Cybersecurity researchers have disclosed details of an emergent ransomware family dubbed Reynolds that comes embedded with a built-in bring your own vulnerable driver (BYOVD) component for defense evasion purposes within the ransomware payload itself. BYOVD refers to an adversarial technique that abuses legitimate but flawed driver software to escalate privileges and disable Endpoint Detection – … Read More “Reynolds Ransomware Embeds BYOVD Driver to Disable EDR Security Tools – The Hacker News” »
Author: [email protected] (The Hacker News)
Are ransomware and encryption still the defining signals of modern cyberattacks, or has the industry been too fixated on noise while missing a more dangerous shift happening quietly all around them? According to Picus Labs’ new Red Report 2026, which analyzed over 1.1 million malicious files and mapped 15.5 million adversarial actions observed across 2025, … Read More “From Ransomware to Residency: Inside the Rise of the Digital Parasite – The Hacker News” »
ZeroDayRAT is a new mobile spyware targeting Android and iOS, offering attackers persistent access – Read More –
Picus Security warns of the increasingly sophisticated ways malicious activity is staying hidden – Read More –
Pride Month Phishing Targets Employees via Trusted Email Services – Hackread – Cybersecurity News, Data Breaches, AI and More

Attackers are using Pride Month themed phishing emails to target employees worldwide, abusing trusted email platforms like SendGrid to harvest credentials. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Operation Cyber Guardian was Singapore’s largest and longest running anti-cyber threat law enforcement operation – Read More –
SmarterTools confirmed last week that the Warlock (aka Storm-2603) ransomware gang breached its network by exploiting an unpatched SmarterMail instance. The incident took place on January 29, 2026, when a mail server that was not updated to the latest version was compromised, the company’s Chief Commercial Officer, Derek Curtis, said. “Prior to the breach, we … Read More “Warlock Ransomware Breaches SmarterTools Through Unpatched SmarterMail Server – The Hacker News” »
January 5, 2026, Seattle, USA — ZAST.AI announced the completion of a $6 million Pre-A funding round. This investment came from the well-known investment firm Hillhouse Capital, bringing ZAST.AI’s total funding close to $10 million. This marks a recognition from leading capital markets of a new solution: ending the era of high false positive rates … Read More “ZAST.AI Raises $6M Pre-A to Scale “Zero False Positive” AI-Powered Code Security – The Hacker News” »
NCSC call firms to ‘act now’ following disruptive malware attacks targeting Polish energy providers – Read More –
Navigating MiCA: A Practical Compliance Guide for European CASPs – Hackread – Cybersecurity News, Data Breaches, AI and More

MiCA creates a single EU crypto rulebook, replacing national regimes with unified licensing, capital, and compliance rules for all CASPs. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
The European Commission and government agencies in Finland and the Netherlands have suffered potentially related breaches – Read More –
The Netherlands’ Dutch Data Protection Authority (AP) and the Council for the Judiciary confirmed both agencies (Rvdr) have disclosed that their systems were impacted by cyber attacks that exploited the recently disclosed security flaws in Ivanti Endpoint Manager Mobile (EPMM), according to a notice sent to the country’s parliament on Friday. “On January 29, the … Read More “Dutch Authorities Confirm Ivanti Zero-Day Exploit Exposed Employee Contact Data – The Hacker News” »
How to ensure the ‘organisational memory’ of past vulnerabilities is not lost. – Read More – NCSC Feed
Apple Sends Alert – iPhones are at Risk – Da Vinci Cybersecurity: Leading Cyber Security Services in South Africa.

Around 1.6 billion people around the world have iPhones, and while Apple is usually diligent regarding security, there are two major problems that have surfaced. These problems leave iPhone users completely vulnerable to cyber criminal attacks and if users don’t address, they can steal all of your personal data and even your financial information. The … Read More “Apple Sends Alert – iPhones are at Risk – Da Vinci Cybersecurity: Leading Cyber Security Services in South Africa.” »
Fortinet has released security updates to address a critical flaw impacting FortiClientEMS that could lead to the execution of arbitrary code on susceptible systems. The vulnerability, tracked as CVE-2026-21643, has a CVSS rating of 9.1 out of a maximum of 10.0. “An improper neutralization of special elements used in an SQL Command (‘SQL Injection’) vulnerability … Read More “Fortinet Patches Critical SQLi Flaw Enabling Unauthenticated Code Execution – The Hacker News” »
The Digital Personal Data Protection (DPDP) Act in India transforms the privacy compliance documentation of companies to user experience… The post Designing DPDP Compliant Consent and Notice Flows appeared first on JISA Softech Pvt Ltd. – Read More – JISA Softech Pvt Ltd
The Trump administration has made U.S. dominance in artificial intelligence a national priority, but some critics say a light-touch approach to regulating security and safety in U.S. models is making it harder to promote adoption in other countries. White House officials have said since taking office that Trump intended to move away from predecessor Joe … Read More “Critics warn America’s ‘move fast’ AI strategy could cost it the global market – CyberScoop” »
Hackers Deliver Global Group Ransomware Offline via Phishing Emails – Hackread – Cybersecurity News, Data Breaches, AI and More

