Iranian government-connected groups are deploying malware via the Telegram messaging app, taking aim at dissidents and other opponents of Tehran around the world, the FBI said in an alert Friday. The FBI said attackers linked to the Ministry of Intelligence and Security are behind the campaign, which stretches back to 2023. The bureau is escalating … Read More “FBI: Iranian hackers targeting opponents with Telegram malware – CyberScoop” »
Author: Tim Starks
North Korean Hacker Lands Remote IT Job, Caught After VPN Slip – Hackread – Cybersecurity News, Data Breaches, AI and More

New research from LevelBlue reveals how a suspected North Korean operative landed a remote IT role to fund national weapons programmes. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
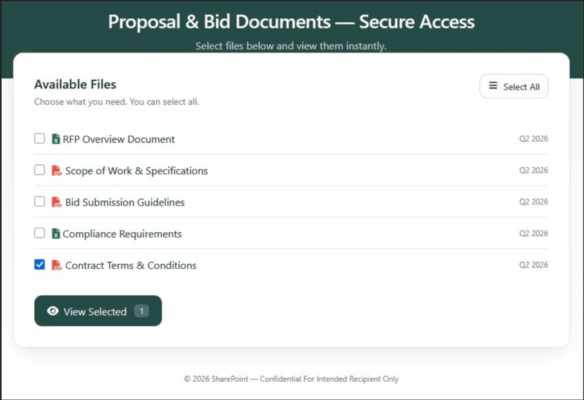
A phishing campaign tied to AI cloud-hosting service Railway has given hackers access to the Microsoft cloud accounts for hundreds of businesses, according to researchers at Huntress. Rich Mozeleski, product manager for Huntress’ identity team, told CyberScoop the campaign is currently tied to a smaller actor and approximately a dozen IP addresses, but has managed … Read More “An AI-powered phishing campaign has compromised hundreds of organizations – CyberScoop” »
Tycoon2FA phishing platform resumes activity post-takedown, leveraging AITM techniques to bypass MFA – Read More –
ISACA survey found that confusion over responsibility and lack of understanding around AI cyber-attacks makes containing them difficult – Read More –
Voice-based phishing, a form of social engineering where attackers call employees or IT help desks under false pretenses in an attempt to gain access to victim networks, surged in 2025, Mandiant said Monday in its annual M-Trends report. These points of intrusion, which have been a hallmark of attacks attributed to members of the cybercrime … Read More “The phone call is the new phishing email – CyberScoop” »
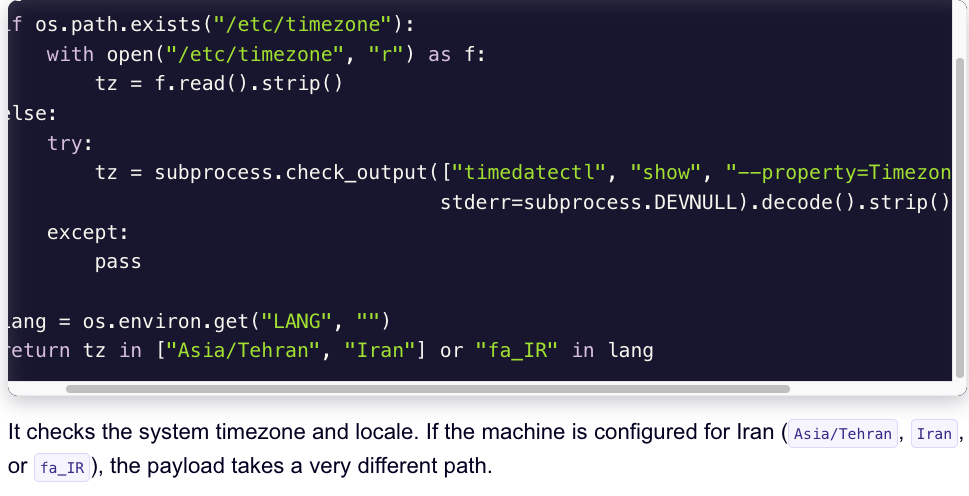
A financially motivated data theft and extortion group is attempting to inject itself into the Iran war, unleashing a worm that spreads through poorly secured cloud services and wipes data on infected systems that use Iran’s time zone or have Farsi set as the default language. Experts say the wiper campaign against Iran materialized this … Read More “‘CanisterWorm’ Springs Wiper Attack Targeting Iran – Krebs on Security” »
New Trivy Docker images 0.69.5 and 0.69.6 compromised with TeamPCP infostealer, impacting CI/CD scans – Read More –
High tech was the most frequently targeted industry in Mandiant investigations in 2025, overtaking financial services which led in 2023 and 2024 – Read More –
⚡ Weekly Recap: CI/CD Backdoor, FBI Buys Location Data, WhatsApp Ditches Numbers & More – The Hacker News
Another week, another reminder that the internet is still a mess. Systems people thought were secure are being broken in simple ways, showing many still ignore basic advisories. This edition covers a mix of issues: supply chain attacks hitting CI/CD setups, long-abused IoT devices being shut down, and exploits moving quickly from disclosure to real … Read More “⚡ Weekly Recap: CI/CD Backdoor, FBI Buys Location Data, WhatsApp Ditches Numbers & More – The Hacker News” »
We Found Eight Attack Vectors Inside AWS Bedrock. Here’s What Attackers Can Do with Them – The Hacker News
AWS Bedrock is Amazon’s platform for building AI-powered applications. It gives developers access to foundation models and the tools to connect those models directly to enterprise data and systems. That connectivity is what makes it powerful – but it’s also what makes Bedrock a target. When an AI agent can query your Salesforce instance, trigger … Read More “We Found Eight Attack Vectors Inside AWS Bedrock. Here’s What Attackers Can Do with Them – The Hacker News” »
Police Shut Down 373,000 Dark Web Sites in Single-Operator CSAM Network – Hackread – Cybersecurity News, Data Breaches, AI and More

