The financial ecosystem in India is changing radically. As digital banking, fintech networks, UPI-based applications and API-driven financial services… The post Designing a DPDP-Ready Crypto Architecture for BFSI & Fintech appeared first on JISA Softech Pvt Ltd. – Read More – JISA Softech Pvt Ltd
Author: Aakash Chaudhary
Dutch Intel Warns of Russian Hackers Hijacking Signal, WhatsApp Attacks – Hackread – Cybersecurity News, Data Breaches, AI and More

Dutch intelligence warns Russian hackers are hijacking Signal and WhatsApp accounts using fake support bots and verification code scams targeting officials and journalists. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Fake CleanMyMac Site Uses ClickFix Trick to Install SHub Stealer on macOS – Hackread – Cybersecurity News, Data Breaches, AI and More
Researchers warn of a fake CleanMyMac site using a ClickFix attack to install SHub Stealer on macOS and steal passwords and crypto wallets. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Malicious npm Package Posing as OpenClaw Installer Deploys RAT, Steals macOS Credentials – The Hacker News
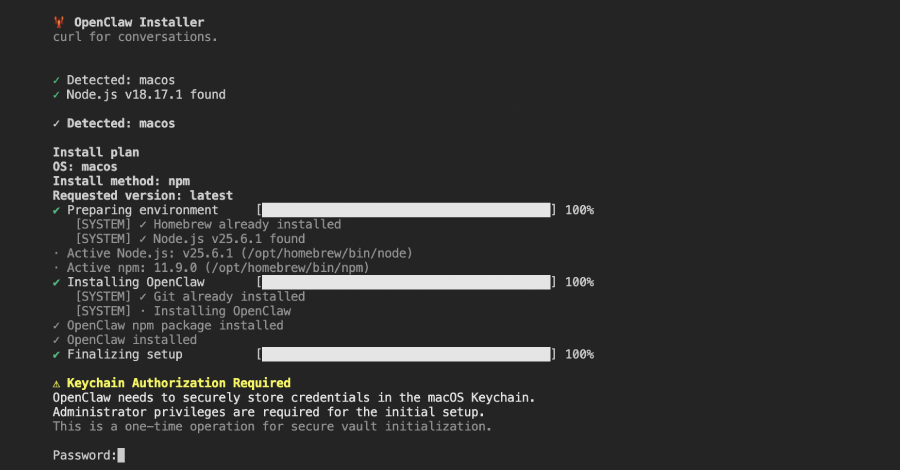
Cybersecurity researchers have discovered a malicious npm package that masquerades as an OpenClaw installer to deploy a remote access trojan (RAT) and steal sensitive data from compromised hosts. The package, named “@openclaw-ai/openclawai,” was uploaded to the registry by a user named “openclaw-ai” on March 3, 2026. It has been downloaded 178 times to date. The … Read More “Malicious npm Package Posing as OpenClaw Installer Deploys RAT, Steals macOS Credentials – The Hacker News” »
The Trump administration is plotting an interagency body to confront malign hackers, pilot programs to secure critical infrastructure across states and other steps tied to its freshly-released cyber strategy, National Cyber Director Sean Cairncross said Monday. The “interagency cell” will bring together agencies like the Justice Department, the Department of State, the FBI and the … Read More “Sean Cairncross lays out what’s coming next for Trump’s cyber strategy – CyberScoop” »
UNC4899 Breached Crypto Firm After Developer AirDropped Trojanized File to Work Device – The Hacker News

