ShadowSyndicate cluster expands with new SSH fingerprints connecting servers to other ransomware ops – Read More –
Author: Joe-W
MomentProof Deploys Patented Digital Asset Protection – Hackread – Cybersecurity News, Data Breaches, AI and More

Washington, DC, 4th February 2026, CyberNewsWire – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Cofense claims AI is making phishing emails more personalized and sophisticated – Read More –
Pillar Security discovered two new critical vulnerabilities in n8n that could lead to supply chain compromise, credential harvesting and complete takeover attacks – Read More –
Exposed AWS Credentials Lead to AI-Assisted Cloud Breach in 8 Minutes – Hackread – Cybersecurity News, Data Breaches, AI and More

Researchers recently tracked a high-speed cloud attack where an intruder gained full admin access in just eight minutes. Discover how AI automation and a simple storage error led to a major security breach. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Orchid Security Introduces Continuous Identity Observability for Enterprise Applications – The Hacker News
An innovative approach to discovering, analyzing, and governing identity usage beyond traditional IAM controls. The Challenge: Identity Lives Outside the Identity Stack Identity and access management tools were built to govern users and directories. Modern enterprises run on applications. Over time, identity logic has moved into application code, APIs, service accounts, and custom authentication – … Read More “Orchid Security Introduces Continuous Identity Observability for Enterprise Applications – The Hacker News” »
Many incident response failures do not come from a lack of tools, intelligence, or technical skills. They come from what happens immediately after detection, when pressure is high, and information is incomplete. I have seen IR teams recover from sophisticated intrusions with limited telemetry. I have also seen teams lose control of investigations they should … Read More “The First 90 Seconds: How Early Decisions Shape Incident Response Investigations – The Hacker News” »
CISA has added a critical CVE in SolarWinds Web Help Desk to its KEV Catalog – Read More –
Phishing Campaigns Abuse Trusted Cloud Platforms, Raising New Risks for Enterprises – Hackread – Cybersecurity News, Data Breaches, AI and More

ANY.RUN experts report a surge in phishing campaigns abusing trusted cloud and CDN platforms to bypass security controls and target enterprise users. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Microsoft has warned that information-stealing attacks are “rapidly expanding” beyond Windows to target Apple macOS environments by leveraging cross-platform languages like Python and abusing trusted platforms for distribution at scale. The tech giant’s Defender Security Research Team said it observed macOS-targeted infostealer campaigns using social engineering techniques such as ClickFix since – Read More – … Read More “Microsoft Warns Python Infostealers Target macOS via Fake Ads and Installers – The Hacker News” »
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday added a critical security flaw impacting SolarWinds Web Help Desk (WHD) to its Known Exploited Vulnerabilities (KEV) catalog, flagging it as actively exploited in attacks. The vulnerability, tracked as CVE-2025-40551 (CVSS score: 9.8), is a untrusted data deserialization vulnerability that could pave the way for … Read More “CISA Adds Actively Exploited SolarWinds Web Help Desk RCE to KEV Catalog – The Hacker News” »
The Eclipse Foundation, which maintains the Open VSX Registry, has announced plans to enforce security checks before Microsoft Visual Studio Code (VS Code) extensions are published to the open-source repository to combat supply chain threats. The move marks a shift from a reactive to a proactive approach to ensure that malicious extensions don’t end up … Read More “Eclipse Foundation Mandates Pre-Publish Security Checks for Open VSX Extensions – The Hacker News” »
One Identity Appoints Gihan Munasinghe as Chief Technology Officer – Hackread – Cybersecurity News, Data Breaches, AI, and More

Alisa Viejo, United States, 4th February 2026, CyberNewsWire – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More
More than a year after national security officials revealed that Chinese hackers had systematically infiltrated U.S. telecommunications networks, the top Senate Democrat on the committee overseeing the industry is calling for hearings with executives from the nation’s biggest telecom companies. In a public letter released Tuesday, Sen. Maria Cantwell, D-Wash., called for the CEOs of … Read More “Cantwell claims telecoms blocked release of Salt Typhoon report – CyberScoop” »
What’s next for DHS’s forthcoming replacement critical infrastructure protection panel, AI information sharing – CyberScoop