Police shut down 373K dark web sites in a one-man CSAM and cybercrime network run by a 35-year-old man in China, with global probe ongoing. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Why Your Weather-Powered Design Tool Needs More Than Just an API Key – Hackread – Cybersecurity News, Data Breaches, AI and More

Weather-powered design tools need more than an API key. Learn how authentication, access control, and server-side calls keep… – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Global Crackdown Dismantles 4 Botnets Behind Major DDoS Attacks – Hackread – Cybersecurity News, Data Breaches, AI and More
Global crackdown dismantles Aisuru, KimWolf, JackSkid and Mossad botnets behind major DDoS attack campaigns targeting millions of devices worldwide. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
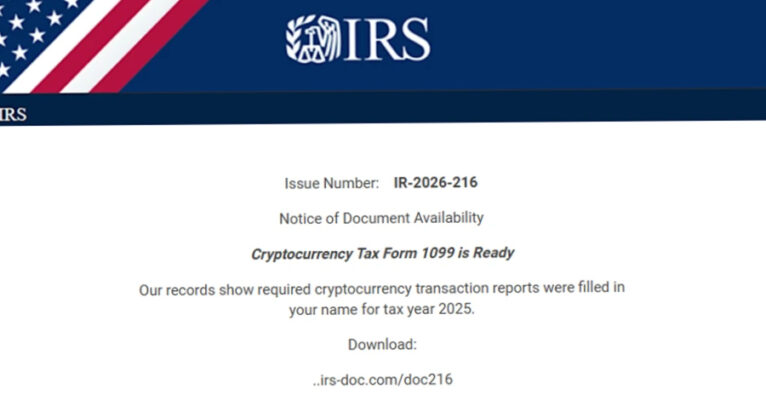
Microsoft has warned of fresh campaigns that are capitalizing on the upcoming tax season in the U.S. to harvest credentials and deliver malware. The email campaigns take advantage of the urgency and time-sensitive nature of emails to send phishing messages masquerading as refund notices, payroll forms, filing reminders, and requests from tax professionals to deceive … Read More “Microsoft Warns IRS Phishing Hits 29,000 Users, Deploys RMM Malware – The Hacker News” »
CISA added CVE-2026-20131 to its KEV catalog as it is being used in ransomware campaigns – Read More –
Cybersecurity researchers have uncovered malicious artifacts distributed via Docker Hub following the Trivy supply chain attack, highlighting the widening blast radius across developer environments. The last known clean release of Trivy on Docker Hub is 0.69.3. The malicious versions 0.69.4, 0.69.5, and 0.69.6 have since been removed from the container image library. “New image tags … Read More “Trivy Hack Spreads Infostealer via Docker, Triggers Worm and Kubernetes Wiper – The Hacker News” »
German-led policing effort against fraud operation disrupts countless CSAM and cybercrime sites – Read More –
Hackers Exploit CVE-2025-32975 (CVSS 10.0) to Hijack Unpatched Quest KACE SMA Systems – The Hacker News

Threat actors are suspected to be exploiting a maximum-severity security flaw impacting Quest KACE Systems Management Appliance (SMA), according to Arctic Wolf. The cybersecurity company said it observed malicious activity starting the week of March 9, 2026, in customer environments that’s consistent with the exploitation of CVE-2025-32975 on unpatched SMA systems exposed to the internet. … Read More “Hackers Exploit CVE-2025-32975 (CVSS 10.0) to Hijack Unpatched Quest KACE SMA Systems – The Hacker News” »
Politics live: new standards for datacentres being built in Australia; report warns of drone threat – Data and computer security | The Guardian

Labor under pressure over fuel crisis as federal parliament returns. Follow updates live Get our breaking news email, free app or daily news podcast Should Australians work from home to save fuel? James Glenday then asks Tim Ayres whether he thinks Australians should consider working from home to conserve fuel. Countries like Sri Lanka have … Read More “Politics live: new standards for datacentres being built in Australia; report warns of drone threat – Data and computer security | The Guardian” »
Threat actors affiliated with Russian Intelligence Services are conducting phishing campaigns to compromise commercial messaging applications (CMAs) like WhatsApp and Signal to seize control of accounts belonging to individuals with high intelligence value, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) and Federal Bureau of Investigation (FBI) said Friday. “The campaign – Read More – … Read More “FBI Warns Russian Hackers Target Signal, WhatsApp in Mass Phishing Attacks – The Hacker News” »
Oracle Patches Critical CVE-2026-21992 Enabling Unauthenticated RCE in Identity Manager – The Hacker News