Global Group ransomware is delivered through phishing emails and can encrypt files offline without any internet connection. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Ivanti customers, including major government agencies, face mounting pressure as attackers expand their scope of targets to exploit a pair of vulnerabilities the vendor disclosed last week after in-the-wild attacks already occurred. The Netherlands’ Dutch Data Protection Authority and the Council for the Judiciary confirmed both agencies were impacted by attacks linked to the Ivanti … Read More “Fallout from latest Ivanti zero-days spreads to nearly 100 victims – CyberScoop” »
Cyber Attack Hits European Commission Staff Mobile Systems – Hackread – Cybersecurity News, Data Breaches, AI and More

The European Commission reports a cyber attack on its central mobile infrastructure that may have exposed staff names and phone numbers. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
The Cyber Security Agency (CSA) of Singapore on Monday revealed that the China-nexus cyber espionage group known as UNC3886 targeted its telecommunications sector. “UNC3886 had launched a deliberate, targeted, and well-planned campaign against Singapore’s telecommunications sector,” CSA said. “All four of Singapore’s major telecommunications operators (‘telcos’) – M1, SIMBA Telecom, Singtel, and – Read More … Read More “China-Linked UNC3886 Targets Singapore Telecom Sector in Cyber Espionage Campaign – The Hacker News” »
Security researchers from LayerX identified a new flaw in 50 Claude Desktop Extensions that could lead to unauthorized remote code execution – Read More –
Criminal IP Integrates with IBM QRadar to Deliver Real-Time Threat Intelligence Across SIEM and SOAR – Hackread – Cybersecurity News, Data Breaches, AI and More

Torrance, United States / California, 9th February 2026, CyberNewswire – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
VoidLink, a Linux-based C2 framework, facilitates credential theft, data exfiltration across clouds – Read More –
Two Connecticut men face federal charges for a $3m scheme targeting online gambling platforms – Read More –
SolarWinds Web Help Desk Exploited for RCE in Multi-Stage Attacks on Exposed Servers – The Hacker News

Microsoft has revealed that it observed a multi‑stage intrusion that involved the threat actors exploiting internet‑exposed SolarWinds Web Help Desk (WHD) instances to obtain initial access and move laterally across the organization’s network to other high-value assets. That said, the Microsoft Defender Security Research Team said it’s not clear whether the activity weaponized recently – … Read More “SolarWinds Web Help Desk Exploited for RCE in Multi-Stage Attacks on Exposed Servers – The Hacker News” »
Hackers Use Signal QR Codes to Spy on Military and Political Leaders – Hackread – Cybersecurity News, Data Breaches, AI and More

Hackers are using Signal QR codes and fake support scams to spy on military and political leaders, German security agencies warn. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
⚡ Weekly Recap: AI Skill Malware, 31Tbps DDoS, Notepad++ Hack, LLM Backdoors and More – The Hacker News
Cyber threats are no longer coming from just malware or exploits. They’re showing up inside the tools, platforms, and ecosystems organizations use every day. As companies connect AI, cloud apps, developer tools, and communication systems, attackers are following those same paths. A clear pattern this week: attackers are abusing trust. Trusted updates, trusted marketplaces, trusted … Read More “⚡ Weekly Recap: AI Skill Malware, 31Tbps DDoS, Notepad++ Hack, LLM Backdoors and More – The Hacker News” »
Why do SOC teams keep burning out and missing SLAs even after spending big on security tools? Routine triage piles up, senior specialists get dragged into basic validation, and MTTR climbs, while stealthy threats still find room to slip through. Top CISOs have realized the solution isn’t hiring more people or stacking yet another tool … Read More “How Top CISOs Solve Burnout and Speed up MTTR without Extra Hiring – The Hacker News” »
China-Linked DKnife Spyware Hijacking Internet Routers Since 2019 – Hackread – Cybersecurity News, Data Breaches, AI and More

