Hudson Rock has warned OpenClaw users that infostealers are targeting their configuration files – Read More –
Author: Joe-W
Realmo Launches Location Intelligence Engine to Match Vacant Properties with Their Best Use – Hackread – Cybersecurity News, Data Breaches, AI and More

Boston, Massachusetts, 17th February 2026, CyberNewswire – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Apple on Monday released a new developer beta of iOS and iPadOS with support for end-to-end encryption (E2EE) in Rich Communications Services (RCS) messages. The feature is currently available for testing in iOS and iPadOS 26.4 Beta, and is expected to be shipped to customers in a future update for iOS, iPadOS, macOS, and watchOS. … Read More “Apple Tests End-to-End Encrypted RCS Messaging in iOS 26.4 Developer Beta – The Hacker News” »
Hackers Abuse ScreenConnect to Hijack PCs via Fake Social Security Emails – Hackread – Cybersecurity News, Data Breaches, AI and More

Forcepoint X-labs reveals how hackers use fake SSA emails and hijacked ScreenConnect tools to bypass Windows security to target UK, US, and Canadian organisations. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
The Digital Personal Data Protection (DPDP) Act is a transformative change in the data protection environment in India, the… The post How to build a DPDP-aligned incident and breach response playbook appeared first on JISA Softech Pvt Ltd. – Read More – JISA Softech Pvt Ltd
Posted by Apple Product Security via Fulldisclosure on Feb 16 APPLE-SA-02-11-2026-4 macOS Sequoia 15.7.4 macOS Sequoia 15.7.4 addresses the following issues. Information about the security content is also available at https://support.apple.com/126349. Apple maintains a Security Releases page at https://support.apple.com/100100 which lists recent software updates with security advisories. AppleMobileFileIntegrity Available for: macOS Sequoia Impact: An … Read More “APPLE-SA-02-11-2026-4 macOS Sequoia 15.7.4 – Full Disclosure” »
Posted by Apple Product Security via Fulldisclosure on Feb 16 APPLE-SA-02-11-2026-5 macOS Sonoma 14.8.4 macOS Sonoma 14.8.4 addresses the following issues. Information about the security content is also available at https://support.apple.com/126350. Apple maintains a Security Releases page at https://support.apple.com/100100 which lists recent software updates with security advisories. AppleMobileFileIntegrity Available for: macOS Sonoma Impact: An … Read More “APPLE-SA-02-11-2026-5 macOS Sonoma 14.8.4 – Full Disclosure” »
Posted by Apple Product Security via Fulldisclosure on Feb 16 APPLE-SA-02-11-2026-6 tvOS 26.3 tvOS 26.3 addresses the following issues. Information about the security content is also available at https://support.apple.com/126351. Apple maintains a Security Releases page at https://support.apple.com/100100 which lists recent software updates with security advisories. Bluetooth Available for: Apple TV HD and Apple TV … Read More “APPLE-SA-02-11-2026-6 tvOS 26.3 – Full Disclosure” »
Posted by Apple Product Security via Fulldisclosure on Feb 16 APPLE-SA-02-11-2026-7 watchOS 26.3 watchOS 26.3 addresses the following issues. Information about the security content is also available at https://support.apple.com/126352. Apple maintains a Security Releases page at https://support.apple.com/100100 which lists recent software updates with security advisories. Bluetooth Available for: Apple Watch Series 6 and later … Read More “APPLE-SA-02-11-2026-7 watchOS 26.3 – Full Disclosure” »
Posted by Apple Product Security via Fulldisclosure on Feb 16 APPLE-SA-02-11-2026-8 visionOS 26.3 visionOS 26.3 addresses the following issues. Information about the security content is also available at https://support.apple.com/126353. Apple maintains a Security Releases page at https://support.apple.com/100100 which lists recent software updates with security advisories. AppleMobileFileIntegrity Available for: Apple Vision Pro (all models) Impact: … Read More “APPLE-SA-02-11-2026-8 visionOS 26.3 – Full Disclosure” »
Posted by Apple Product Security via Fulldisclosure on Feb 16 APPLE-SA-02-11-2026-9 Safari 26.3 Safari 26.3 addresses the following issues. Information about the security content is also available at https://support.apple.com/126354. Apple maintains a Security Releases page at https://support.apple.com/100100 which lists recent software updates with security advisories. CFNetwork Available for: macOS Sonoma and macOS Sequoia Impact: … Read More “APPLE-SA-02-11-2026-9 Safari 26.3 – Full Disclosure” »
Posted by Christian Zäske via Fulldisclosure on Feb 16 Advisory ID: SYSS-2025-011 Product: MR9600, MX4200 (and potentially others) Manufacturer: Linksys Affected Version(s): 1.0.4.205530 for MR9600, 1.0.13.210200 for MX4200 (and potentially others) Tested … Read More “[SYSS-2025-011] Linksys MX9600/MX4200 – OS Command Injection – Full Disclosure” »
[SYSS-2025-014] Linksys MX4200 – Improper Verification of Source of a Communication Channel – Full Disclosure
![[SYSS-2025-014] Linksys MX4200 – Improper Verification of Source of a Communication Channel – Full Disclosure](https://attackfeed.com/wp-content/uploads/2026/02/fulldisclosure-img-2ngvbO.webp)
Posted by Christian Zäske via Fulldisclosure on Feb 16 Advisory ID: SYSS-2025-014 Product: MX4200 (and potentially others) Manufacturer: Linksys Affected Version(s): 1.0.13.210200 (and potentially others) Tested Version(s): 1.0.13.210200 MX4200 … Read More “[SYSS-2025-014] Linksys MX4200 – Improper Verification of Source of a Communication Channel – Full Disclosure” »
Firedancer Solana Validator – QUIC Transport Parameter UB and Consensus-Splitting Cast Bug – Full Disclosure

