targets Node.js maintainers using fake LinkedIn and Slack profiles to spread malware and compromise open source packages. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Fake ChatGPT Ad Blocker Chrome Extension Caught Spying on Users – Hackread – Cybersecurity News, Data Breaches, AI and More
A fake Chrome browser extension called ‘ChatGPT Ad Blocker’ was harvesting conversations of ChatGPT users in the name of offering an ad-free experience. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
North Korean Hackers Abuse GitHub to Spy on South Korean Firms – Hackread – Cybersecurity News, Data Breaches, AI and More

Researchers from FortiGuard Labs have uncovered a high-severity spying campaign targeting South Korean companies. Discover how North Korean… – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
China-Linked TA416 Targets European Governments with PlugX and OAuth-Based Phishing – The Hacker News

A China-aligned threat actor has set its sights on European government and diplomatic organizations since mid-2025, following a two-year period of minimal targeting in the region. The campaign has been attributed to TA416, a cluster of activity that overlaps with DarkPeony, RedDelta, Red Lich, SmugX, UNC6384, and Vertigo Panda. “This TA416 activity included multiple – Read More – The Hacker … Read More “China-Linked TA416 Targets European Governments with PlugX and OAuth-Based Phishing – The Hacker News” »
AI Future: The Leading International AI and Web3 Forum to Take Place in April – Hackread – Cybersecurity News, Data Breaches, AI and More

Moscow, Russia, 3rd April 2026, CyberNewswire – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
AI Firm Mercor Confirms Breach as Hackers Claim 4TB of Stolen Data – Hackread – Cybersecurity News, Data Breaches, AI and More

AI firm Mercor confirms a breach linked to a LiteLLM supply chain attack, as hackers claim to have stolen 4TB of sensitive data and internal systems. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Wyden warns Social Security chief: Trump’s voter database is ‘blatant voter suppression’ – CyberScoop

Sen. Ron Wyden, D-Ore., warned Social Security Administration chief Frank Bisignano that any follow-through on President Donald Trump’s executive order creating a new database of U.S. voters using agency data would be viewed by Democrats as a conscious choice on the part of SSA officials to participate in “blatant voter suppression.” “Facilitating Donald Trump’s directive … Read More “Wyden warns Social Security chief: Trump’s voter database is ‘blatant voter suppression’ – CyberScoop” »
President Donald Trump’s fiscal 2027 budget would slash the Cybersecurity and Infrastructure Security Agency’s total by $707 million, according to a summary released Friday, which would deeply chop down an agency that already took a big hit in Trump’s first year. Another budget document suggests a smaller — but still substantial — hit of $361 … Read More “Trump budget proposal would cut hundreds of millions more from CISA – CyberScoop” »
Wyden warns Social Security chief: Trump’s voter database is ‘blatant voter suppression’ – CyberScoop

Sen. Ron Wyden, D-Ore., warned Social Security Administration chief Frank Bisignano that any follow-through on President Donald Trump’s executive order creating a new database of U.S. voters using agency data would be viewed by Democrats as a conscious choice on the part of SSA officials to participate in “blatant voter suppression.” “Facilitating Donald Trump’s directive … Read More “Wyden warns Social Security chief: Trump’s voter database is ‘blatant voter suppression’ – CyberScoop” »
The next major breach hitting your clients probably won’t come from inside their walls. It’ll come through a vendor they trust, a SaaS tool their finance team signed up for, or a subcontractor nobody in IT knows about. That’s the new attack surface, and most organizations are underprepared for it. Cynomi’s new guide, Securing the Modern Perimeter: The Rise of … Read More “Why Third-Party Risk Is the Biggest Gap in Your Clients’ Security Posture – The Hacker News” »
The maintainer of the Axios npm package has confirmed that the supply chain compromise was the result of a highly-targeted social engineering campaign orchestrated by North Korean threat actors tracked as UNC1069. Maintainer Jason Saayman said the attackers tailored their social engineering efforts “specifically to me” by first approaching him under the guise of the founder of … Read More “UNC1069 Social Engineering of Axios Maintainer Led to npm Supply Chain Attack – The Hacker News” »
A Nigerian fraudster spent years posing as a woman online, romancing unsuspecting American men out of their savings – until he accidentally tried the same trick on a fellow scammer, who told him to “learn how to do a clean job.” The recovered chat logs helped put him behind bars for 15 years. Read more … Read More “Nigerian romance scammer jailed after being caught out by fellow fraudster – GRAHAM CLULEY” »
Drift Loses $285 Million in Durable Nonce Social Engineering Attack Linked to DPRK – The Hacker News