The North Korean threat actor known as UNC4899 is suspected to be behind a sophisticated cloud compromise campaign targeting a cryptocurrency organization in 2025 to steal millions of dollars in cryptocurrency. The activity has been attributed with moderate confidence to the state-sponsored adversary, which is also tracked under the cryptonyms Jade Sleet, PUKCHONG, Slow Pisces, … Read More “UNC4899 Breached Crypto Firm After Developer AirDropped Trojanized File to Work Device – The Hacker News” »
Huntress researchers uncover campaign exploiting vulnerabilities to steal data using Elastic Cloud as a data hub – Read More –
⚡ Weekly Recap: Qualcomm 0-Day, iOS Exploit Chains, AirSnitch Attack & Vibe-Coded Malware – The Hacker News
Another week in cybersecurity. Another week of “you’ve got to be kidding me.” Attackers were busy. Defenders were busy. And somewhere in the middle, a whole lot of people had a very bad Monday morning. That’s kind of just how it goes now. The good news? There were some actual wins this week. Real ones. … Read More “⚡ Weekly Recap: Qualcomm 0-Day, iOS Exploit Chains, AirSnitch Attack & Vibe-Coded Malware – The Hacker News” »
Iran’s MuddyWater Hackers Target US Firms with New Dindoor Backdoor – Hackread – Cybersecurity News, Data Breaches, AI and More

Researchers say Iran’s MuddyWater hackers targeted US companies and an Israeli software firm’s department in a cyber campaign using the Dindoor malware – All this amid the ongoing conflict. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Security Risk Advisors Releases “The Purple Perspective 2026” Report – Hackread – Cybersecurity News, Data Breaches, AI and More

Philadelphia, PA, United States, 9th March 2026, CyberNewswire – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
US national cyber strategy focuses on stronger defenses, countering threats, fostering innovation – Read More –
Over one in five winners of IT-Harvest’s 2026 Cyber 150 are AI security companies – Read More –
New UK Online Crime Centre will combine expertise from a range of sources to takedown online channels cyber-scammers rely on – Read More –
Post Content – Read More – IC3.gov News
AI Bot Hackerbot-Claw Targets Microsoft, DataDog and CNCF GitHub Repos – Hackread – Cybersecurity News, Data Breaches, AI and More

Security firm Pillar reveals the Chaos Agent in which Hackerbot-Claw, an AI agent, used natural language to compromise major GitHub projects and hijack developer tools. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Mid-market organizations are constantly striving to achieve security levels on a par with their enterprise peers. With heightened awareness of supply chain attacks, your customers and business partners are defining the security level you must meet. What if you could be the enabler for your organization to remain competitive — and help win business — … Read More “Can the Security Platform Finally Deliver for the Mid-Market? – The Hacker News” »
We’ve seen ransomware cost American lives. Here’s what it will actually take to stop it. – CyberScoop

Flights canceled. Emergency rooms shut down. Centuries-old companies shuttered. Ransomware and other similar cyberattacks have become so routine that even those serious human and economic consequences are often overlooked or easily forgotten. This lack of focus is dangerous. As former leaders of FBI and CISA cyber units, we’ve seen cybercrime ripple through communities – disrupting … Read More “We’ve seen ransomware cost American lives. Here’s what it will actually take to stop it. – CyberScoop” »
Chrome Extension Turns Malicious After Ownership Transfer, Enabling Code Injection and Data Theft – The Hacker News

Two Google Chrome extensions have turned malicious after what appears to be a case of ownership transfer, offering attackers a way to push malware to downstream customers, inject arbitrary code, and harvest sensitive data. The extensions in question, both originally associated with a developer named “[email protected]” (BuildMelon), are listed below – QuickLens – Search Screen … Read More “Chrome Extension Turns Malicious After Ownership Transfer, Enabling Code Injection and Data Theft – The Hacker News” »
Derrick Van Yeboah admitted he stole over $10m in romance scams as part of crime gang – Read More –
Billing services provider TriZetto Provider Solutions has begun notifying millions of patients about a data breach – Read More –
Web Server Exploits and Mimikatz Used in Attacks Targeting Asian Critical Infrastructure – The Hacker News
High-value organizations located in South, Southeast, and East Asia have been targeted by a Chinese threat actor as part of a years-long campaign. The activity, which has targeted aviation, energy, government, law enforcement, pharmaceutical, technology, and telecommunications sectors, has been attributed by Palo Alto Networks Unit 42 to a previously undocumented threat activity group dubbed … Read More “Web Server Exploits and Mimikatz Used in Attacks Targeting Asian Critical Infrastructure – The Hacker News” »
AI-based assistants or “agents” — autonomous programs that have access to the user’s computer, files, online services and can automate virtually any task — are growing in popularity with developers and IT workers. But as so many eyebrow-raising headlines over the past few weeks have shown, these powerful and assertive new tools are rapidly shifting … Read More “How AI Assistants are Moving the Security Goalposts – Krebs on Security” »
New Social Security Scam Emails Use Fake Tax Documents to Hijack PCs – Hackread – Cybersecurity News, Data Breaches, AI and More

