A spear-phishing campaign which spread across the Middle East between 2023 and 2024 has now been linked to Bitter APT group – Read More –
Author: Joe-W
macOS 26.4 update introduced security warnings into Terminal to prevent ClickFix attacks, so attackers have shifted to Script Editor instead – Read More –
SANS Institute reveals that AI agents are behind a 76% surge in non-human identities – Read More –
GPUBreach uses GPU Rowhammer on GDDR6 to flip bits, corrupt page tables and escalate to system root – Read More –
Google’s threat intel team warns UNC6783, a new extortion group possibly linked to the “Raccoon” persona, is targeting BPOs and enterprises – Read More –
Ninja Forms File Upload RCE via unauthenticated arbitrary file upload; update to 3.3.27 immediately – Read More –
Google API key flaw exposes mobile apps to Gemini AI access, private files and billing risks – Read More –
Smashing Security podcast #462: LinkedIn is spying on you, and you agreed to nothing – GRAHAM CLULEY

LinkedIn has been secretly scanning your browser for over 6,000 installed extensions — on every single click you make. It can tell if you’re job hunting, what religion you are, and whether you have ADHD. And none of this is mentioned anywhere in their privacy policy. Meanwhile, California’s crypto millionaires are learning that no amount … Read More “Smashing Security podcast #462: LinkedIn is spying on you, and you agreed to nothing – GRAHAM CLULEY” »
Cybersecurity researchers have flagged a new variant ofmalware called Chaosthat’scapable of hitting misconfigured cloud deployments, marking an expansion of the botnet’s targeting infrastructure. “Chaos malware is increasingly targeting misconfigured cloud deployments, expanding beyond its traditional focus on routers and edge devices,” Darktrace said in a new report. – Read More – The Hacker News
Operation Masquerade: FBI Disrupts Russian Router Hacking Campaign – Hackread – Cybersecurity News, Data Breaches, AI and More