Oracle has released security updates to address a critical security flaw impacting Identity Manager and Web Services Manager that could be exploited to achieve remote code execution. The vulnerability, tracked as CVE-2026-21992, carries a CVSS score of 9.8 out of a maximum of 10.0. “This vulnerability is remotely exploitable without authentication,” Oracle said in an … Read More “Oracle Patches Critical CVE-2026-21992 Enabling Unauthenticated RCE in Identity Manager – The Hacker News” »
CISA Flags Apple, Craft CMS, Laravel Bugs in KEV, Orders Patching by April 3, 2026 – The Hacker News
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday added five security flaws impacting Apple, Craft CMS, and Laravel Livewire to its Known Exploited Vulnerabilities (KEV) catalog, urging federal agencies to patch them by April 3, 2026. The vulnerabilities that have come under exploitation are listed below – CVE-2025-31277 (CVSS score: 8.8) – A … Read More “CISA Flags Apple, Craft CMS, Laravel Bugs in KEV, Orders Patching by April 3, 2026 – The Hacker News” »
Trivy Supply Chain Attack Triggers Self-Spreading CanisterWorm Across 47 npm Packages – The Hacker News
The threat actors behind the supply chain attack targeting the popular Trivy scanner are suspected to be conducting follow-on attacks that have led to the compromise of a large number of npm packages with a previously undocumented self-propagating worm dubbed CanisterWorm. The name is a reference to the fact that the malware uses an ICP … Read More “Trivy Supply Chain Attack Triggers Self-Spreading CanisterWorm Across 47 npm Packages – The Hacker News” »
Hacker Group LAPSUS$ Claims Alleged AstraZeneca Data Breach – Hackread – Cybersecurity News, Data Breaches, AI and More
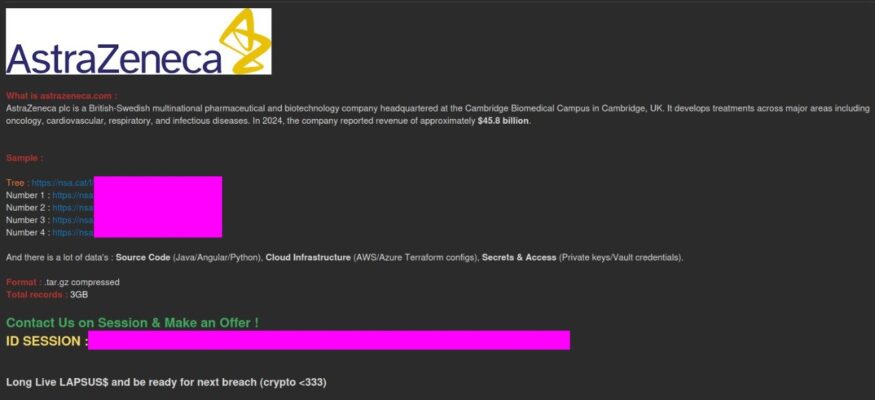
LAPSUS$ claims it breached AstraZeneca, offering alleged source code, credentials, cloud configs, and employee data for sale in leaked samples. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Russian intelligence-affiliated hackers have gained access to thousands of users’ messaging apps with a global phishing campaign, the FBI and the Cybersecurity and Infrastructure Security Agency warned in a public service announcement on Friday. The high-value targets they’re pursuing include current and former U.S. government officials, political figures, military personnel and journalists, the two agencies … Read More “FBI, CISA issue PSA on Russian intelligence campaign to target messaging apps – CyberScoop” »
Trivy Security Scanner GitHub Actions Breached, 75 Tags Hijacked to Steal CI/CD Secrets – The Hacker News

Trivy, a popular open-source vulnerability scanner maintained by Aqua Security, was compromised a second time within the span of a month to deliver malware that stole sensitive CI/CD secrets. The latest incident impacted GitHub Actions “aquasecurity/trivy-action” and “aquasecurity/setup-trivy,” which are used to scan Docker container images for vulnerabilities and set up GitHub Actions workflow – … Read More “Trivy Security Scanner GitHub Actions Breached, 75 Tags Hijacked to Steal CI/CD Secrets – The Hacker News” »
Three American men were sentenced Friday for crimes they committed in furtherance of North Korea’s vast scheme to get operatives hired at U.S. companies, the Justice Department said. The trio — Audricus Phagnasay, 25, Jason Salazar, 30, and Alexander Paul Travis, 35 — pleaded guilty in November to wire fraud conspiracy for providing U.S. identities … Read More “Trio sentenced for facilitating North Korean IT worker scheme from their homes – CyberScoop” »
Post Content – Read More – IC3.gov News
Researchers and threat hunters are scrambling to contain a maximum-severity defect in Ubiquiti’s UniFi Network Application that attackers could exploit to take over user accounts by accessing and manipulating files. The path-traversal vulnerability — CVE-2026-22557 — affects software used to manage UniFi networking devices, including access points, gateways and switches. The vendor disclosed and released … Read More “Ubiquiti defect poses account takeover risk for UniFi Networking Application users – CyberScoop” »
Critical Langflow Flaw CVE-2026-33017 Triggers Attacks within 20 Hours of Disclosure – The Hacker News