A new phishing campaign is targeting thousands in the US by posing as the Social Security Administration. Learn how scammers use fake 2025/2026 tax statements and Datto RMM software to hijack computers and steal data, as shared with Hackread.com – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
OpenAI Codex Security Scanned 1.2 Million Commits and Found 10,561 High-Severity Issues – The Hacker News
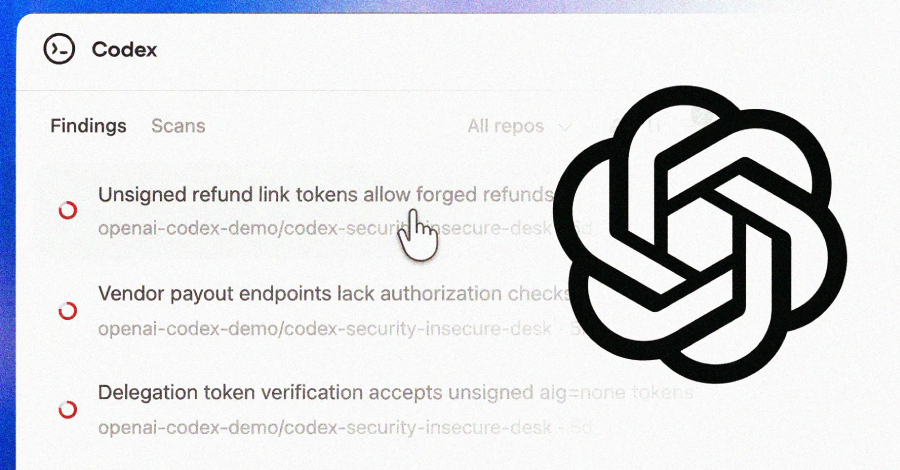
OpenAI on Friday began rolling out Codex Security, an artificial intelligence (AI)-powered security agent that’s designed to find, validate, and propose fixes for vulnerabilities. The feature is available in a research preview to ChatGPT Pro, Enterprise, Business, and Edu customers via the Codex web with free usage for the next month. “It builds deep context … Read More “OpenAI Codex Security Scanned 1.2 Million Commits and Found 10,561 High-Severity Issues – The Hacker News” »
Hackers Spread Fake Red Alert Rocket Alert App to Spy on Israeli Users – Hackread – Cybersecurity News, Data Breaches, AI and More

Researchers at Acronis have discovered a malicious trojanized version of the Red Alert rocket warning app targeting Israeli Android users. Distributed via fake Home Front Command SMS messages, this spyware steals GPS data, SMS messages, and contact lists while maintaining full alert functionality. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and … Read More “Hackers Spread Fake Red Alert Rocket Alert App to Spy on Israeli Users – Hackread – Cybersecurity News, Data Breaches, AI and More” »
Anthropic on Friday said it discovered 22 new security vulnerabilities in the Firefox web browser as part of a security partnership with Mozilla. Of these, 14 have been classified as high, seven have been classified as moderate, and one has been rated low in severity. The issues were addressed in Firefox 148, released late last … Read More “Anthropic Finds 22 Firefox Vulnerabilities Using Claude Opus 4.6 AI Model – The Hacker News” »
President Donald Trump released his administration’s cyber strategy Friday, promoting offense operations in cyberspace, securing federal networks and critical infrastructure, streamlining regulations, leveraging emerging technologies and strengthening the cybersecurity workforce. Trump also signed an executive order Friday directing agencies to take action to combat cybercrime and fraud. A little more than half of the five … Read More “The long-awaited Trump cyber strategy has arrived – CyberScoop” »
President Donald Trump released his administration’s cyber strategy Friday, promoting offense operations in cyberspace, securing federal networks and critical infrastructure, streamlining regulations, leveraging emerging technologies and strengthening the cybersecurity workforce. Trump also signed an executive order Friday directing agencies to take action to combat cybercrime and fraud. A little more than half of the five … Read More “The long-awaited Trump cyber strategy has arrived – CyberScoop” »
Microsoft warns North Korean threat groups are scaling up fake worker schemes with generative AI – CyberScoop

