North Korean Hackers Publish 26 npm Packages Hiding Pastebin C2 for Cross-Platform RAT – The Hacker News

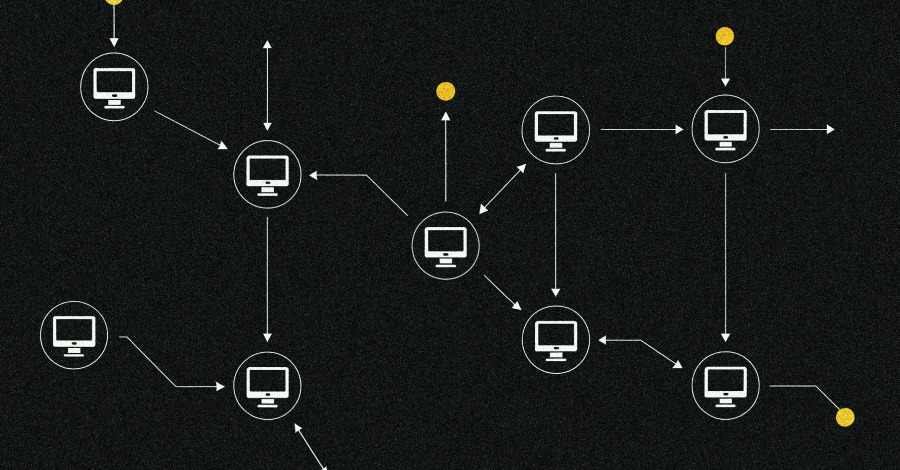
Cybersecurity researchers have disclosed a new iteration of the ongoing Contagious Interview campaign, where the North Korean threat actors have published a set of 26 malicious packages to the npm registry. The packages masquerade as developer tools, but contain functionality to extract the actual command-and-control (C2) by using seemingly harmless Pastebin content as a dead … Read More “North Korean Hackers Publish 26 npm Packages Hiding Pastebin C2 for Cross-Platform RAT – The Hacker News” »