The Department of Health and Human Services unveiled a tool Thursday to help health care facilities assess their cybersecurity risks, elevating the emphasis on those threats to the kind produced by weather conditions and other dangers. The assistance from HHS’s Administration for Strategic Preparedness and Response (ASPR) comes in the form of an update to … Read More “HHS updates a free risk tool to help hospitals size up their cybersecurity exposure – CyberScoop” »
Author: Tim Starks
PleaseFix Flaw Lets Hackers Access 1Password Vault via Comet AI Browser – Hackread – Cybersecurity News, Data Breaches, AI and More
Researchers at Zenity Labs uncover PleaseFix flaws in Perplexity’s Comet browser. See how zero-click calendar invites allow AI agents to steal 1Password credentials and personal files. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Interview with Tom Howe of Hydrolix: AI Bots, the Friends, Foes, and Frenemies of Online Shopping – Hackread – Cybersecurity News, Data Breaches, AI and More

Hydrolix expert Tom Howe explains how AI bots impact ecommerce, how to spot good vs malicious bots, and why blocking them can hurt sales. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Russian national Evgenii Ptitsyn pleaded guilty to running the Phobos ransomware outfit that extorted more than $39 million from more than 1,000 victims globally, the Justice Department said Wednesday. Ptitsyn assumed a leadership role in the Phobos ransomware group in January 2022, yet his criminal activities began by April 2019, according to court records. He … Read More “Phobos ransomware leader pleads guilty, faces up to 20 years in prison – CyberScoop” »
Cisco has disclosed that two more vulnerabilities affecting Catalyst SD-WAN Manager (formerly SD-WAN vManage) have come under active exploitation in the wild. The vulnerabilities in question are listed below – CVE-2026-20122 (CVSS score: 7.1) – An arbitrary file overwrite vulnerability that could allow an authenticated, remote attacker to overwrite arbitrary files on the local file … Read More “Cisco Confirms Active Exploitation of Two Catalyst SD-WAN Manager Vulnerabilities – The Hacker News” »
Cisco has disclosed that two more vulnerabilities affecting Catalyst SD-WAN Manager (formerly SD-WAN vManage) have come under active exploitation in the wild. The vulnerabilities in question are listed below – CVE-2026-20122 (CVSS score: 7.1) – An arbitrary file overwrite vulnerability that could allow an authenticated, remote attacker to overwrite arbitrary files on the local file … Read More “Cisco Confirms Active Exploitation of Two Catalyst SD-WAN Manager Vulnerabilities – The Hacker News” »
Malicious insiders are using misusing AI for nefarious gain, while employees cutting corners also creates risk, warns Mimecast – Read More –
Authorities Shut Down Tycoon 2FA Phishing Platform Used to Bypass MFA – Hackread – Cybersecurity News, Data Breaches, AI and More