Solana-based decentralized exchange Drift has confirmed that attackers drained about $285 million from the platform during a security incident that took place on April 1, 2026. “Earlier today, a malicious actor gained unauthorized access to Drift Protocol through a novel attack involving durable nonces, resulting in a rapid takeover of Drift’s Security Council administrative powers,” the& … Read More “Drift Loses $285 Million in Durable Nonce Social Engineering Attack Linked to DPRK – The Hacker News” »
New SparkCat Variant in iOS, Android Apps Steals Crypto Wallet Recovery Phrase Images – The Hacker News

Cybersecurity researchers have discovered a new version of the SparkCat malware on the Apple App Store and Google Play Store, more than a year after the trojan was discovered targeting both the mobile operating systems. The malware has been found to conceal itself within seemingly benign apps, such as enterprise messengers and food delivery services, while – Read More – The Hacker … Read More “New SparkCat Variant in iOS, Android Apps Steals Crypto Wallet Recovery Phrase Images – The Hacker News” »
A large-scale credential harvesting operation has been observed exploiting the React2Shell vulnerability as an initial infection vector to steal database credentials, SSH private keys, Amazon Web Services (AWS) secrets, shell command history, Stripe API keys, and GitHub tokens at scale. Cisco Talos has attributed the operation to a threat cluster it tracks as – Read More – The Hacker News
ShinyHunters Hackers Claim Theft of 3M+ Cisco Records, Threaten Public Leak – Hackread – Cybersecurity News, Data Breaches, AI and More
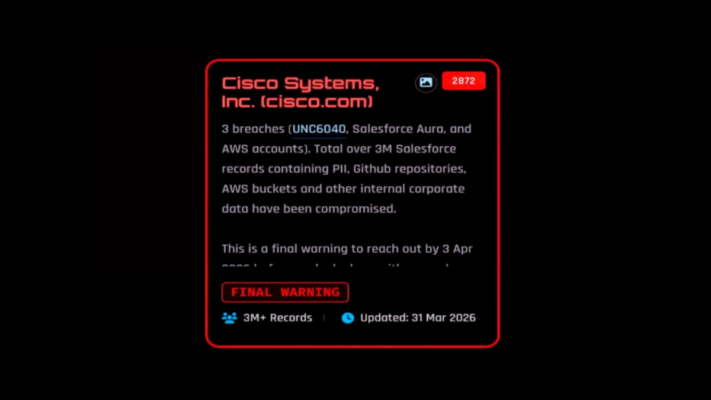
ShinyHunters hackers claim they stole 3 million+ Cisco records via Salesforce and AWS, warning of a public leak if demands are not met by April 3, 2026. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Immigration and Customs Enforcement has confirmed it is using Paragon spyware, prompting outrage Thursday from a trio of House Democrats. In response to a letter from the lawmakers inquiring about Paragon’s use, acting ICE Director Todd Lyons wrote that he had authorized the use of “cutting-edge technological tools” to help the Homeland Security Investigations division … Read More “House Dems decry confirmed ICE usage of Paragon spyware – CyberScoop” »
Cisco has released updates to address a critical security flaw in the Integrated Management Controller (IMC) that, if successfully exploited, could allow an unauthenticated, remote attacker to bypass authentication and gain access to the system with elevated privileges. The vulnerability, tracked as CVE-2026-20093, carries a CVSS score of 9.8 out of a maximum of 10.0. “This – Read More … Read More “Cisco Patches 9.8 CVSS IMC and SSM Flaws Allowing Remote System Compromise – The Hacker News” »
Microsoft Warns of WhatsApp Attachments Spreading Backdoor on Windows PCs – Hackread – Cybersecurity News, Data Breaches, AI and More