A revised government-industry council devoted to critical infrastructure protection could be set up to have broader and more specific discussions on things like cybersecurity and threats to hardware and software that monitor and control industrial processes, known as operational technology (OT). A top official at the Cybersecurity and Infrastructure Security Agency (CISA), Nick Andersen, said … Read More “What’s next for DHS’s forthcoming replacement critical infrastructure protection panel, AI information sharing – CyberScoop” »
Attackers are again focusing on a familiar target in the network edge space, actively exploiting two critical zero-day vulnerabilities in Ivanti software that allows administrators to set mobile device and application controls. The vulnerabilities — CVE-2026-1281 and CVE-2026-1340 — each carry a CVSS rating of 9.8 and allow unauthenticated users to execute code remotely in … Read More “Ivanti’s EPMM is under active attack, thanks to two critical zero-days – CyberScoop” »
Op Neusploit: Russian APT28 Uses Microsoft Office Flaw in Malware Attacks – Hackread – Cybersecurity News, Data Breaches, AI, and More

A new campaign by the Russian-linked group APT28, called Op Neusploit, exploits a Microsoft Office flaw to steal emails for remote control of devices in Ukraine, Slovakia, and Romania. – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More
Docker Fixes Critical Ask Gordon AI Flaw Allowing Code Execution via Image Metadata – The Hacker News

