Threat actors likely associated with the Democratic People’s Republic of Korea (DPRK) have been observed using GitHub as command-and-control (C2) infrastructure in multi-stage attacks targeting organizations in South Korea. The attack chain, per Fortinet FortiGuard Labs, involves obfuscated Windows shortcut (LNK) files acting as the starting point to drop a decoy PDF – Read More – The Hacker News
Author: [email protected] (The Hacker News)
Microsoft has released a new report about the Storm-1175 group and its connection to Medusa ransomware – Read More –
Artificial Intelligence (AI) is as reliable as the data that it ingests. With enterprises broadening their use of AI… The post Building secure AI data pipelines with CryptoBind appeared first on JISA Softech Pvt Ltd. – Read More – JISA Softech Pvt Ltd
New academic research has identified multiple RowHammer attacks against high-performance graphics processing units (GPUs) that could be exploited to escalate privileges and, in some cases, even take full control of a host. The efforts have been codenamed GPUBreach, GDDRHammer, and GeForge. GPUBreach goes a step further than GPUHammer, demonstrating for the first time that – Read More – The … Read More “New GPUBreach Attack Enables Full CPU Privilege Escalation via GDDR6 Bit-Flips – The Hacker News” »
Fortinet has updated its FortiClient EMS product after zero-day attacks surfaced – Read More –
Life imprisonment for Cambodian scam compound operators – but will it make a difference? – GRAHAM CLULEY

Cambodia has taken a dramatic step in its fight against scam compounds that have imprisoned innocent people, and forced them to work as virtual slaves defrauding victims via the internet around the world with romance scams and dodgy investment schemes. Read more in my article on the Hot for Security blog. – Read More – … Read More “Life imprisonment for Cambodian scam compound operators – but will it make a difference? – GRAHAM CLULEY” »
A China-based threat actor known for deploying Medusa ransomware has been linked to the weaponization of a combination of zero-day and N-day vulnerabilities to orchestrate “high-velocity” attacks and break into susceptible internet-facing systems. “The threat actor’s high operational tempo and proficiency in identifying exposed perimeter assets have proven successful, with recent – Read More – The Hacker … Read More “China-Linked Storm-1175 Exploits Zero-Days to Rapidly Deploy Medusa Ransomware – The Hacker News” »
Flowise AI Agent Builder Under Active CVSS 10.0 RCE Exploitation; 12,000+ Instances Exposed – The Hacker News

Threat actors are exploiting a maximum-severity security flaw in Flowise, an open-source artificial intelligence (AI) platform, according to new findings from VulnCheck. The vulnerability in question is CVE-2025-59528 (CVSS score: 10.0), a code injection vulnerability that could result in remote code execution. “The CustomMCP node allows users to input configuration settings for connecting – Read More … Read More “Flowise AI Agent Builder Under Active CVSS 10.0 RCE Exploitation; 12,000+ Instances Exposed – The Hacker News” »
Fortinet customers confront actively exploited zero-day, with a full patch still pending – CyberScoop

Fortinet released an emergency software update over the weekend to address an actively exploited vulnerability in FortiClient EMS, an endpoint management tool for customer devices. The zero-day vulnerability — CVE-2026-35616 — has a CVSS rating of 9.8 and was added to the Cybersecurity and Infrastructure Security Agency’s known exploited vulnerability catalog Monday. Fortinet said in … Read More “Fortinet customers confront actively exploited zero-day, with a full patch still pending – CyberScoop” »
Iran-Linked Password-Spraying Campaign Targets 300+ Israeli Microsoft 365 Organizations – The Hacker News

An Iran-nexus threat actor is suspected to be behind a password-spraying campaign targeting Microsoft 365 environments in Israel and the U.A.E. amid ongoing conflict in the Middle East. The activity, assessed to be ongoing, was carried out in three distinct attack waves that took place on March 3, March 13, and March 23, 2026, per Check Point. “The campaign is … Read More “Iran-Linked Password-Spraying Campaign Targets 300+ Israeli Microsoft 365 Organizations – The Hacker News” »
A federal judge has sentenced the maker of stalkerware pcTattleTale, which went out of business after a data breach, to supervised release and a $5,000 fine. Bryan Fleming pleaded guilty in January to a charge of intentionally manufacturing, possessing or selling a device with the knowledge that it would be primarily used for surreptitious interception … Read More “pcTattleTale stalkerware maker sentence includes fine, supervised release – CyberScoop” »
Missile Alert Phishing Exploits Iran-US-Israel Conflict for Microsoft Logins – Hackread – Cybersecurity News, Data Breaches, AI and More