North Korean threat groups are using artificial intelligence tools to accelerate and expand the country’s long-running scheme to get remote technical workers hired at global companies for longer durations, Microsoft Threat Intelligence said in a report Friday. AI services are empowering North Korean operatives across the attack lifecycle. Attackers have turned AI into a “force … Read More “Microsoft warns North Korean threat groups are scaling up fake worker schemes with generative AI – CyberScoop” »
900+ Certificates Used by Fortune 500, Governments Exposed by Key Leaks – Hackread – Cybersecurity News, Data Breaches, AI and More

A joint study by Google and GitGuardian reveals that over 2,600 valid TLS certificates, protecting Fortune 500 companies and government agencies, were compromised due to private key leaks on GitHub and DockerHub. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
How hackers bypassed MFA with a $120 phishing kit – until a global takedown shut it down – GRAHAM CLULEY

In a co-ordinated public-private operation between law enforcement agencies and cybersecurity industry partners, Tycoon 2FA – one of the world’s most prolific phishing-as-a-service platforms – has been dismantled. Read more in my article on the Hot for Security blog. – Read More – GRAHAM CLULEY
The post DHS CISO, deputy CISO exit amid reported IT leadership overhaul appeared first on CyberScoop. – Read More – CyberScoop
Cybersecurity researchers have disclosed details of a multi-stage malware campaign that uses batch scripts as a pathway to deliver various encrypted remote access trojan (RATs) payloads that correspond to XWorm, AsyncRAT, and Xeno RAT. The stealthy attack chain has been codenamed VOID#GEIST by Securonix Threat Research. At a high level, the obfuscated batch script is … Read More “Multi-Stage VOID#GEIST Malware Delivering XWorm, AsyncRAT, and Xeno RAT – The Hacker News” »
Transparent Tribe Uses AI to Mass-Produce Malware Implants in Campaign Targeting India – The Hacker News

The Pakistan-aligned threat actor known as Transparent Tribe has become the latest hacking group to embrace artificial intelligence (AI)-powered coding tools to strike targets with various implants. The activity is designed to produce a “high-volume, mediocre mass of implants” that are developed using lesser-known programming languages like Nim, Zig, and Crystal and rely on trusted … Read More “Transparent Tribe Uses AI to Mass-Produce Malware Implants in Campaign Targeting India – The Hacker News” »
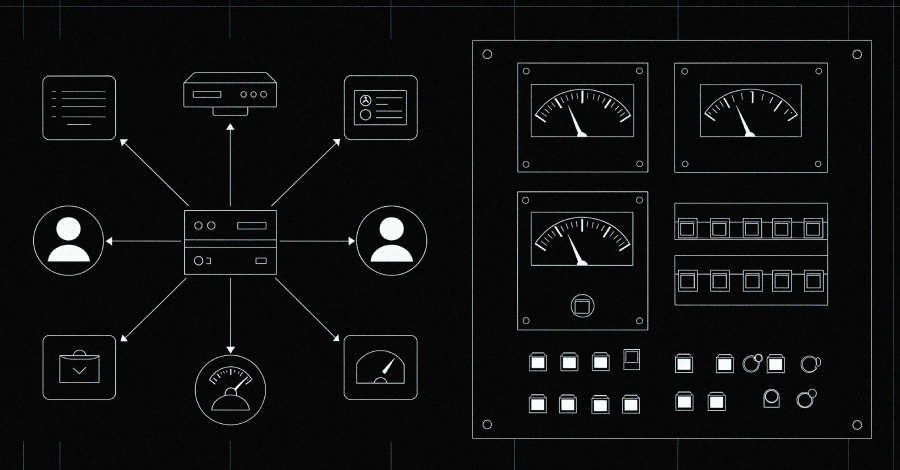
A bank, an airport, a non-profit and the Israeli branch of a US software company were among the targets of this new MuddyWater campaign – Read More –
The House Energy and Commerce committee unanimously passed a package of bipartisan cybersecurity bills Thursday targeting the energy sector, including legislation that would reauthorize and fund a critical federal cybersecurity assistance program for rural electric utilities across the country. The Rural and Municipal Utility Cybersecurity Act, introduced by Reps. Mariannette Miller-Meeks, R-Iowa, and Jennifer McClellan, … Read More “Congress looks to revive critical cyber program for rural electric utilities – CyberScoop” »
Cisco Patches 48 Firewall Vulnerabilities with Two CVSS 10 Flaws – Hackread – Cybersecurity News, Data Breaches, AI and More