Operation Masquerade: The FBI and DoJ disrupted a Russian GRU campaign that hijacked routers via DNS attacks to spy on users and steal credentials. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Cybersecurity researchers have lifted the curtain on a stealthy botnet that’s designed for distributed denial-of-service (DDoS) attacks. Called Masjesu, the botnet has been advertised via Telegram as a DDoS-for-hire service since it first surfaced in 2023. It’s capable of targeting a wide range of IoT devices, such as routers and gateways, spanning multiple architectures. “Built for … Read More “Masjesu Botnet Emerges as DDoS-for-Hire Service Targeting Global IoT Devices – The Hacker News” »
An apparent hack-for-hire campaign from a group with suspected Indian government connections targeted Middle Eastern and North African journalists and activists using spyware, three collaborating organizations said in reports published Wednesday. The attacks shared infrastructure that pointed to the advanced persistent threat group known as Bitter, which most frequently targets government, military, diplomatic and critical … Read More “Hack-for-hire spyware campaign targets journalists in Middle East, North Africa – CyberScoop” »
In September of 2024, ZDI received a vulnerability submission from an anonymous researcher affecting npm CLI that revealed a fundamental design issue in Node.js. This blog details how it continues to expose applications to local privilege escalation (LPE) attacks on Windows systems, including the Discord desktop app (CVE-2026-0776 0-Day), which remains unpatched and vulnerable. The … Read More “Node.js Trust Falls: Dangerous Module Resolution on Windows – Zero Day Initiative – Blog” »
The Russian threat actor known as APT28 (aka Forest Blizzard and Pawn Storm) has been linked to a fresh spear-phishing campaign targeting Ukraine and its allies to deploy a previously undocumented malware suite codenamed PRISMEX. “PRISMEX combines advanced steganography, component object model (COM) hijacking, and legitimate cloud service abuse for command-and-control,” Trend Micro – Read More – … Read More “APT28 Deploys PRISMEX Malware in Campaign Targeting Ukraine and NATO Allies – The Hacker News” »
Storm-1175 Deploys Medusa Ransomware Within 24 Hours of Flaw Disclosure – Hackread – Cybersecurity News, Data Breaches, AI and More
Microsoft researchers have uncovered a fast-moving group, Storm-1175, launching high-speed Medusa ransomware attacks against healthcare and education sectors in the UK, US, and Australia by exploiting security flaws in as little as 24 hours. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
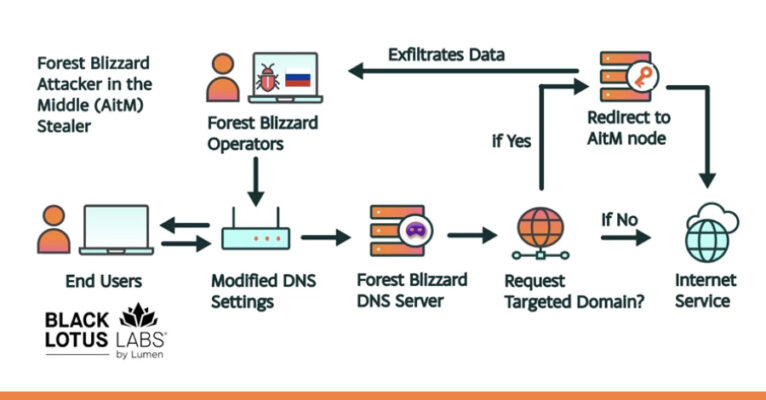
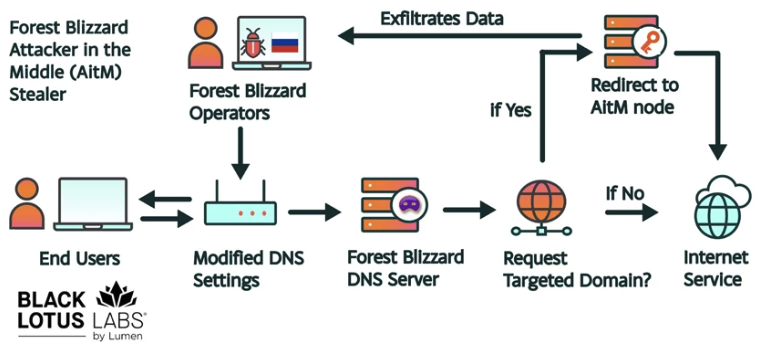
Russian Forest Blizzard Hackers Hijack Home Routers for Global Spying – Hackread – Cybersecurity News, Data Breaches, AI and More

Microsoft Threat Intelligence reveals how Russian hacking group Forest Blizzard uses home routers for DNS hijacking and spying. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Shrinking the IAM Attack Surface through Identity Visibility and Intelligence Platforms (IVIP) – The Hacker News
The Fragmented State of Modern Enterprise Identity Enterprise IAM is approaching a breaking point. As organizations scale, identity becomes increasingly fragmented across thousands of applications, decentralized teams, machine identities, and autonomous systems. The result is Identity Dark Matter: identity activity that sits outside the visibility of centralized IAM and – Read More – The Hacker News
Anthropic launches Project Glasswing, using its Claude Mythos Preview AI to autonomously identify and fix undiscovered vulnerabilities in critical software – Read More –
Anthropic’s Claude AI has helped researchers find a vulnerability in Apache ActiveMQ Classic – Read More –
The FBI deployed a method to unplug US-based routers compromised by APT28 from the threat actor’s malicious network – Read More –
New ClickFix Attack Uses Node.js Malware via Tor to Steal Crypto – Hackread – Cybersecurity News, Data Breaches, AI and More

Netskope Threat Labs report a new ClickFix attack using fake CAPTCHAs to deploy Tor-backed NodeJS malware and drain crypto wallets on Windows. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Artificial Intelligence (AI) company Anthropic announced a new cybersecurity initiative called Project Glasswing that will use a preview version of its new frontier model, Claude Mythos, to find and address security vulnerabilities. The model will be used by a small set of organizations, including Amazon Web Services, Apple, Broadcom, Cisco, CrowdStrike,& – Read More – The Hacker News
The North Korea-linked persistent campaign known as Contagious Interview has spread its tentacles by publishing malicious packages targeting the Go, Rust, and PHP ecosystems. “The threat actor’s packages were designed to impersonate legitimate developer tooling […], while quietly functioning as malware loaders, extending Contagious Interview’s established playbook into a coordinated – Read More – The Hacker News
CISA has revealed Iranian attacks causing disruption and financial loss at US critical infrastructure firms – Read More –
Iran-Linked Hackers Disrupt U.S. Critical Infrastructure by Targeting Internet-Exposed PLCs – The Hacker News