New Phishing scam uses fake missile alerts and the ongoing conflict involving Iran to target users with QR codes and fake government emails to steal Microsoft passwords. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
⚡ Weekly Recap: Axios Hack, Chrome 0-Day, Fortinet Exploits, Paragon Spyware and More – The Hacker News

This week had real hits. The key software got tampered with. Active bugs showed up in the tools people use every day. Some attacks didn’t even need much effort because the path was already there. One weak spot now spreads wider than before. What starts small can reach a lot of systems fast. New bugs, faster use, less time to react. That’s this … Read More “⚡ Weekly Recap: Axios Hack, Chrome 0-Day, Fortinet Exploits, Paragon Spyware and More – The Hacker News” »
Your attack surface no longer lives on one operating system, and neither do the campaigns targeting it. In enterprise environments, attackers move across Windows endpoints, executive MacBooks, Linux infrastructure, and mobile devices, taking advantage of the fact that many SOC workflows are still fragmented by platform. For security leaders, this creates a – Read More – The Hacker News
Why Security Researchers and Red Teams Are Turning to Workflow Automation – Hackread – Cybersecurity News, Data Breaches, AI and More
Security researchers and red teams adopt workflow automation to cut alert fatigue, enrich data, and scale operations across SOC, intel and recon tasks. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Cloudflare Targets WordPress With New AI-Powered EmDash CMS – Hackread – Cybersecurity News, Data Breaches, AI and More

Cloudflare launches EmDash CMS, an AI-powered platform built to fix WordPress security flaws with sandboxed plugins, serverless scaling, and passkey auth. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
North Korean Hackers Pose as Trading Firm to Steal $285M from Drift – Hackread – Cybersecurity News, Data Breaches, AI and More