Microsoft warns of a WhatsApp attachments spreading VBS malware that installs backdoors on Windows PCs, giving hackers remote access and control systems. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
With the country’s cybersecurity workforce still experiencing major shortages, a bipartisan, bicameral group of lawmakers is pushing to enlist the Department of Labor to help tackle the problem. The Cyber Ready Workforce Act would direct the DOL to establish a grant program that supports the “creation, implementation, and expansion of registered apprenticeship programs in cybersecurity,” … Read More “Lawmakers renew push for Labor Department-backed cyber apprenticeship grants – CyberScoop” »
Akira ransomware group can achieve initial access to data encryption in less than an hour – CyberScoop
The Akira ransomware group has compromised hundreds of victims over the past year with a well-honed attack lifecycle that has whittled down the time from initial access to encryption of data in less than four hours, according to cybersecurity firm Halcyon. Akira has been active since 2023, racking up at least $245 million in ransom … Read More “Akira ransomware group can achieve initial access to data encryption in less than an hour – CyberScoop” »
Medtech company Stryker says it’s back to being “fully operational,” three weeks after it became the most prominent victim to date of Iranian hackers, who said they attacked the Michigan-based company in retaliation over the conflict with the United States and Israel. A March 11 wiper attack from the pro-Palestinian, Iranian government-connected group Handala damaged … Read More “Medtech giant Stryker says it’s back up after Iranian cyberattack – CyberScoop” »
ThreatsDay Bulletin: Pre-Auth Chains, Android Rootkits, CloudTrail Evasion & 10 More Stories – The Hacker News

The latest ThreatsDay Bulletin is basically a cheat sheet for everything breaking on the internet right now. No corporate fluff or boring lectures here, just a quick and honest look at the messy reality of keeping systems safe this week. Things are moving fast. The list includes researchers chaining small bugs together to create massive backdoors, old software flaws – … Read More “ThreatsDay Bulletin: Pre-Auth Chains, Android Rootkits, CloudTrail Evasion & 10 More Stories – The Hacker News” »
Storm Infostealer Sold as Service, Targets Browsers, Wallets and Accounts – Hackread – Cybersecurity News, Data Breaches, AI and More

New research from Varonis Threat Labs reveals Storm infostealer, a malicious subscription service that bypasses Google Chrome encryption.… – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Yurei Ransomware Uses Common Tools, Adds Stranger Things References – Hackread – Cybersecurity News, Data Breaches, AI and More

Team Cymru details the Yurei ransomware campaign, using standard tools and a few Stranger Things–named payloads to breach and encrypt systems. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Why GitHub Developers Are Targeted by Token Giveaway Scams – Hackread – Cybersecurity News, Data Breaches, AI and More

GitHub developers face rising giveaway scams. Verify repos, links, and maintainers before acting. Avoid rushed clicks, fake rewards, and risky wallet actions. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
In December 2025, we shared the first-ever The State of Trusted Open Source report, featuring insights from our product data and customer base on open source consumption across our catalog of container image projects, versions, images, language libraries, and builds. These insights shed light on what teams pull, deploy, and maintain day to day, alongside the vulnerabilities and … Read More “The State of Trusted Open Source Report – The Hacker News” »
Researchers Uncover Mining Operation Using ISO Lures to Spread RATs and Crypto Miners – The Hacker News

A financially motivated operation codenamed REF1695 has been observed leveraging fake installers to deploy remote access trojans (RATs) and cryptocurrency miners since November 2023. “Beyond cryptomining, the threat actor monetizes infections through CPA (Cost Per Action) fraud, directing victims to content locker pages under the guise of software registration,” Elastic – Read More – The Hacker News
WhatsApp Alerts 200 Users After Fake iOS App Installed Spyware; Italian Firm Faces Action – The Hacker News