Posted by Agent Spooky’s Fun Parade via Fulldisclosure on Feb 16 1. SUMMARY Two independently confirmed vulnerabilities in Jump Crypto’s Firedancer Solana validator (https://github.com/firedancer-io/firedancer, commit 7cd3b6dce): A) Three undefined behavior / logic bugs in QUIC transport parameter processing, triggerable by a malicious QUIC server with zero authentication. Enables remote connection kill or hang. B) … Read More “Firedancer Solana Validator – QUIC Transport Parameter UB and Consensus-Splitting Cast Bug – Full Disclosure” »
🚨 Public Disclosure: Remote BitLocker Bypass via Intel AMT — SYSTEM Access Without Login – Full Disclosure

Posted by Darsh Naik on Feb 16 🔓 The Attack Path — No Login, SYSTEM Access 1. Boot into setup.exe (via USB, PXE, or OOBM like Intel vPro). 2. Click “Repair your computer” → Enter WinRE. 3. Press Shift + F10 → SYSTEM-level Command Prompt. 4. From there, attacker can: – Run `net user` … Read More “🚨 Public Disclosure: Remote BitLocker Bypass via Intel AMT — SYSTEM Access Without Login – Full Disclosure” »
Blind XXE in Electronic Invoice online tools (validator.invoice-portal.de, xrechnung.rib.de) – Full Disclosure