North Korean hackers (UNC4736) posed as a trading firm for six months to infiltrate Drift Protocol, using social engineering tactics to steal $285M without suspicion. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
The most active piece of enterprise infrastructure in the company is the developer workstation. That laptop is where credentials are created, tested, cached, copied, and reused across services, bots, build tools, and now local AI agents. In March 2026, the TeamPCP threat actor proved just how valuable developer machines are. Their supply chain attack on – Read More – The Hacker News
Threat actors associated with Qilin and Warlock ransomware operations have been observed using the bring your own vulnerable driver (BYOVD) technique to silence security tools running on compromised hosts, according to findings from Cisco Talos and Trend Micro. Qilin attacks analyzed by Talos have been found to deploy a malicious DLL named “msimg32.dll,” – Read More – The Hacker News
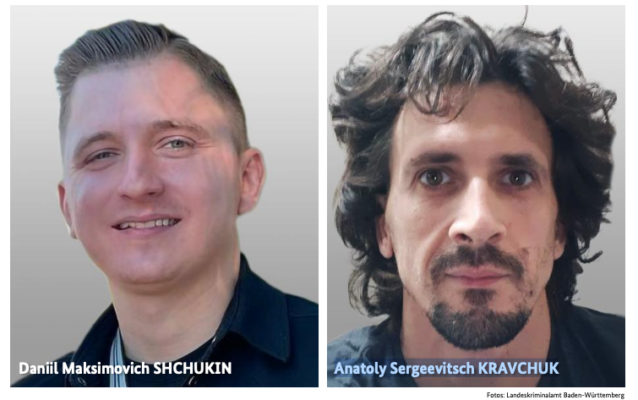
Germany’s Federal Criminal Police Office (aka BKA or the Bundeskriminalamt) has unmasked the real identity of the main threat actors associated with the now-defunct REvil (aka Sodinokibi) ransomware-as-a-service (RaaS) operation. The threat actor, who went by the alias UNKN, functioned as a representative of the group, advertising the ransomware in June 2019 on the XSS … Read More “BKA Identifies REvil Leaders Behind 130 German Ransomware Attacks – The Hacker News” »
An elusive hacker who went by the handle “UNKN” and ran the early Russian ransomware groups GandCrab and REvil now has a name and a face. Authorities in Germany say 31-year-old Russian Daniil Maksimovich Shchukin headed both cybercrime gangs and helped carry out at least 130 acts of computer sabotage and extortion against victims across … Read More “Germany Doxes “UNKN,” Head of RU Ransomware Gangs REvil, GandCrab – Krebs on Security” »
Drift has revealed that the April 1, 2026, attack that led to the theft of $285 million was the culmination of a months-long targeted and meticulously planned social engineering operation undertaken by the Democratic People’s Republic of Korea (DPRK) that began in the fall of 2025. The Solana-based decentralized exchange described it as “an attack six months in the – … Read More “$285 Million Drift Hack Traced to Six-Month DPRK Social Engineering Operation – The Hacker News” »
Microsoft Details Cookie-Controlled PHP Web Shells Persisting via Cron on Linux Servers – The Hacker News
Threat actors are increasingly using HTTP cookies as a control channel for PHP-based web shells on Linux servers and to achieve remote code execution, according to findings from the Microsoft Defender Security Research Team. “Instead of exposing command execution through URL parameters or request bodies, these web shells rely on threat actor-supplied cookie values to gate execution, … Read More “Microsoft Details Cookie-Controlled PHP Web Shells Persisting via Cron on Linux Servers – The Hacker News” »
BrowserGate: LinkedIn Tracks 6,000+ Browser Extensions on Users’ PCs – Hackread – Cybersecurity News, Data Breaches, AI and More
LinkedIn is accused in the BrowserGate report of tracking 6,000+ browser extensions on users’ PCs, raising concerns over privacy and data collection practices. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Fortinet has released out-of-band patches for a critical security flaw impacting FortiClient EMS that it said has been exploited in the wild. The vulnerability, tracked as CVE-2026-35616 (CVSS score: 9.1), has been described as a pre-authentication API access bypass leading to privilege escalation. “An improper access control vulnerability [CWE-284] in FortiClient EMS may allow an – Read More … Read More “Fortinet Patches Actively Exploited CVE-2026-35616 in FortiClient EMS – The Hacker News” »
36 Malicious npm Packages Exploited Redis, PostgreSQL to Deploy Persistent Implants – The Hacker News
Cybersecurity researchers have discovered 36 malicious packages in the npm registry that are disguised as Strapi CMS plugins but come with different payloads to facilitate Redis and PostgreSQL exploitation, deploy reverse shells, harvest credentials, and drop a persistent implant. “Every package contains three files (package.json, index.js, postinstall.js), has no description, repository, – Read More – The … Read More “36 Malicious npm Packages Exploited Redis, PostgreSQL to Deploy Persistent Implants – The Hacker News” »
UNC1069 Targets Node.js Maintainers via Fake LinkedIn, Slack Profiles – Hackread – Cybersecurity News, Data Breaches, AI and More

North Korean group UNC1069 targets Node.js maintainers using fake LinkedIn and Slack profiles to spread malware and compromise open source packages. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
A Vulnerability has been discovered in Fortinet FortiClientEMS that could allow for arbitrary code execution. FortiClientEMS is a centralized management platform for deploying, configuring, monitoring, and enforcing security policies across numerous endpoints (computers) running the FortiClient agent. Successful exploitation of this vulnerability could allow for arbitrary code execution in the context of the affected service account. Depending … Read More “A Vulnerability in Fortinet FortiClientEMS Could Allow for Arbitrary Code Execution – Cyber Security Advisories – MS-ISAC” »
Fake ChatGPT Ad Blocker Chrome Extension Caught Spying on Users – Hackread – Cybersecurity News, Data Breaches, AI and More
A fake Chrome browser extension called ‘ChatGPT Ad Blocker’ was harvesting conversations of ChatGPT users in the name of offering an ad-free experience. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
North Korean Hackers Abuse GitHub to Spy on South Korean Firms – Hackread – Cybersecurity News, Data Breaches, AI and More

Researchers from FortiGuard Labs have uncovered a high-severity spying campaign targeting South Korean companies. Discover how North Korean… – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
China-Linked TA416 Targets European Governments with PlugX and OAuth-Based Phishing – The Hacker News

A China-aligned threat actor has set its sights on European government and diplomatic organizations since mid-2025, following a two-year period of minimal targeting in the region. The campaign has been attributed to TA416, a cluster of activity that overlaps with DarkPeony, RedDelta, Red Lich, SmugX, UNC6384, and Vertigo Panda. “This TA416 activity included multiple – Read More – The Hacker … Read More “China-Linked TA416 Targets European Governments with PlugX and OAuth-Based Phishing – The Hacker News” »
AI Future: The Leading International AI and Web3 Forum to Take Place in April – Hackread – Cybersecurity News, Data Breaches, AI and More