Cisco patches 48 vulnerabilities in Secure Firewall products, including two critical CVSS 10 flaws that could allow authentication bypass and remote code execution. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Almost a quarter of the zero days detected by Google in 2025 targeted security and networking appliances – Read More –
New research from Broadcom’s Symantec and Carbon Black Threat Hunter Team has discovered evidence of an Iranian hacking group embedding itself in several U.S. companies’ networks, including banks, airports, non-profit, and the Israeli arm of a software company. The activity has been attributed to a state-sponsored hacking group called MuddyWater (aka Seedworm). It’s affiliated with … Read More “Iran-Linked MuddyWater Hackers Target U.S. Networks With New Dindoor Backdoor – The Hacker News” »
Scaling cybersecurity services as an MSP or MSSP requires technical expertise and a business model that delivers measurable value at scale. Risk-based cybersecurity is the foundation of that model. When done right, it builds client trust, increases upsell opportunities, and drives recurring revenue. But to deliver this consistently and efficiently, you need the right technology … Read More “The MSP Guide to Using AI-Powered Risk Management to Scale Cybersecurity – The Hacker News” »
China-Linked Hackers Use TernDoor, PeerTime, BruteEntry in South American Telecom Attacks – The Hacker News

A China-linked advanced persistent threat (APT) actor has been targeting critical telecommunications infrastructure in South America since 2024, targeting Windows and Linux systems and edge devices with three different implants. The activity is being tracked by Cisco Talos under the moniker UAT-9244, describing it as closely associated with another cluster known as FamousSparrow. It’s worth … Read More “China-Linked Hackers Use TernDoor, PeerTime, BruteEntry in South American Telecom Attacks – The Hacker News” »
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added two security flaws impacting Hikvision and Rockwell Automation products to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation. The critical-severity vulnerabilities are listed below – CVE-2017-7921 (CVSS score: 9.8) – An improper authentication vulnerability affecting – Read More – The Hacker … Read More “Hikvision and Rockwell Automation CVSS 9.8 Flaws Added to CISA KEV Catalog – The Hacker News” »
Microsoft Reveals ClickFix Campaign Using Windows Terminal to Deploy Lumma Stealer – The Hacker News
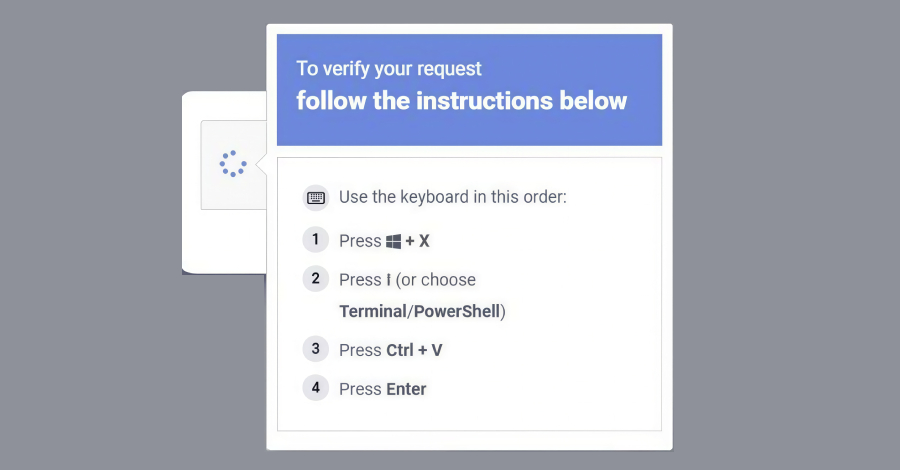
Microsoft on Thursday disclosed details of a new widespread ClickFix social engineering campaign that has leveraged the Windows Terminal app as a way to activate a sophisticated attack chain and deploy the Lumma Stealer malware. The activity, observed in February 2026, makes use of the terminal emulator program instead of instructing users to launch the … Read More “Microsoft Reveals ClickFix Campaign Using Windows Terminal to Deploy Lumma Stealer – The Hacker News” »