Cybersecurity researchers have disclosed details of a now-patched security flaw impacting Ask Gordon, an artificial intelligence (AI) assistant built into Docker Desktop and the Docker Command-Line Interface (CLI), that could be exploited to execute code and exfiltrate sensitive data. The critical vulnerability has been codenamed DockerDash by cybersecurity company Noma Labs. It was addressed by … Read More “Docker Fixes Critical Ask Gordon AI Flaw Allowing Code Execution via Image Metadata – The Hacker News” »
The Trump administration needs help from industry to reduce the cybersecurity regulatory burden and to back important cyber legislation on Capitol Hill, among other areas, National Cyber Director Sean Cairncross said Tuesday. “You know your regulatory scheme better than I do: Where there’s friction, where there’s frustration with information sharing, what sort of information is … Read More “Sean Cairncross’ cybersecurity agenda: less regulation, more cooperation – CyberScoop” »
40,000 WordPress sites are vulnerable to SQL injection in Quiz and Survey Master plugin – Read More –
A security researcher found 386 malicious ‘skills’ published on ClawHub, a skill repository for the popular OpenClaw AI assistant project – Read More –
Meet Moltbook, the Social Platform Where AI Agents Talk and Humans Watch – Hackread – Cybersecurity News, Data Breaches, AI, and More
Moltbook is a new social platform where AI agents post and interact while humans observe, raising questions about autonomy, security, and agent behavior. – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More
UK Data Protection Watchdog has “serious concerns” over data privacy on Elon Musk’s social platform – Read More –
DockerDash vulnerability allows RCE and data exfiltration via unverified metadata in Ask Gordon – Read More –
Threat actors have been observed exploiting a critical security flaw impacting the Metro Development Server in the popular “@react-native-community/cli” npm package. Cybersecurity company VulnCheck said it first observed exploitation of CVE-2025-11953 (aka Metro4Shell) on December 21, 2025. With a CVSS score of 9.8, the vulnerability allows remote unauthenticated attackers to execute arbitrary – Read More … Read More “Hackers Exploit Metro4Shell RCE Flaw in React Native CLI npm Package – The Hacker News” »
Most security teams today are buried under tools. Too many dashboards. Too much noise. Not enough real progress. Every vendor promises “complete coverage” or “AI-powered automation,” but inside most SOCs, teams are still overwhelmed, stretched thin, and unsure which tools are truly pulling their weight. The result? Bloated stacks, missed signals, and mounting pressure to … Read More “[Webinar] The Smarter SOC Blueprint: Learn What to Build, Buy, and Automate – The Hacker News” »
A new ransomware-as-a-service operation dubbed “Vect” features custom malware – Read More –
Elon Musk and X’s former CEO were summoned for voluntary interviews in Paris on April 20, 2026 – Read More –
Recent major cloud service outages have been hard to miss. High-profile incidents affecting providers such as AWS, Azure, and Cloudflare have disrupted large parts of the internet, taking down websites and services that many other systems depend on. The resulting ripple effects have halted applications and workflows that many organizations rely on every day. For … Read More “When Cloud Outages Ripple Across the Internet – The Hacker News” »
Everest Ransomware Claims 90GB Data Theft Involving Legacy Polycom Systems – Hackread – Cybersecurity News, Data Breaches, AI, and More
Everest ransomware claims a breach involving legacy Polycom systems later acquired by HP Inc., alleging the theft of 90GB of internal data. – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More
Multi-stage attack begins with fake message relating to business requests and evades detection with link hidden in a PDF – Read More –
Wiz Security claims Moltbook misconfiguration allowed full read and write access – Read More –
The Russia-linked state-sponsored threat actor known as APT28 (aka UAC-0001) has been attributed to attacks exploiting a newly disclosed security flaw in Microsoft Office as part of a campaign codenamed Operation Neusploit. Zscaler ThreatLabz said it observed the hacking group weaponizing the shortcoming on January 29, 2026, in attacks targeting users in Ukraine, Slovakia, and … Read More “APT28 Uses Microsoft Office CVE-2026-21509 in Espionage-Focused Malware Attacks – The Hacker News” »
CSPM tools are big business. Could they be the answer to your cloud configuration problems? – Read More – NCSC Feed
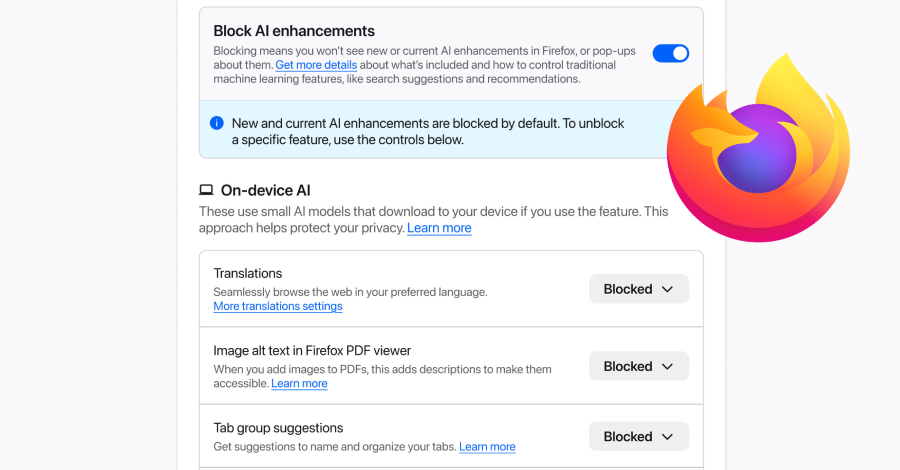
Mozilla on Monday announced a new controls section in its Firefox desktop browser settings that allows users to completely turn off generative artificial intelligence (GenAI) features. “It provides a single place to block current and future generative AI features in Firefox,” Ajit Varma, head of Firefox, said. “You can also review and manage individual AI … Read More “Mozilla Adds One-Click Option to Disable Generative AI Features in Firefox – The Hacker News” »
A China-linked threat actor known as Lotus Blossom has been attributed with medium confidence to the recently discovered compromise of the infrastructure hosting Notepad++. The attack enabled the state-sponsored hacking group to deliver a previously undocumented backdoor codenamed Chrysalis to users of the open-source editor, according to new findings from Rapid7. The development comes shortly … Read More “Notepad++ Hosting Breach Attributed to China-Linked Lotus Blossom Hacking Group – The Hacker News” »
The Digital Personal Data Protection (DPDP) Act of India is one of the most significant regulatory changes in the… The post 90-Day DPDP Readiness Plan for Indian Enterprises appeared first on JISA Softech Pvt Ltd. – Read More – JISA Softech Pvt Ltd
It’s no secret that the Trump administration has radically altered the federal government’s relationship with state election officials since being sworn into power last year. While his first term included the creation of the Cybersecurity and Infrastructure Security Agency and the distribution of hundreds of millions in congressional funding sent to help states upgrade election … Read More “As feds pull back, states look inward for election security support – CyberScoop” »
Phishing Scam Uses Clean Emails and PDFs to Steal Dropbox Logins – Hackread – Cybersecurity News, Data Breaches, AI, and More