Moscow, Russia, 3rd April 2026, CyberNewswire – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
AI Firm Mercor Confirms Breach as Hackers Claim 4TB of Stolen Data – Hackread – Cybersecurity News, Data Breaches, AI and More

AI firm Mercor confirms a breach linked to a LiteLLM supply chain attack, as hackers claim to have stolen 4TB of sensitive data and internal systems. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Wyden warns Social Security chief: Trump’s voter database is ‘blatant voter suppression’ – CyberScoop

Sen. Ron Wyden, D-Ore., warned Social Security Administration chief Frank Bisignano that any follow-through on President Donald Trump’s executive order creating a new database of U.S. voters using agency data would be viewed by Democrats as a conscious choice on the part of SSA officials to participate in “blatant voter suppression.” “Facilitating Donald Trump’s directive … Read More “Wyden warns Social Security chief: Trump’s voter database is ‘blatant voter suppression’ – CyberScoop” »
President Donald Trump’s fiscal 2027 budget would slash the Cybersecurity and Infrastructure Security Agency’s total by $707 million, according to a summary released Friday, which would deeply chop down an agency that already took a big hit in Trump’s first year. Another budget document suggests a smaller — but still substantial — hit of $361 … Read More “Trump budget proposal would cut hundreds of millions more from CISA – CyberScoop” »
Wyden warns Social Security chief: Trump’s voter database is ‘blatant voter suppression’ – CyberScoop

Sen. Ron Wyden, D-Ore., warned Social Security Administration chief Frank Bisignano that any follow-through on President Donald Trump’s executive order creating a new database of U.S. voters using agency data would be viewed by Democrats as a conscious choice on the part of SSA officials to participate in “blatant voter suppression.” “Facilitating Donald Trump’s directive … Read More “Wyden warns Social Security chief: Trump’s voter database is ‘blatant voter suppression’ – CyberScoop” »
A large-scale credential theft campaign targeting senior executives has been linked to a previously unknown automated phishing platform called Venom – Read More –
The next major breach hitting your clients probably won’t come from inside their walls. It’ll come through a vendor they trust, a SaaS tool their finance team signed up for, or a subcontractor nobody in IT knows about. That’s the new attack surface, and most organizations are underprepared for it. Cynomi’s new guide, Securing the Modern Perimeter: The Rise of … Read More “Why Third-Party Risk Is the Biggest Gap in Your Clients’ Security Posture – The Hacker News” »
The maintainer of the Axios npm package has confirmed that the supply chain compromise was the result of a highly-targeted social engineering campaign orchestrated by North Korean threat actors tracked as UNC1069. Maintainer Jason Saayman said the attackers tailored their social engineering efforts “specifically to me” by first approaching him under the guise of the founder of … Read More “UNC1069 Social Engineering of Axios Maintainer Led to npm Supply Chain Attack – The Hacker News” »
A Nigerian fraudster spent years posing as a woman online, romancing unsuspecting American men out of their savings – until he accidentally tried the same trick on a fellow scammer, who told him to “learn how to do a clean job.” The recovered chat logs helped put him behind bars for 15 years. Read more … Read More “Nigerian romance scammer jailed after being caught out by fellow fraudster – GRAHAM CLULEY” »
Drift Loses $285 Million in Durable Nonce Social Engineering Attack Linked to DPRK – The Hacker News

Solana-based decentralized exchange Drift has confirmed that attackers drained about $285 million from the platform during a security incident that took place on April 1, 2026. “Earlier today, a malicious actor gained unauthorized access to Drift Protocol through a novel attack involving durable nonces, resulting in a rapid takeover of Drift’s Security Council administrative powers,” the& … Read More “Drift Loses $285 Million in Durable Nonce Social Engineering Attack Linked to DPRK – The Hacker News” »
New SparkCat Variant in iOS, Android Apps Steals Crypto Wallet Recovery Phrase Images – The Hacker News