Multiple vulnerabilities have been discovered in Cisco products, the most severe of which could allow for remote code execution. Cisco Secure Firewall Management Center (FMC) is a centralized management platform for Cisco firewalls. Cisco Secure Firewall Adaptive Security Appliance (ASA) Software is the core operating system that powers the Cisco ASA family of firewalls. Cisco … Read More “Multiple Vulnerabilities in Cisco Products Could Allow for Remote Code Execution – Cyber Security Advisories – MS-ISAC” »
A vulnerability has been discovered in pac4j-jwt (JwtAuthenticator) which could allow for authentication bypass. pac4j-jwt is a Java module within the pac4j security framework designed for generating, validating, and managing JSON Web Tokens (JWT) to secure web applications and services. It supports signed and encrypted tokens, primarily using the Nimbus JOSE+JWT library to handle authentication, … Read More “A Vulnerability in pac4j-jwt (JwtAuthenticator) Could Allow for Authentication Bypass – Cyber Security Advisories – MS-ISAC” »
The Hidden Cyber Risks of Remote Work Infrastructure – Hackread – Cybersecurity News, Data Breaches, AI and More

Hidden cyber risks in remote work include insecure home Wi-Fi, phishing attacks, and data exposure, leaving businesses and employees vulnerable to breaches. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Pakistan-Linked APT36 Floods Indian Govt Networks With AI-Made ‘Vibeware’ – Hackread – Cybersecurity News, Data Breaches, AI and More

Bitdefender research reveals Pakistani group APT36 is using AI-generated vibeware and trusted cloud services like Google Sheets to target Indian officials. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
The FBI found evidence that its networks had been targeted in a suspected cybersecurity incident, the bureau confirmed on Thursday, without sharing any further details. “The FBI identified and addressed suspicious activities on FBI networks, and we have leveraged all technical capabilities to respond,” the agency said in a statement. “We have nothing additional to … Read More “FBI targeted with ‘suspicious’ activity on its networks – CyberScoop” »
PleaseFix Flaw Lets Hackers Access 1Password Vault via Comet AI Browser – Hackread – Cybersecurity News, Data Breaches, AI and More
Researchers at Zenity Labs uncover PleaseFix flaws in Perplexity’s Comet browser. See how zero-click calendar invites allow AI agents to steal 1Password credentials and personal files. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
5 Best Next Gen Endpoint Protection Platforms in 2026 – Hackread – Cybersecurity News, Data Breaches, AI and More

Discover the best next-gen endpoint protection platforms in 2026, built to detect modern threats, stop credential abuse, and secure enterprise devices. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More