Cisco Talos uncovers DKnife, a China-nexus framework targeting routers and edge devices. Learn how seven stealthy implants hijack data and deliver malware via AitM attacks. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Bloody Wolf Targets Uzbekistan, Russia Using NetSupport RAT in Spear-Phishing Campaign – The Hacker News

The threat actor known as Bloody Wolf has been linked to a campaign targeting Uzbekistan and Russia to infect systems with a remote access trojan known as NetSupport RAT. Cybersecurity vendor Kaspersky is tracking the activity under the moniker Stan Ghouls. The threat actor is known to be active since at least 2023, orchestrating spear-phishing … Read More “Bloody Wolf Targets Uzbekistan, Russia Using NetSupport RAT in Spear-Phishing Campaign – The Hacker News” »
The Great Wall of China was built to slow northern raiders and prevent steppe armies from riding straight into the empire’s heart. Yet in 1644, its most impregnable fortress fell without a siege. At Shanhai Pass, where the wall meets the Bohai Sea, General Wu Sangui commanded the eastern gate. Behind him: a rebel army … Read More “AI security’s ‘Great Wall’ problem – CyberScoop” »
Revolut claims social media sites make £3.8bn annually from scam ads targeting European users – Read More –
The services of Florida-based payments platform BridgePay are offline due to a ransomware attack – Read More –
Cybersecurity researchers have called attention to a “massive campaign” that has systematically targeted cloud native environments to set up malicious infrastructure for follow-on exploitation. The activity, observed around December 25, 2025, and described as “worm-driven,” leveraged exposed Docker APIs, Kubernetes clusters, Ray dashboards, and Redis servers, along with the recently disclosed – Read More – … Read More “TeamPCP Worm Exploits Cloud Infrastructure to Build Criminal Infrastructure – The Hacker News” »
SecurityScorecard has identified over 40,000 OpenClaw deployments exposed to potential attack – Read More –
CISA has issued a new directive requiring federal agencies to decommission all end of support edge devices within 12 months to reduce ongoing exploitation risks – Read More –
BeyondTrust has released updates to address a critical security flaw impacting Remote Support (RS) and Privileged Remote Access (PRA) products that, if successfully exploited, could result in remote code execution. “BeyondTrust Remote Support (RS) and certain older versions of Privileged Remote Access (PRA) contain a critical pre-authentication remote code execution vulnerability,” the company – Read … Read More “BeyondTrust Fixes Critical Pre-Auth RCE Vulnerability in Remote Support and PRA – The Hacker News” »
8 Top MDR Providers for Mid-Market Companies – Hackread – Cybersecurity News, Data Breaches, AI and More

Top 8 MDR providers for mid-market firms needing expert detection, faster response, and reduced noise without building full in-house SOCs. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
UK Construction Firm Hit by Prometei Botnet Hiding in Windows Server – Hackread – Cybersecurity News, Data Breaches, AI and More