Europol and partners dismantle Tycoon 2FA phishing service used to bypass MFA, disrupting a global phishing-as-a-service operation targeting organisations. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
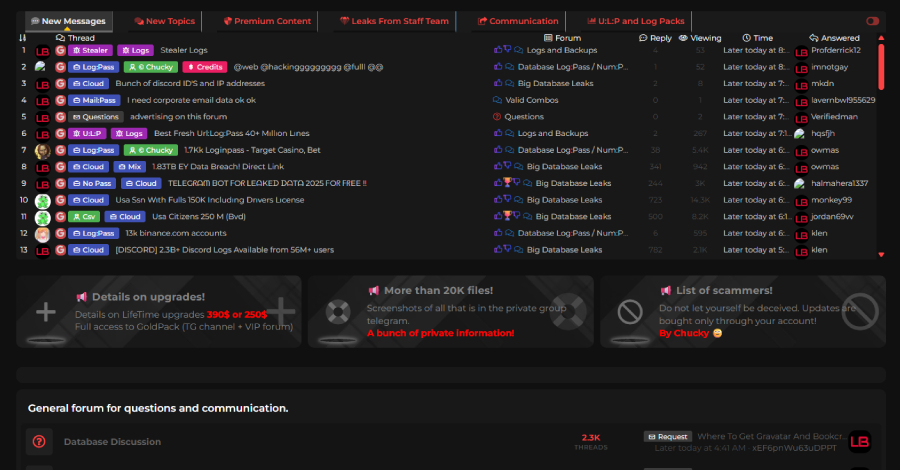
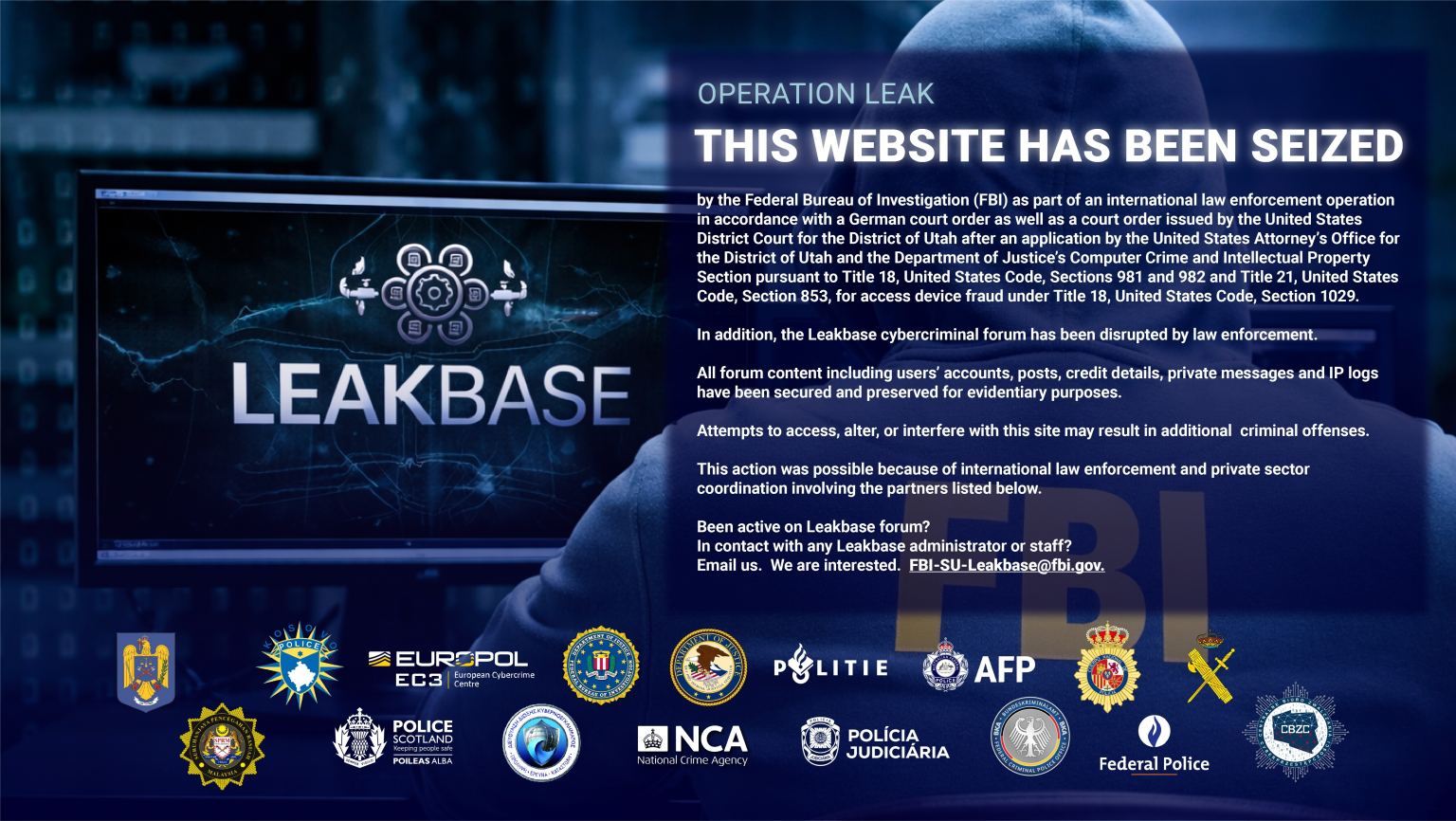
LeakBase Cybercrime and Hacker Forum Seized – Hackread – Cybersecurity News, Data Breaches, AI and More
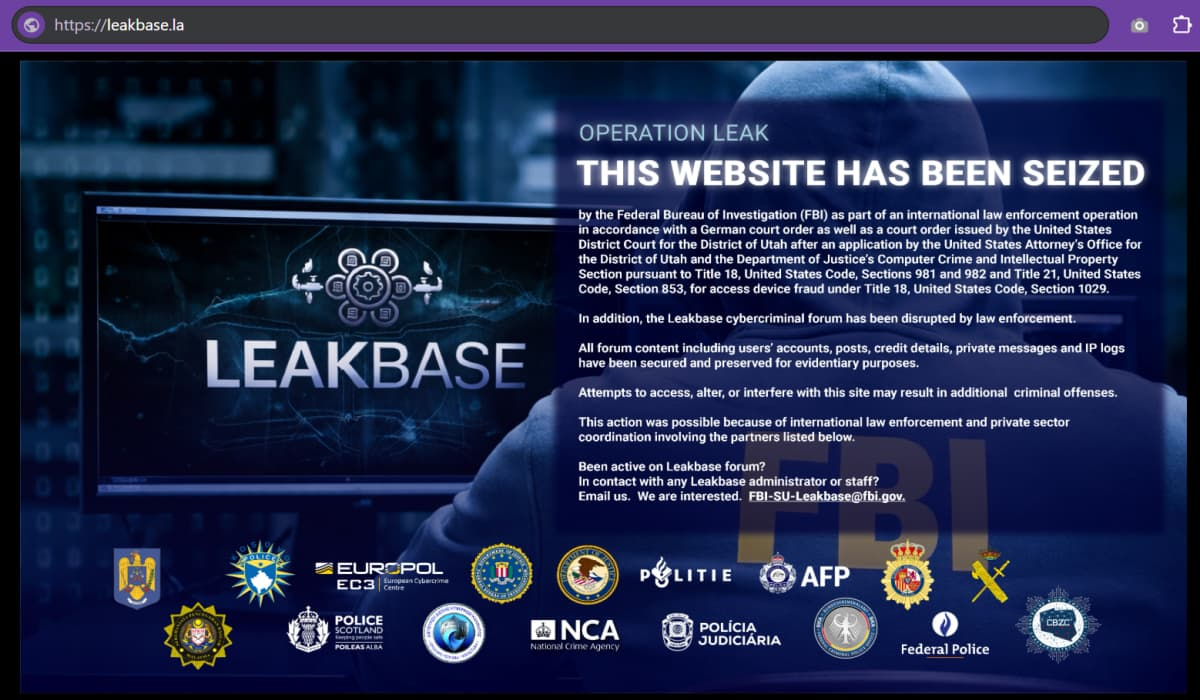
Europol seizes LeakBase cybercrime and hacker forum used to trade stolen data, disrupting a global platform with over 140,000 members. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Cisco released information on a pair of max-severity vulnerabilities in its firewall management software Wednesday that unauthenticated, remote attackers could exploit to obtain the highest level of access to the underlying operating system or on affected devices. The vulnerabilities — CVE-2026-20079 and CVE-2026-20131 — affect the web-based interface of Cisco Secure Firewall Management Center (FMC) … Read More “Cisco reveals 2 max-severity defects in firewall management software – CyberScoop” »
Preparing for the Quantum Era: Post-Quantum Cryptography Webinar for Security Leaders – The Hacker News
Most organizations assume encrypted data is safe. But many attackers are already preparing for a future where today’s encryption can be broken. Instead of trying to decrypt information now, they are collecting encrypted data and storing it so it can be decrypted later using quantum computers. This tactic—known as “harvest now, decrypt later”—means sensitive data … Read More “Preparing for the Quantum Era: Post-Quantum Cryptography Webinar for Security Leaders – The Hacker News” »
ThreatsDay Bulletin: DDR5 Bot Scalping, Samsung TV Tracking, Reddit Privacy Fine & More – The Hacker News
Some weeks in cybersecurity feel routine. This one doesn’t. Several new developments surfaced over the past few days, showing how quickly the threat landscape keeps shifting. Researchers uncovered fresh activity, security teams shared new findings, and a few unexpected moves from major tech companies also drew attention. Together, these updates offer a useful snapshot of … Read More “ThreatsDay Bulletin: DDR5 Bot Scalping, Samsung TV Tracking, Reddit Privacy Fine & More – The Hacker News” »
Critical flaw “ContextCrush” in Context7 MCP Server could allow malicious instructions into AI tools – Read More –