Iran-affiliated cyber actors are targeting internet-facing operational technology (OT) devices across critical infrastructures in the U.S., including programmable logic controllers (PLCs), cybersecurity and intelligence agencies warned Tuesday. “These attacks have led to diminished PLC functionality, manipulation of display data and, in some cases, operational disruption and financial – Read More – The Hacker News
Russian state-sponsored attackers compromised more than 18,000 routers spread across more than 120 countries to gain deeper access to sensitive networks for a large-scale espionage campaign before it was recently neutralized, researchers and authorities said Tuesday. Forest Blizzard, also known as APT28 and Fancy Bear, exploited known vulnerabilities to steal credentials for thousands of TP-Link … Read More “Feds quash widespread Russia-backed espionage network spanning 18,000 devices – CyberScoop” »
Multiple vulnerabilities have been discovered in Mozilla products, the most severe of which could allow for arbitrary code execution. Mozilla Firefox is a web browser used to access the Internet. Mozilla Firefox ESR is a version of the web browser intended to be deployed in large organizations. Mozilla Thunderbird is an email client. Mozilla … Read More “Multiple Vulnerabilities in Mozilla Products Could Allow for Arbitrary Code Execution – Cyber Security Advisories – MS-ISAC” »
Post Content – Read More – IC3.gov News
Hackers Pose as Non-Profit Developers to Deploy Monero Mining Malware – Hackread – Cybersecurity News, Data Breaches, AI and More
REF1695 hackers spread Monero mining malware via fake non-profit installers, using stealth tactics to evade detection and hijack systems for profit. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Iranian government hackers are launching disruptive cyberattacks on American energy and water infrastructure, U.S. government agencies “urgently” warned Tuesday. The hackers are taking aim at devices and systems that control industrial processes, and have harmed victims in the last month following the onset of U.S.-Israel strikes against Iran, according to the joint alert from the … Read More “Iranian hackers launching disruptive attacks at U.S. energy, water targets, feds warn – CyberScoop” »
Tech giants launch AI-powered ‘Project Glasswing’ to identify critical software vulnerabilities – CyberScoop

Major technology companies have joined forces in an effort to use advanced artificial intelligence to identify and address security flaws in the world’s most critical software systems, marking a significant shift in how the industry approaches cybersecurity threats. Anthropic announced Project Glasswing on Tuesday, bringing together Amazon, Apple, Broadcom, Cisco, CrowdStrike, the Linux Foundation, Microsoft, … Read More “Tech giants launch AI-powered ‘Project Glasswing’ to identify critical software vulnerabilities – CyberScoop” »
Cybercrime remains a booming business. Annual cybercrime losses amounted to almost $20.9 billion last year, reflecting a 26% increase from 2024, the FBI’s Internet Crime Complaint Center (IC3) said in its annual report Tuesday. The comprehensive study exposes a worsening digital crime environment that is driving financial losses, with momentum moving in the wrong direction … Read More “Cybercrime losses jumped 26% to $20.9 billion in 2025 – CyberScoop” »
The Russia-linked threat actor known as APT28 (aka Forest Blizzard) has been linked to a new campaign that has compromised insecure MikroTik and TP-Link routers and modified their settings to turn them into malicious infrastructure under their control as part of a cyber espionage campaign since at least May 2025. The large-scale exploitation campaign has been codenamed – … Read More “Russian State-Linked APT28 Exploits SOHO Routers in Global DNS Hijacking Campaign – The Hacker News” »
Hackers linked to Russia’s military intelligence units are using known flaws in older Internet routers to mass harvest authentication tokens from Microsoft Office users, security experts warned today. The spying campaign allowed state-backed Russian hackers to quietly siphon authentication tokens from users on more than 18,000 networks without deploying any malicious software or code. Microsoft … Read More “Russia Hacked Routers to Steal Microsoft Office Tokens – Krebs on Security” »
A high-severity security vulnerability has been disclosed in Docker Engine that could permit an attacker to bypass authorization plugins (AuthZ) under specific circumstances. The vulnerability, tracked as CVE-2026-34040 (CVSS score: 8.8), stems from an incomplete fix for CVE-2024-41110, a maximum-severity vulnerability in the same component that came to light in July 2024. ” – Read More – The Hacker … Read More “Docker CVE-2026-34040 Lets Attackers Bypass Authorization and Gain Host Access – The Hacker News” »
GrafanaGhost Vulnerability Allows Data Theft via AI Injection – Hackread – Cybersecurity News, Data Breaches, AI and More