Meta-owned messaging platform WhatsApp said it alerted about 200 users who were tricked into installing a bogus version of its iOS app that was infected with spyware. According to reports from Italian newspaper La Repubblica and news agency ANSA, the vast majority of the targets are located in Italy. It’s assessed that the threat actors behind the activity … Read More “WhatsApp Alerts 200 Users After Fake iOS App Installed Spyware; Italian Firm Faces Action – The Hacker News” »
Apple on Wednesday expanded the availability of iOS 18.7.7 and iPadOS 18.7.7 to a broader range of devices to protect users from the risk posed by a recently disclosed exploit kit known as DarkSword. “We enabled the availability of iOS 18.7.7 for more devices on April 1, 2026, so users with Automatic Updates turned on can automatically receive important security – … Read More “Apple Expands iOS 18.7.7 Update to More Devices to Block DarkSword Exploit – The Hacker News” »
A cannabis-growing, beekeeping, gyrocopter-flying Irishman invested his drug money in Bitcoin back in 2011 – and now sits on a fortune worth $400 million. There’s just one small problem: the access codes were tucked inside his fishing rod case, which has mysteriously vanished. Or has it? Because this week, one of his frozen wallets suddenly … Read More “Smashing Security podcast #461: This man hid $400 million in a fishing rod. Then it vanished – GRAHAM CLULEY” »
Apple Pushes Rare iOS 18 Patch for Devices at Risk from DarkSword Exploit – Hackread – Cybersecurity News, Data Breaches, AI and More

Apple pushes rare iOS 18 security patch to protect devices at risk from the DarkSword exploit, urging users to update or move to iOS 26 for stronger protection. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
LinkedIn Phishing Scam Uses Fake Notifications to Hijack Accounts – Hackread – Cybersecurity News, Data Breaches, AI and More

A LinkedIn phishing scam uses fake notifications and lookalike domains to steal credentials, hijack accounts, and access sensitive professional data. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
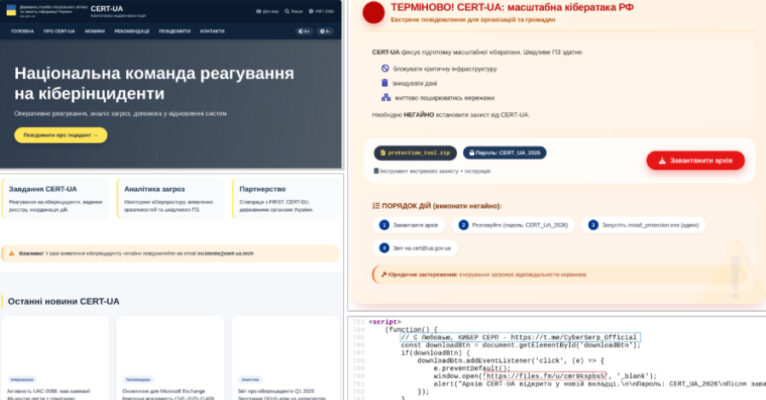
The Computer Emergency Response Team of Ukraine (CERT-UA) has disclosed details of a new phishing campaign in which the cybersecurity agency itself was impersonated to distribute a remote administration tool known as AGEWHEEZE. As part of the attacks, the threat actors, tracked as UAC-0255, sent emails on March 26 and 27, 2026, posing as CERT-UA … Read More “CERT-UA Impersonation Campaign Spread AGEWHEEZE Malware to 1 Million Emails – The Hacker News” »
Anthropic Leaks 512,000 Lines of Claude AI Code in Major Blunder – Hackread – Cybersecurity News, Data Breaches, AI and More
Human error exposed 512,000+ lines of Anthropic Claude AI Code, revealing KAIROS and Capybara secrets, pushing users to switch to the Native Installer. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
A Chinese cyberespionage group has shifted its gaze back to Europe after years of focusing on other parts of the world, Proofpoint research published Wednesday found. The surge began in mid-2025, with a bevy of issues bubbling up between China and Europe, the company said. Proofpoint labels the government-linked group TA416, but other companies track … Read More “European-Chinese geopolitical issues drive renewed cyberespionage campaign – CyberScoop” »
Google on Thursday released security updates for its Chrome web browser to address 21 vulnerabilities, including a zero-day flaw that it said has been exploited in the wild. The high-severity vulnerability, CVE-2026-5281 (CVSS score: N/A), concerns a use-after-free bug in Dawn, an open-source and cross-platform implementation of the WebGPU standard. “Use-after-free in Dawn in Google … Read More “New Chrome Zero-Day CVE-2026-5281 Under Active Exploitation — Patch Released – The Hacker News” »
Microsoft Warns of WhatsApp-Delivered VBS Malware Hijacking Windows via UAC Bypass – The Hacker News