A suspected Iran-nexus threat actor has been attributed to a campaign targeting government officials in Iraq by impersonating the country’s Ministry of Foreign Affairs to deliver a set of never-before-seen malware. Zscaler ThreatLabz, which observed the activity in January 2026, is tracking the cluster under the name Dust Specter. The attacks, which manifest in the … Read More “Dust Specter Targets Iraqi Officials with New SPLITDROP and GHOSTFORM Malware – The Hacker News” »
Exploit kit “Coruna” targets iPhones running iOS 13.0 to 17.2.1, focusing on financial data theft – Read More –
Cybersecurity researchers have disclosed details of a new Russian cyber campaign that has targeted Ukrainian entities with two previously undocumented malware families named BadPaw and MeowMeow. “The attack chain initiates with a phishing email containing a link to a ZIP archive. Once extracted, an initial HTA file displays a lure document written in Ukrainian concerning … Read More “APT28-Linked Campaign Deploys BadPaw Loader and MeowMeow Backdoor in Ukraine – The Hacker News” »
Organizations typically roll out multi-factor authentication (MFA) and assume stolen passwords are no longer enough to access systems. In Windows environments, that assumption is often wrong. Attackers still compromise networks every day using valid credentials. The issue is not MFA itself, but coverage. Enforced through an identity provider (IdP) such as Microsoft Entra ID, Okta, … Read More “Where Multi-Factor Authentication Stops and Credential Abuse Starts – The Hacker News” »
Ox Security warns that Mail2Shell could enable threat actors to hijack FreeScout systems without user interaction – Read More –
A global operation has resulted in the takedown of popular cybercrime forum LeakBase – Read More –
Two of the 48 Cisco vulnerabilities, affecting Secure Firewall Management Center, are maximum-severity flaws – Read More –
A joint law enforcement operation has dismantled LeakBase, one of the world’s largest online forums for cybercriminals to buy and sell stolen data and cybercrime tools. The LeakBase forum, per the U.S. Department of Justice (DoJ), had over 142,000 members and more than 215,000 messages between members as of December 2025. Those attempting to access … Read More “FBI and Europol Seize LeakBase Forum Used to Trade Stolen Credentials – The Hacker News” »
Europol-Led Operation Takes Down Tycoon 2FA Phishing-as-a-Service Linked to 64,000 Attacks – The Hacker News