Posted by Hanno Böck on Feb 16 During tests of electronic invoicing tools, I discovered multiple XXE and Blind XXE vulnerabilities in online tools parsing electronic invoices in XML formats. While most of the affected tools have fixed these vulnerabilities, two online tools remain vulnerable to Blind XXE attacks, allowing exfiltration of files. Disclosure … Read More “Blind XXE in Electronic Invoice online tools (validator.invoice-portal.de, xrechnung.rib.de) – Full Disclosure” »
Posted by Apple Product Security via Fulldisclosure on Feb 16 APPLE-SA-02-11-2026-1 iOS 26.3 and iPadOS 26.3 iOS 26.3 and iPadOS 26.3 addresses the following issues. Information about the security content is also available at https://support.apple.com/126346. Apple maintains a Security Releases page at https://support.apple.com/100100 which lists recent software updates with security advisories. Accessibility Available for: … Read More “APPLE-SA-02-11-2026-1 iOS 26.3 and iPadOS 26.3 – Full Disclosure” »
Posted by Apple Product Security via Fulldisclosure on Feb 16 APPLE-SA-02-11-2026-2 iOS 18.7.5 and iPadOS 18.7.5 iOS 18.7.5 and iPadOS 18.7.5 addresses the following issues. Information about the security content is also available at https://support.apple.com/126347. Apple maintains a Security Releases page at https://support.apple.com/100100 which lists recent software updates with security advisories. Accessibility Available for: … Read More “APPLE-SA-02-11-2026-2 iOS 18.7.5 and iPadOS 18.7.5 – Full Disclosure” »
Posted by Apple Product Security via Fulldisclosure on Feb 16 APPLE-SA-02-11-2026-3 macOS Tahoe 26.3 macOS Tahoe 26.3 addresses the following issues. Information about the security content is also available at https://support.apple.com/126348. Apple maintains a Security Releases page at https://support.apple.com/100100 which lists recent software updates with security advisories. Admin Framework Available for: macOS Tahoe Impact: … Read More “APPLE-SA-02-11-2026-3 macOS Tahoe 26.3 – Full Disclosure” »
[Full Disclosure] CVE-2025-69690 & CVE-2025-69691 — Authenticated RCE in Netgate pfSense CE 2.7.2 and 2.8.0 – Full Disclosure
![[Full Disclosure] CVE-2025-69690 & CVE-2025-69691 — Authenticated RCE in Netgate pfSense CE 2.7.2 and 2.8.0 – Full Disclosure](https://attackfeed.com/wp-content/uploads/2026/02/fulldisclosure-img-zQCQhK.webp)
Posted by privexploits via Fulldisclosure on Feb 16 Advisory: Authenticated Remote Code Execution in pfSense CECVEs: CVE-2025-69690, CVE-2025-69691 Researcher: Nelson Adhepeau (privexploits () protonmail com) Date: February 2026 == RESPONSIBLE DISCLOSURE NOTICE == This advisory is published in accordance with responsible disclosure practices. The vendor was notified on December 2, 2025, acknowledged the reports, … Read More “[Full Disclosure] CVE-2025-69690 & CVE-2025-69691 — Authenticated RCE in Netgate pfSense CE 2.7.2 and 2.8.0 – Full Disclosure” »
SEC Consult SA-20260212-0 :: Multiple Vulnerabilities in various Solax Power Pocket WiFi models – Full Disclosure