Microsoft is calling attention to a new campaign that has leveraged WhatsApp messages to distribute malicious Visual Basic Script (VBS) files. The activity, beginning in late February 2026, leverages these scripts to initiate a multi-stage infection chain for establishing persistence and enabling remote access. It’s currently not known what lures the threat actors use to … Read More “Microsoft Warns of WhatsApp-Delivered VBS Malware Hijacking Windows via UAC Bypass – The Hacker News” »
A multi-pronged phishing campaign is targeting Spanish-speaking users in organizations across Latin America and Europe to deliver Windows banking trojans like Casbaneiro (aka Metamorfo) via another malware called Horabot. The activity has been attributed to a Brazilian cybercrime threat actor tracked as Augmented Marauder and Water Saci. The e-crime group was first documented by Trend … Read More “Casbaneiro Phishing Targets Latin America and Europe Using Dynamic PDF Lures – The Hacker News” »
Ransomware Groups Exploit Legit IT Tools to Bypass Antivirus – Hackread – Cybersecurity News, Data Breaches, AI and More

New research from Seqrite explains the ‘dual-use dilemma,’ where ransomware attackers repurpose legitimate IT tools like IOBit Unlocker… – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
There is a character that keeps appearing in enterprise security departments, and most CISOs know exactly who that is. It doesn’t build. It doesn’t enable. Its entire function is to say “No.” No to ChatGPT. No to DeepSeek. No to the file-sharing tool the product team swears by. For years, this looked like security. But … Read More “Block the Prompt, Not the Work: The End of “Doctor No” – The Hacker News” »
Defending Encryption in the Post Quantum Era – Hackread – Cybersecurity News, Data Breaches, AI and More
Post-quantum cryptography explained, risks of quantum attacks, and steps to secure data, systems, and infrastructure for a quantum-resilient… – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Cybersecurity Firm TAC Security Hits 10,000 Clients, Enters Top 5 in Global VM & AppSec – Hackread – Cybersecurity News, Data Breaches, AI and More

New York, New York, April 1st, 2026, CyberNewswire – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
ImageMagick Zero-Day Enables RCE on Linux and WordPress Servers – Hackread – Cybersecurity News, Data Breaches, AI and More
New research from Octagon Networks reveals a critical zero-day ImageMagick vulnerability that allows Remote Code Execution (RCE) via simple image uploads affecting Ubuntu, Amazon Linux, and WordPress. This magic byte shift bypasses even the most secure policies. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
3 Reasons Attackers Are Using Your Trusted Tools Against You (And Why You Don’t See It Coming) – The Hacker News

For years, cybersecurity has followed a familiar model: block malware, stop the attack. Now, attackers are moving on to what’s next. Threat actors now use malware less frequently in favor of what’s already inside your environment, including abusing trusted tools, native binaries, and legitimate admin utilities to move laterally, escalate privileges, and persist without raising … Read More “3 Reasons Attackers Are Using Your Trusted Tools Against You (And Why You Don’t See It Coming) – The Hacker News” »