Tycoon 2FA, one of the prominent phishing-as-a-service (PhaaS) toolkits that allowed cybercriminals to stage adversary-in-the-middle (AitM) credential harvesting attacks at scale, was dismantled by a coalition of law enforcement agencies and security companies. The subscription-based phishing kit, which first emerged in August 2023, was described by Europol as one of the largest phishing – Read … Read More “Europol-Led Operation Takes Down Tycoon 2FA Phishing-as-a-Service Linked to 64,000 Attacks – The Hacker News” »
Nowadays, information is among the most precious resources of companies and states in the digital age. The cross-border and system-to-system… The post Why India Needs Indigenous HSMs for DPDP Act and RBI Compliance appeared first on JISA Softech Pvt Ltd. – Read More – JISA Softech Pvt Ltd
When a top cybersecurity firm discovered it had a leak, you would expect the FBI to be called. Instead, the person put in charge of the investigation was the actual leaker… who promptly sent an innocent colleague into a career-ending ambush. In this episode, we unravel the jaw-dropping tale of a defence contractor caught selling … Read More “Smashing Security podcast #457: How a cybersecurity boss framed his own employee – GRAHAM CLULEY” »
Fake Zoom, Teams Meeting Invites Use Compromised Certificates to Drop Malware – Hackread – Cybersecurity News, Data Breaches, AI and More