Cybersecurity firm eSentire’s TRU break down the Russian Prometei botnet attack on a UK firm, detailing its TOR usage, password theft and decoy tactics. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
OpenClaw (formerly Moltbot and Clawdbot) has announced that it’s partnering with Google-owned VirusTotal to scan skills that are being uploaded to ClawHub, its skill marketplace, as part of broader efforts to bolster the security of the agentic ecosystem. “All skills published to ClawHub are now scanned using VirusTotal’s threat intelligence, including their new Code Insight … Read More “OpenClaw Integrates VirusTotal Scanning to Detect Malicious ClawHub Skills – The Hacker News” »
Posted by Asterisk Development Team via Fulldisclosure on Feb 07 The Asterisk Development Team would like to announce security release Certified Asterisk 20.7-cert9. The release artifacts are available for immediate download at https://github.com/asterisk/asterisk/releases/tag/certified-20.7-cert9 and https://downloads.asterisk.org/pub/telephony/certified-asterisk Repository: https://github.com/asterisk/asterisk Tag: certified-20.7-cert9 ## Change Log for Release asterisk-certified-20.7-cert9 ###… – Read More – Full Disclosure
Posted by Asterisk Development Team via Fulldisclosure on Feb 07 The Asterisk Development Team would like to announce security release Asterisk 20.18.2. The release artifacts are available for immediate download at https://github.com/asterisk/asterisk/releases/tag/20.18.2 and https://downloads.asterisk.org/pub/telephony/asterisk Repository: https://github.com/asterisk/asterisk Tag: 20.18.2 ## Change Log for Release asterisk-20.18.2 ### Links: – [Full ChangeLog](… – Read More – Full Disclosure
Posted by Asterisk Development Team via Fulldisclosure on Feb 07 The Asterisk Development Team would like to announce security release Asterisk 22.8.2. The release artifacts are available for immediate download at https://github.com/asterisk/asterisk/releases/tag/22.8.2 and https://downloads.asterisk.org/pub/telephony/asterisk Repository: https://github.com/asterisk/asterisk Tag: 22.8.2 ## Change Log for Release asterisk-22.8.2 ### Links: – [Full ChangeLog](… – Read More – Full Disclosure
Posted by Asterisk Development Team via Fulldisclosure on Feb 07 The Asterisk Development Team would like to announce security release Asterisk 21.12.1. The release artifacts are available for immediate download at https://github.com/asterisk/asterisk/releases/tag/21.12.1 and https://downloads.asterisk.org/pub/telephony/asterisk Repository: https://github.com/asterisk/asterisk Tag: 21.12.1 ## Change Log for Release asterisk-21.12.1 ### Links: – [Full ChangeLog](… – Read More – Full Disclosure
Posted by Asterisk Development Team via Fulldisclosure on Feb 07 The Asterisk Development Team would like to announce security release Asterisk 23.2.2. The release artifacts are available for immediate download at https://github.com/asterisk/asterisk/releases/tag/23.2.2 and https://downloads.asterisk.org/pub/telephony/asterisk Repository: https://github.com/asterisk/asterisk Tag: 23.2.2 ## Change Log for Release asterisk-23.2.2 ### Links: – [Full ChangeLog](… – Read More – Full Disclosure
Bithumb Mistakenly Sends 620,000 Bitcoin ($40B) to Customer Accounts – Hackread – Cybersecurity News, Data Breaches, AI and More

A system error at Bithumb sent 620,000 Bitcoin worth about $40B to hundreds of users during a promotion, briefly disrupting prices and drawing scrutiny. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Firefox Will Give Users an AI Kill Switch for Better Privacy – Hackread – Cybersecurity News, Data Breaches, AI and More

Not everyone wants AI in their browser. Firefox 148 is introducing easy toggles to disable chatbots and AI tab grouping. Discover how Mozilla is prioritising user choice and privacy in its latest 2026 update. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
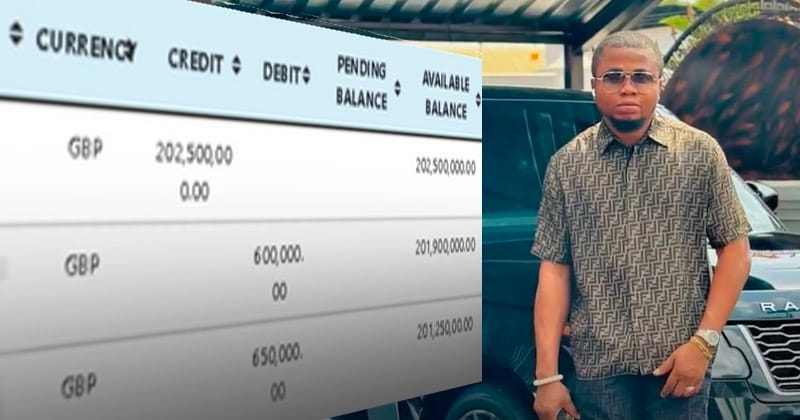
When a Romanian businesswoman fell for a fake Dubai Crown Prince in a $2.5 million romance scam, investigators tracked the fraudster to his Nigerian mansion – only to discover he was masquerading as a campaigning philanthropist. Read more in my article on the Hot for Security blog. – Read More – GRAHAM CLULEY
German Agencies Warn of Signal Phishing Targeting Politicians, Military, Journalists – The Hacker News

Germany’s Federal Office for the Protection of the Constitution (aka Bundesamt für Verfassungsschutz or BfV) and Federal Office for Information Security (BSI) have issued a joint advisory warning of a malicious cyber campaign undertaken by a likely state-sponsored threat actor that involves carrying out phishing attacks over the Signal messaging app. “The focus is on … Read More “German Agencies Warn of Signal Phishing Targeting Politicians, Military, Journalists – The Hacker News” »