Op Bizarre Bazaar: New LLMjacking Campaign Targets Unprotected Models – Hackread – Cybersecurity News, Data Breaches, AI, and More

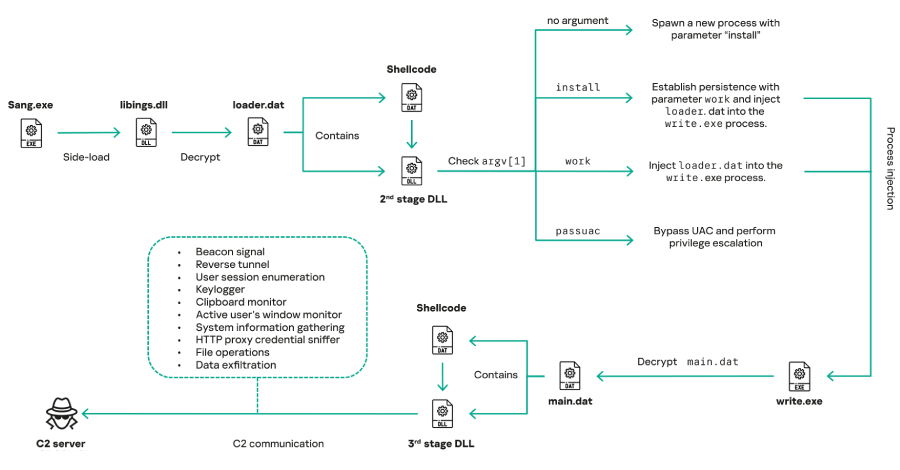
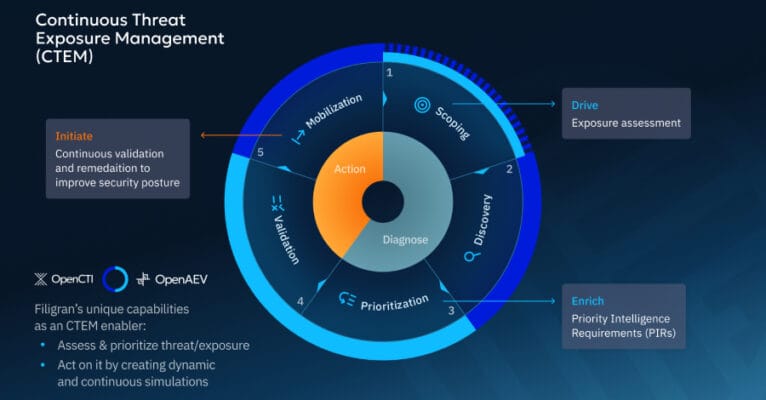
Pillar Security Research has discovered Operation Bizarre Bazaar, a massive cyberattack campaign led by a hacker known as Hecker. Between December 2025 and January 2026, over 35,000 sessions were recorded targeting AI systems to steal compute power and resell access via silver.inc. – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More