A new phishing campaign is using stolen certificates from TrustConnect Software PTY LTD to sign malware. By impersonating updates for Zoom and Microsoft Teams, hackers install RMM tools to gain persistent, privileged access to networks – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
How to Avoid Confidentiality Gaps in Early-Stage Startups – Hackread – Cybersecurity News, Data Breaches, AI and More

Startups often expose sensitive data during pitches and hiring. Learn when to use NDAs and simple workflows to close confidentiality gaps. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Institutional DeFi: Building Secure Bridges Between Decentralized Protocols and Corporate Treasury – Hackread – Cybersecurity News, Data Breaches, AI and More
Institutional DeFi helps corporations improve treasury liquidity, speed cross-border settlements, and manage capital using secure permissioned blockchain protocols. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Tycoon 2FA, a major phishing kit and platform that allowed low-skilled cybercriminals to bypass multifactor authentication and conduct large-scale adversary-in-the-middle attacks, was dismantled Wednesday by a global coalition of security companies and law enforcement agencies. Microsoft, which led the effort alongside Europol and authorities from six countries and 11 security firms or organizations, said it … Read More “Global coalition dismantles Tycoon 2FA phishing kit – CyberScoop” »
Can anonymity on the internet survive in the age of generative AI? A recent study from ETH Zurich examined how Large Language Models can combine information from across the internet to identify the human behind the accounts of various online platforms. In the study, LLM agents were given anonymous bios based on real profiles from users … Read More “LLMs are getting better at unmasking people online – CyberScoop” »
Can anonymity on the internet survive in the age of generative AI? A recent study from ETH Zurich examined how Large Language Models can combine information from across the internet to identify the human behind the accounts of various online platforms. In the study, LLM agents were given anonymous bios based on real profiles from users … Read More “LLMs are getting better at unmasking people online – CyberScoop” »
Multiple vulnerabilities have been discovered in Google Android OS, the most severe of which could allow for remote code execution. Android is an operating system developed by Google for mobile devices, including, but not limited to, smartphones, tablets, and watches. Successful exploitation of the most severe of these vulnerabilities could allow for remote code execution. … Read More “Multiple Vulnerabilities in Google Android OS Could Allow for Remote Code Execution – Cyber Security Advisories – MS-ISAC” »
Best DeleteMe Alternatives (2026): Competitors and Comparisons – Hackread – Cybersecurity News, Data Breaches, AI and More
Best DeleteMe alternatives for 2026 compared, including Incogni, Optery, Aura, Kanary, and Privacy Bee for data broker removal and privacy protection. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
149 Hacktivist DDoS Attacks Hit 110 Organizations in 16 Countries After Middle East Conflict – The Hacker News

Cybersecurity researchers have warned of a surge in retaliatory hacktivist activity following the U.S.-Israel coordinated military campaign against Iran, codenamed Epic Fury and Roaring Lion. “The hacktivist threat in the Middle East is highly lopsided, with two groups, Keymous+ and DieNet, driving nearly 70% of all attack activity between February 28 and March 2,” Radware … Read More “149 Hacktivist DDoS Attacks Hit 110 Organizations in 16 Countries After Middle East Conflict – The Hacker News” »
Authorities from 14 countries shut down LeakBase, seized its domains and arrested multiple people allegedly involved in the cybercrime marketplace for stolen data and hacking tools, the Justice Department said Wednesday. LeakBase had more than 142,000 members, ranking it among the world’s largest forums for cybercriminals. The site, which was available on the open web, … Read More “Authorities from 14 countries shut down major cybercrime forum LeakBase – CyberScoop” »
A coalition of seven Western nations has launched guidelines to help integrate security-by-design principles into future 6G standards – Read More –
Reclaim Security Raises $26M to Eliminate the 27-Day Remediation Gap – Hackread – Cybersecurity News, Data Breaches, AI and More

New York, USA, 4th March 2026, CyberNewswire – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
The Most Common Swap Scams in 2026, and How to Avoid Them – Hackread – Cybersecurity News, Data Breaches, AI and More