Posted by SEC Consult Vulnerability Lab via Fulldisclosure on Feb 16 SEC Consult Vulnerability Lab Security Advisory < 20260212-0 > ======================================================================= title: Multiple Vulnerabilities product: Various Solax Power Pocket WiFi models vulnerable version: See section below fixed version: See section below … Read More “SEC Consult SA-20260212-0 :: Multiple Vulnerabilities in various Solax Power Pocket WiFi models – Full Disclosure” »
A new study has found that multiple cloud-based password managers, including Bitwarden, Dashlane, and LastPass, are susceptible to password recovery attacks under certain conditions. “The attacks range in severity from integrity violations to the complete compromise of all vaults in an organization,” researchers Matteo Scarlata, Giovanni Torrisi, Matilda Backendal, and Kenneth G. Paterson said. – … Read More “Study Uncovers 25 Password Recovery Attacks in Major Cloud Password Managers – The Hacker News” »
Cybersecurity researchers disclosed they have detected a case of an information stealer infection successfully exfiltrating a victim’s OpenClaw (formerly Clawdbot and Moltbot) configuration environment. “This finding marks a significant milestone in the evolution of infostealer behavior: the transition from stealing browser credentials to harvesting the ‘souls’ and identities of personal AI [ – Read More … Read More “Infostealer Steals OpenClaw AI Agent Configuration Files and Gateway Tokens – The Hacker News” »
NCSC’s Richard Horne has warned that cybercriminals do not care about business size and called for SMEs to act now to secure their organizations – Read More –
Security researchers have challenged end-to-end encryption claims from popular commercial password managers – Read More –
New phishing campaign dubbed Operation DoppelBrand targeted major financial firms like Wells Fargo – Read More –
OysterLoader malware evolves into 2026, refining C2 infrastructure, obfuscation & infection stages – Read More –
This week’s recap shows how small gaps are turning into big entry points. Not always through new exploits, often through tools, add-ons, cloud setups, or workflows that people already trust and rarely question. Another signal: attackers are mixing old and new methods. Legacy botnet tactics, modern cloud abuse, AI assistance, and supply-chain exposure are being … Read More “Weekly Recap: Outlook Add-Ins Hijack, 0-Day Patches, Wormable Botnet & AI Malware – The Hacker News” »
Presentation of the KTU Consortium Mission ‘A Safe and Inclusive Digital Society’ at the Innovation Agency event ‘Innovation Breakfast: How Mission-Oriented Science and Innovation Programmes Will Address Societal Challenges’. Technologies are evolving fast, reshaping economies, governance, and daily life. Yet, as innovation accelerates, so do digital risks. Technological change is no longer – Read More … Read More “Safe and Inclusive E‑Society: How Lithuania Is Bracing for AI‑Driven Cyber Fraud – The Hacker News” »
A high severity vulnerability in Google Chrome and allows remote attackers to execute code – Read More –
Google Ads and Claude AI Abused to Spread MacSync Malware via ClickFix – Hackread – Cybersecurity News, Data Breaches, AI and More
Cybersecurity experts at Moonlock Lab have discovered a new ClickFix attack. Hackers are using hijacked Google Ads and fake Claude AI guides to trick Mac users into installing the data-stealing MacSync malware. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Cybersecurity researchers have disclosed details of a new mobile spyware platform dubbed ZeroDayRAT that’s being advertised on Telegram as a way to grab sensitive data and facilitate real-time surveillance on Android and iOS devices. “The developer runs dedicated channels for sales, customer support, and regular updates, giving buyers a single point of access to a … Read More “New ZeroDayRAT Mobile Spyware Enables Real-Time Surveillance and Data Theft – The Hacker News” »
Chainalysis warns that online fraud is fuelling sophisticated human trafficking operations – Read More –
Dutch telco Odido has revealed a major data breach impacting over six million customers – Read More –
Google on Friday released security updates for its Chrome browser to address a security flaw that it said has been exploited in the wild. The high-severity vulnerability, tracked as CVE-2026-2441 (CVSS score: 8.8), has been described as a use-after-free bug in CSS. Security researcher Shaheen Fazim has been credited with discovering and reporting the shortcoming … Read More “New Chrome Zero-Day (CVE-2026-2441) Under Active Attack — Patch Released – The Hacker News” »
Microsoft has disclosed details of a new version of the ClickFix social engineering tactic in which the attackers trick unsuspecting users into running commands that carry out a Domain Name System (DNS) lookup to retrieve the next-stage payload. Specifically, the attack relies on using the “nslookup” (short for nameserver lookup) command to execute a custom … Read More “Microsoft Discloses DNS-Based ClickFix Attack Using Nslookup for Malware Staging – The Hacker News” »
287 Chrome Extensions Caught Harvesting Browsing Data from 37M Users – Hackread – Cybersecurity News, Data Breaches, AI and More
New investigation by Q Continuum reveals 287 Chrome extensions leaking the private browsing data of 37.4 million users to firms like Similarweb and Alibaba. Learn how these harmless tools turn your history into a product. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
What Interoperability in Healthcare Really Means for Security and Privacy – Hackread – Cybersecurity News, Data Breaches, AI and More
Healthcare interoperability improves care but expands attack surfaces, increasing data exposure, compliance risk, and security challenges across connected systems. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Google Links China, Iran, Russia, North Korea to Coordinated Defense Sector Cyber Operations – The Hacker News
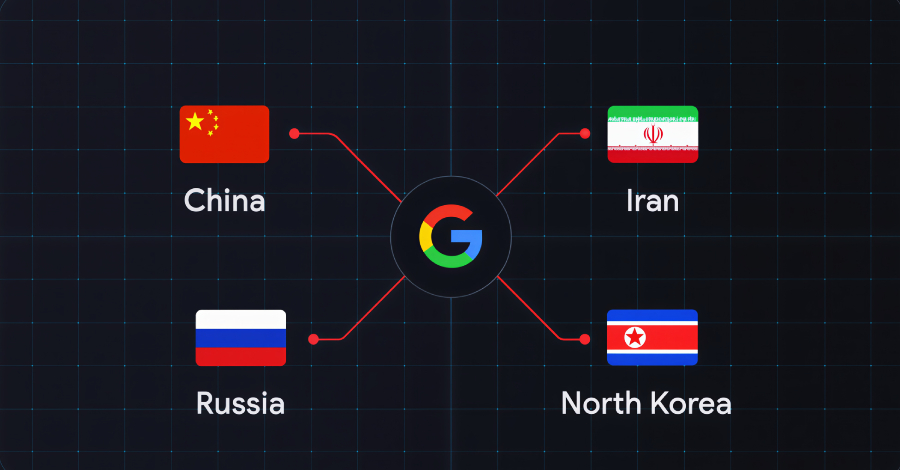
Several state-sponsored actors, hacktivist entities, and criminal groups from China, Iran, North Korea, and Russia have trained their sights on the defense industrial base (DIB) sector, according to findings from Google Threat Intelligence Group (GTIG). The tech giant’s threat intelligence division said the adversarial targeting of the sector is centered around four key themes: striking … Read More “Google Links China, Iran, Russia, North Korea to Coordinated Defense Sector Cyber Operations – The Hacker News” »
A previously undocumented threat actor has been attributed to attacks targeting Ukrainian organizations with malware known as CANFAIL. Google Threat Intelligence Group (GTIG) described the hack group as possibly affiliated with Russian intelligence services. The threat actor is assessed to have targeted defense, military, government, and energy organizations within the Ukrainian regional and – Read … Read More “Google Ties Suspected Russian Actor to CANFAIL Malware Attacks on Ukrainian Orgs – The Hacker News” »
A previously unknown threat actor tracked as UAT-9921 has been observed leveraging a new modular framework called VoidLink in its campaigns targeting the technology and financial services sectors, according to findings from Cisco Talos. “This threat actor seems to have been active since 2019, although they have not necessarily used VoidLink over the duration of … Read More “UAT-9921 Deploys VoidLink Malware to Target Technology and Financial Sectors – The Hacker News” »
G7 countries ranked cyber-attacks as the top risk, while BICS members placed cyber threats only as the eighth most pressing risk – Read More –
Static Design to Adaptive Control: How Artificial Intelligence Improves Modern Material Handling Equipment Systems – Hackread – Cybersecurity News, Data Breaches, AI and More
AI enables material handling systems to adapt to demand volatility through predictive design, dynamic control, and smarter maintenance without replacing core engineering. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
The $17 Billion Wake-Up Call: Securing Crypto in the Age of AI Scams – Hackread – Cybersecurity News, Data Breaches, AI and More

