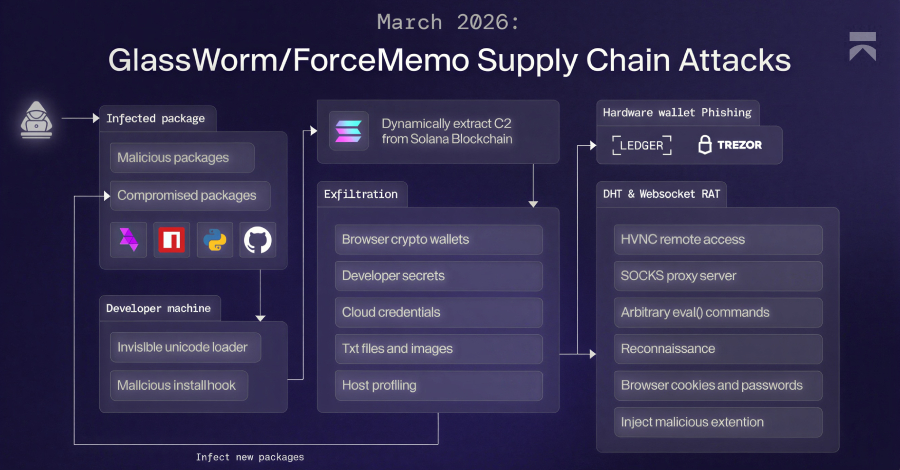
ThreatsDay Bulletin: PQC Push, AI Vuln Hunting, Pirated Traps, Phishing Kits & 20 More Stories – The Hacker News

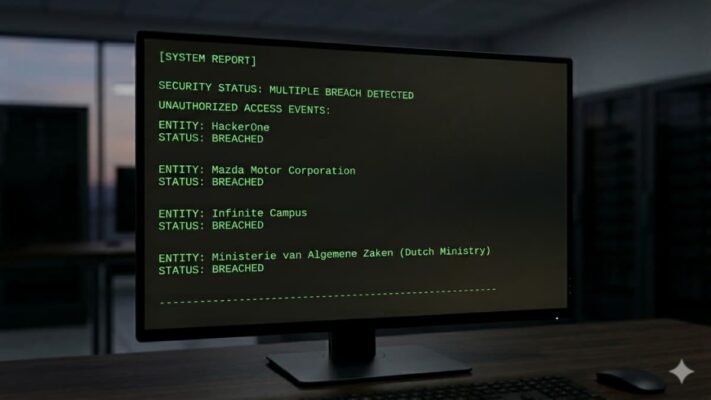
Some weeks in security feel loud. This one feels sneaky. Less big dramatic fireworks, more of that slow creeping sense that too many people are getting way too comfortable abusing things they probably shouldn’t even be touching. There’s a little bit of everything in this one, too. Weird delivery tricks, old problems coming back in … Read More “ThreatsDay Bulletin: PQC Push, AI Vuln Hunting, Pirated Traps, Phishing Kits & 20 More Stories – The Hacker News” »




![[Webinar] Stop Guessing. Learn to Validate Your Defenses Against Real Attacks – The Hacker News](https://attackfeed.com/wp-content/uploads/2026/03/validate-3lC6Rk.jpg)