A critical security flaw impacting Langflow has come under active exploitation within 20 hours of public disclosure, highlighting the speed at which threat actors weaponize newly published vulnerabilities. The security defect, tracked as CVE-2026-33017 (CVSS score: 9.3), is a case of missing authentication combined with code injection that could result in remote code execution. “The … Read More “Critical Langflow Flaw CVE-2026-33017 Triggers Attacks within 20 Hours of Disclosure – The Hacker News” »
Pedestrians crossing a street in Denver, Colorado, got rather more than they bargained for last weekend, when the audio signals at two crosswalks began broadcasting a political message alongside their usual walking instructions. Read more in my article on the Hot for Security blog. – Read More – GRAHAM CLULEY
Apple is urging users who are still running an outdated version of iOS to update their iPhones to secure against web-based attacks carried out via powerful exploit kits like Coruna and DarkSword. These attacks employ malicious web content to target out-of-date versions of iOS, triggering an infection chain that leads to the theft of sensitive … Read More “Apple Warns Older iPhones Vulnerable to Coruna, DarkSword Exploit Kit Attacks – The Hacker News” »
Why Image Format Conversion Is Becoming a Practical Issue in Web Security and Performance – Hackread – Cybersecurity News, Data Breaches, AI and More
WebP boosts performance raises compatibility issues, making image format conversion to PNG essential for secure, flexible, and efficient web workflows today. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Authorities seized infrastructure powering four botnets that hijacked a combined three million devices and launched more than 300,000 DDoS attacks collectively, the Justice Department said Thursday. The botnets — Aisuru, Kimwolf, JackSkid and Mossad — enabled operators to sell access to the infected devices for various cybercrimes. The aftermath spanned thousands of attacks, including some … Read More “Justice Department disrupts botnet networks that hijacked 3 million devices – CyberScoop” »
New Fake Zoom Meeting Invite Scam Spreads Malware on Windows PCs – Hackread – Cybersecurity News, Data Breaches, AI and More
Cybersecurity researchers at Sublime Security have discovered a new scam that uses realistic, interactive JavaScript-based Zoom meeting invites to trick users into installing malware. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Sansec is warning of a critical security flaw in Magento’s REST API that could allow unauthenticated attackers to upload arbitrary executables and achieve code execution and account takeover. The vulnerability has been codenamed PolyShell by Sansec owing to the fact that the attack hinges on disguising malicious code as an image. There is no evidence … Read More “Magento PolyShell Flaw Enables Unauthenticated Uploads, RCE and Account Takeover – The Hacker News” »
Google Adds 24-Hour Wait for Unverified App Sideloading to Reduce Malware and Scams – The Hacker News
Google on Thursday announced a new “advanced flow” for Android sideloading that requires a mandatory 24-hour wait period to install apps from unverified developers in an attempt to balance openness with safety. The new changes come against the backdrop of a developer verification mandate the tech giant announced last year that requires all Android apps … Read More “Google Adds 24-Hour Wait for Unverified App Sideloading to Reduce Malware and Scams – The Hacker News” »
Artificial Intelligence (AI) is changing how individuals and organizations conduct many activities, including how cybercriminals carry out phishing attacks and iterate on malware. Now, cybercriminals are using AI to generate personalized phishing emails, deepfakes and malware that evade traditional detection by impersonating normal user activity and bypassing legacy security models. As a result, – Read … Read More “The Importance of Behavioral Analytics in AI-Enabled Cyber Attacks – The Hacker News” »