AI-driven crypto scams surge as cybercrime hits $17B, with deepfakes, fraud kits, and industrial social engineering reshaping digital asset threats and defenses. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Malicious Chrome Extensions Caught Stealing Business Data, Emails, and Browsing History – The Hacker News

Cybersecurity researchers have discovered a malicious Google Chrome extension that’s designed to steal data associated with Meta Business Suite and Facebook Business Manager. The extension, named CL Suite by @CLMasters (ID: jkphinfhmfkckkcnifhjiplhfoiefffl), is marketed as a way to scrape Meta Business Suite data, remove verification pop-ups, and generate two-factor authentication (2FA) codes. – Read More … Read More “Malicious Chrome Extensions Caught Stealing Business Data, Emails, and Browsing History – The Hacker News” »
Hundreds of thousands of users have downloaded malicious AI extensions masquerading as ChatGPT, Gemini, Grok and others, warn cybersecurity researchers at LayerX – Read More –
In December 2025, in response to the Sha1-Hulud incident, npm completed a major authentication overhaul intended to reduce supply-chain attacks. While the overhaul is a solid step forward, the changes don’t make npm projects immune from supply-chain attacks. npm is still susceptible to malware attacks – here’s what you need to know for a safer … Read More “npm’s Update to Harden Their Supply Chain, and Points to Consider – The Hacker News” »
As the Digital Personal Data Protection Act moves into active enforcement, many organisations across India are reviewing one of… The post How to Rewrite Your Privacy Notice for DPDP Compliance appeared first on JISA Softech Pvt Ltd. – Read More – JISA Softech Pvt Ltd
A coordinated cyberattack that targeted Poland’s energy infrastructure in late December 2025 has prompted cybersecurity agencies to issue urgent warnings to critical national infrastructure operators on both sides of the Atlantic. Read more in my article on the Fortra blog. – Read More – GRAHAM CLULEY
Researchers Observe In-the-Wild Exploitation of BeyondTrust CVSS 9.9 Vulnerability – The Hacker News
Threat actors have started to exploit a recently disclosed critical security flaw impacting BeyondTrust Remote Support (RS) and Privileged Remote Access (PRA) products, according to watchTowr. “Overnight we observed first in-the-wild exploitation of BeyondTrust across our global sensors,” Ryan Dewhurst, head of threat intelligence at watchTowr, said in a post on X. “Attackers are abusing … Read More “Researchers Observe In-the-Wild Exploitation of BeyondTrust CVSS 9.9 Vulnerability – The Hacker News” »








![[SYSS-2025-011] Linksys MX9600/MX4200 – OS Command Injection – Full Disclosure](https://attackfeed.com/wp-content/uploads/2026/02/fulldisclosure-img-uwBpAe.webp)