A multi-stage phishing campaign is targeting business users by exploiting Vercel cloud storage, PDF attachments, and Telegram bots to steal Dropbox credentials. – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More
A China-based threat group operating for almost two decades broke into the internal systems of Notepad++, an extremely popular open source-code editor, to spy on a select group of targeted users, researchers at Rapid7 said Monday. Don Ho, the author and maintainer of the open-source tool, said independent security researchers confirmed a China state-sponsored group … Read More “China-based espionage group compromised Notepad++ for six months – CyberScoop” »
A security audit of 2,857 skills on ClawHub has found 341 malicious skills across multiple campaigns, according to new findings from Koi Security, exposing users to new supply chain risks. ClawHub is a marketplace designed to make it easy for OpenClaw users to find and install third-party skills. It’s an extension to the OpenClaw project, … Read More “Researchers Find 341 Malicious ClawHub Skills Stealing Data from OpenClaw Users – The Hacker News” »
Notepad++ Updates Delivered Malware After Hosting Provider Breach – Hackread – Cybersecurity News, Data Breaches, AI, and More
A months-long breach allowed Chinese State-sponsored hackers to hijack Notepad++ updates in 2025, exposing users to malware via a compromised hosting provider. – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More
A high-severity security flaw has been disclosed in OpenClaw (formerly referred to as Clawdbot and Moltbot) that could allow remote code execution (RCE) through a crafted malicious link. The issue, which is tracked as CVE-2026-25253 (CVSS score: 8.8), has been addressed in version 2026.1.29 released on January 30, 2026. It has been described as a … Read More “OpenClaw Bug Enables One-Click Remote Code Execution via Malicious Link – The Hacker News” »
Microsoft has announced a three-phase approach to phase out New Technology LAN Manager (NTLM) as part of its efforts to shift Windows environments toward stronger, Kerberos-based options. The development comes more than two years after the tech giant revealed its plans to deprecate the legacy technology, citing its susceptibility to weaknesses that could facilitate relay … Read More “Microsoft Begins NTLM Phase-Out With Three-Stage Plan to Move Windows to Kerberos – The Hacker News” »
A prolific data ransom gang that calls itself Scattered Lapsus Shiny Hunters (SLSH) has a distinctive playbook when it seeks to extort payment from victim firms: Harassing, threatening and even swatting executives and their families, all while notifying journalists and regulators about the extent of the intrusion. Some victims reportedly are paying — perhaps as … Read More “Please Don’t Feed the Scattered Lapsus Shiny Hunters – Krebs on Security” »
NSA released new guidelines to help organizations achieve target-level Zero Trust maturity – Read More –
Spotify and Major Music Labels Sue Anna’s Archive for $13 Trillion – Hackread – Cybersecurity News, Data Breaches, AI, and More

Spotify and the Big Three labels have filed a record-breaking $13 trillion lawsuit against Anna’s Archive over a massive music data scrape. Find out what this means for the future of digital music. – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More
Ivanti Issues Urgent Fix for Critical Zero-Day Flaws Under Active Attack – Hackread – Cybersecurity News, Data Breaches, AI, and More

Ivanti has disclosed two critical remote code execution (RCE) flaws (CVE-2026-1281 & CVE-2026-1340) in its EPMM software. – Read More – Hackread – Cybersecurity News, Data Breaches, AI, and More
A supply chain attack on Notepad++ update process was linked to compromised hosting infrastructure – Read More –
For mid-market organizations, cybersecurity is a constant balancing act. Proactive, preventative security measures are essential to protect an expanding attack surface. Combined with effective protection that blocks threats, they play a critical role in stopping cyberattacks before damage is done. The challenge is that many security tools add complexity and cost that most mid-market businesses … Read More “Securing the Mid-Market Across the Complete Threat Lifecycle – The Hacker News” »















![[Webinar] The Smarter SOC Blueprint: Learn What to Build, Buy, and Automate – The Hacker News](https://attackfeed.com/wp-content/uploads/2026/02/soc-OxCeCE.jpg)