Swap scams target traders through fake DEX sites, token approvals, and phishing. Learn how to detect swap scams and protect funds before you swap now. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Ransomware Breach at University of Hawaii Cancer Center Affects 1.2M People – Hackread – Cybersecurity News, Data Breaches, AI and More

The University of Hawaii Cancer Centre has confirmed a massive ransomware attack affecting 1.24 million people. Sensitive data, including Social Security numbers and historical voter records dating back to 1993, was compromised. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Law enforcers and industry partners have taken down notorious phishing-as-a-service platform Tycoon2FA – Read More –
Cloudflare’s inaugural threat intelligence report identifies a series of weaknesses in technology that attackers have abused and industrialized into professional “attack factories,” leaving most organizations unprepared to respond. Attackers are turning the very services victims deploy and pay for into tools for launching large-scale attacks. Researchers say the barrier to entry has vanished, as identities … Read More “Attackers are using your network against you, according to Cloudflare – CyberScoop” »
Malware campaign uses Ukrainian email service for credibility, deploying “BadPaw” to execute attacks – Read More –
Increased attempts to compromise surveillance cameras linked to Iran during Middle East conflict – Read More –
Coruna iOS Exploit Kit Uses 23 Exploits Across Five Chains Targeting iOS 13–17.2.1 – The Hacker News
Google said it identified a “new and powerful” exploit kit dubbed Coruna (aka CryptoWaters) targeting Apple iPhone models running iOS versions between 13.0 and 17.2.1. The exploit kit featured five full iOS exploit chains and a total of 23 exploits, Google Threat Intelligence Group (GTIG) said. It’s not effective against the latest version of iOS. … Read More “Coruna iOS Exploit Kit Uses 23 Exploits Across Five Chains Targeting iOS 13–17.2.1 – The Hacker News” »
As AI becomes the central engine for enterprise productivity, security leaders are finally getting the green light — and the budget — to secure it. But there’s a quiet crisis unfolding in the boardroom: many organizations know they need “AI Governance,” but they have no idea what they are actually looking for. The CISO’s Dilemma: … Read More “New RFP Template for AI Usage Control and AI Governance – The Hacker News” »
Car Tyre Sensors Can Be Used to Track Drivers Without Their Knowledge – Hackread – Cybersecurity News, Data Breaches, AI and More

New research from IMDEA Networks reveals how unencrypted signals from tyre pressure sensors in brands like Toyota and Mercedes can be used for covert vehicle tracking. Learn how these low-cost systems can map out your daily routines and why current regulations fail to protect driver privacy. – Read More – Hackread – Cybersecurity News, Data … Read More “Car Tyre Sensors Can Be Used to Track Drivers Without Their Knowledge – Hackread – Cybersecurity News, Data Breaches, AI and More” »
Phishing in 2026: 3 Attack Tactics That Beat Most Enterprise Defenses – Hackread – Cybersecurity News, Data Breaches, AI and More

Phishing drives about 90% of cyberattacks in 2026, using tactics like encrypted flows, QR code scams, and trusted cloud platforms to steal credentials. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Cybercriminals are now increasingly using Telegram to sell corporate access, malware subscriptions, and stealer logs, turning the messaging app into a fast cybercrime hub. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Telegram Increasingly Used to Sell Access, Malware and Stolen Logs – Hackread – Cybersecurity News, Data Breaches, AI and More

Cybercriminals are now increasingly using Telegram to sell corporate access, malware subscriptions, and stealer logs, turning the messaging app into a fast cybercrime hub. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
The OpenID Foundation warns that fragmented policies on posthumous digital accounts could open the door for fraudsters to exploit AI deepfakes – Read More –
Cybersecurity researchers have flagged malicious Packagist PHP packages masquerading as Laravel utilities that act as a conduit for a cross-platform remote access trojan (RAT) that’s functional on Windows, macOS, and Linux systems. The names of the packages are listed below – nhattuanbl/lara-helper (37 Downloads) nhattuanbl/simple-queue (29 Downloads) nhattuanbl/lara-swagger (49 Downloads) – Read More – The … Read More “Fake Laravel Packages on Packagist Deploy RAT on Windows, macOS, and Linux – The Hacker News” »