Cybersecurity researchers have discovered a new version of the SparkCat malware on the Apple App Store and Google Play Store, more than a year after the trojan was discovered targeting both the mobile operating systems. The malware has been found to conceal itself within seemingly benign apps, such as enterprise messengers and food delivery services, while – Read More – The Hacker … Read More “New SparkCat Variant in iOS, Android Apps Steals Crypto Wallet Recovery Phrase Images – The Hacker News” »
Posted by cyber security on Apr 02 A vulnerability was identified in OWASP CRS where whitespace padding in filenames can bypass file upload extension checks, allowing uploads of dangerous files such as .php, .phar, .jsp, and .jspx. This issue has been assigned CVE‑2026‑33691. Impact: Attackers may evade CRS protections and upload web shells disguised … Read More “[CVE-2026-33691] OWASP CRS whitespace padding bypass vulnerability – Full Disclosure” »
Posted by Egidio Romano on Apr 02 ————————————————————————— MetInfo CMS <= 8.1 (weixinreply.class.php) PHP Code Injection Vulnerability ————————————————————————— [-] Software Link: https://www.metinfo.cn [-] Affected Versions: Versions 7.9, 8.0, and 8.1. [-] Vulnerability Description: The vulnerable code is located into the… – Read More – Full Disclosure
Posted by Joseph Goydish II via Fulldisclosure on Apr 02 SUMMARY Apple’s Oblivious HTTP relay for Live Caller ID Lookup (iOS 18+) routes traffic through 14 third-party endpoints across six countries. These include an anonymous Delaware LLC sharing data with OpenAI, a Russian endpoint (Yandex), and a Swiss GmbH whose privacy policy names “The … Read More “Apple OHTTP Relay: 14 Third-Party Endpoints, 6 Countries, Zero User Visibility – Full Disclosure” »
SEC Consult SA-20260326-0 :: Local Privilege Escalation in Vienna Assistant (MacOS) – Vienna Symphonic Library – Full Disclosure

Posted by SEC Consult Vulnerability Lab via Fulldisclosure on Apr 02 SEC Consult Vulnerability Lab Security Advisory < 20260326-0 > ======================================================================= title: Local Privilege Escalation product: Vienna Assistant (MacOS) – Vienna Symphonic Library vulnerable version: 1.2.542 fixed version: – CVE number: CVE-2026-24068 impact: high homepage:https://www.vsl.co.at/ … Read More “SEC Consult SA-20260326-0 :: Local Privilege Escalation in Vienna Assistant (MacOS) – Vienna Symphonic Library – Full Disclosure” »
Posted by SEC Consult Vulnerability Lab via Fulldisclosure on Apr 02 SEC Consult Vulnerability Lab Security Advisory < 20260401-0 > ======================================================================= title: Broken Access Control product: Open WebUI vulnerable version: <v0.8.11 fixed version: v0.8.11 CVE number: CVE-2026-34222 impact: high … Read More “SEC Consult SA-20260401-0 :: Broken Access Control in Open WebUI – Full Disclosure” »
Multiple vulnerabilities have been discovered in Cisco products, the most severe of which could allow for arbitrary code execution. Cisco Smart Software Manager On‑Prem is a centralized Cisco tool used by organizations to manage software licenses, entitlements, and compliance for Cisco products within their own network environment. Cisco Integrated Management Controller (IMC) is embedded server … Read More “Multiple Vulnerabilities in Cisco Products Could Allow for Arbitrary Code Execution – Cyber Security Advisories – MS-ISAC” »
Multiple vulnerabilities have been discovered in Progress ShareFile, which when chained together, could allow for remote code execution. Progress ShareFile is a secure, cloud-based content collaboration and file-sharing platform. It enables businesses to securely exchange documents, manage client workflows, and obtain electronic signatures, with a focus on compliance for industries like finance and healthcare. Successful … Read More “Multiple Vulnerabilities in Progress ShareFile Could Allow for Remote Code Execution – Cyber Security Advisories – MS-ISAC” »
A large-scale credential harvesting operation has been observed exploiting the React2Shell vulnerability as an initial infection vector to steal database credentials, SSH private keys, Amazon Web Services (AWS) secrets, shell command history, Stripe API keys, and GitHub tokens at scale. Cisco Talos has attributed the operation to a threat cluster it tracks as – Read More – The Hacker News













![[CVE-2026-33691] OWASP CRS whitespace padding bypass vulnerability – Full Disclosure](https://attackfeed.com/wp-content/uploads/2026/04/fulldisclosure-img-d1d1in.png)
![[KIS-2026-06] MetInfo CMS](https://attackfeed.com/wp-content/uploads/2026/04/fulldisclosure-img-TM4Ea2.png)