A ransomware gang that claims to be a group of “investigative journalists”? Meet LeakNet – the group using fake CAPTCHA pages to trick employees into hacking themselves. Read more in my article on the Fortra blog. – Read More – GRAHAM CLULEY
Sysdig details how threat actors exploited a critical CVE in Langflow in less than a day – Read More –
The National Crime Agency’s director general warns that technology is rapidly reshaping crime – Read More –
DoJ Disrupts 3 Million-Device IoT Botnets Behind Record 31.4 Tbps Global DDoS Attacks – The Hacker News
The U.S. Department of Justice (DoJ) on Thursday announced the disruption of command-and-control (C2) infrastructure used by several Internet of Things (IoT) botnets like AISURU, Kimwolf, JackSkid, and Mossad as part of a court-authorized law enforcement operation. The effort also saw authorities from Canada and Germany targeting the operators behind these botnets, with a number … Read More “DoJ Disrupts 3 Million-Device IoT Botnets Behind Record 31.4 Tbps Global DDoS Attacks – The Hacker News” »
A 27-year-old North Carolina man was found guilty of six counts of extortion for a series of crimes he committed while working as a data analyst contractor for a D.C.-based international technology company, the Justice Department said Thursday. Cameron Nicholas Curry, also known as “Loot,” stole a trove of corporate data, including sensitive employee and … Read More “North Carolina tech worker found guilty of insider attack netting $2.5M ransom – CyberScoop” »
The U.S. Justice Department joined authorities in Canada and Germany in dismantling the online infrastructure behind four highly disruptive botnets that compromised more than three million Internet of Things (IoT) devices, such as routers and web cameras. The feds say the four botnets — named Aisuru, Kimwolf, JackSkid and Mossad — are responsible for a … Read More “Feds Disrupt IoT Botnets Behind Huge DDoS Attacks – Krebs on Security” »
For the past decade, cybersecurity experts in the federal government have argued that trust, or a lack of it, was key to developing effective security policies for agency systems and data. But today, cybercriminals and state-sponsored hackers are using artificial intelligence to develop and launch cyberattacks more quickly and efficiently. Governments and businesses are facing … Read More “Can Zero Trust survive the AI era? – CyberScoop” »
Cybersecurity researchers have flagged a new malware dubbed Speagle that hijacks the functionality and infrastructure of a legitimate program called Cobra DocGuard. “Speagle is designed to surreptitiously harvest sensitive information from infected computers and transmit it to a Cobra DocGuard server that has been compromised by the attackers, masking the data exfiltration process as legitimate … Read More “Speagle Malware Hijacks Cobra DocGuard to Steal Data via Compromised Servers – The Hacker News” »
54 EDR Killers Use BYOVD to Exploit 34 Signed Vulnerable Drivers and Disable Security – The Hacker News
A new analysis of endpoint detection and response (EDR) killers has revealed that 54 of them leverage a technique known as bring your own vulnerable driver (BYOVD) by abusing a total of 34 vulnerable drivers. EDR killer programs have been a common presence in ransomware intrusions as they offer a way for affiliates to neutralize … Read More “54 EDR Killers Use BYOVD to Exploit 34 Signed Vulnerable Drivers and Disable Security – The Hacker News” »
Federal cyber officials aren’t seeing a significant change in attacks tied to Iran since the conflict there began, at least not yet, but they are on the lookout for any uptick and are focusing on the Stryker attack in particular. Terry Kalka — director of the Defense Industrial Base Collaborative Information Sharing Environment at The … Read More “Feds keep eyes peeled for Iran cyberattacks, respond to Stryker breach – CyberScoop” »
Hastalamuerte leaks The Gentlemen RaaS ops: FortiGate exploits, BYOVD evasion, Qilin split tactics – Read More –