GrafanaGhost is a critical vulnerability in Grafana’s AI components that uses indirect prompt injection and protocol-relative URL bypasses to exfiltrate data. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
Newly identified malicious campaigns are linked to virtual private servers modified by APT28 to operate as malicious DNS servers – Read More –
GrafanaGhost chains AI prompt injection and URL flaws to exfiltrate sensitive Grafana data – Read More –
Security researchers at Noma Security have disclosed a new vulnerability they are calling GrafanaGhost, an exploit capable of silently stealing sensitive data from Grafana environments by chaining multiple security bypasses, including a method that circumvents the platform’s AI model guardrails without requiring any user interaction. Grafana is widely deployed across enterprise organizations as a central … Read More “‘GrafanaGhost’ bypasses Grafana’s AI defenses without leaving a trace – CyberScoop” »
AI Agents and Non-Human Identities Creating Critical Security Gaps, Report – Hackread – Cybersecurity News, Data Breaches, AI and More
New research from Keeper Security, reveals non-human identities and automated system-to-system interactions are becoming the top security risk for businesses in 2026. – Read More – Hackread – Cybersecurity News, Data Breaches, AI and More
An active campaign has been observed targeting internet-exposed instances running ComfyUI, a popular stable diffusion platform, to enlist them into a cryptocurrency mining and proxy botnet. “A purpose-built Python scanner continuously sweeps major cloud IP ranges for vulnerable targets, automatically installing malicious nodes via ComfyUI-Manager if no exploitable node is already – Read More – The Hacker … Read More “Over 1,000 Exposed ComfyUI Instances Targeted in Cryptomining Botnet Campaign – The Hacker News” »
New advisory warns cyber threat group APT28 have exploited vulnerable edge devices to support malicious operations. – Read More – All Feed
Russian cyber actor APT28 exploit vulnerable routers to hijack DNS, enabling adversary‑in‑the‑middle attacks and theft of passwords and authentication tokens. – Read More – All Feed
Cryptocurrency scams alone cost victims over $7 billion, while AI-enabled fraud threats are on the rise, says FBI – Read More –
When talking about credential security, the focus usually lands on breach prevention. This makes sense when IBM’s 2025 Cost of a Data Breach Report puts the average cost of a breach at $4.4 million. Avoiding even one major incident is enough to justify most security investments, but that headline figure obscures the more persistent problems caused by recurring credential … Read More “The Hidden Cost of Recurring Credential Incidents – The Hacker News” »
In the rapid evolution of the 2026 threat landscape, a frustrating paradox has emerged for CISOs and security leaders: Identity programs are maturing, yet the risk is actually increasing. According to new research from the Ponemon Institute, hundreds of applications within the typical enterprise remain disconnected from centralized identity systems. These “dark – Read More – The Hacker News
Threat actors likely associated with the Democratic People’s Republic of Korea (DPRK) have been observed using GitHub as command-and-control (C2) infrastructure in multi-stage attacks targeting organizations in South Korea. The attack chain, per Fortinet FortiGuard Labs, involves obfuscated Windows shortcut (LNK) files acting as the starting point to drop a decoy PDF – Read More – The Hacker News
Microsoft has released a new report about the Storm-1175 group and its connection to Medusa ransomware – Read More –
Artificial Intelligence (AI) is as reliable as the data that it ingests. With enterprises broadening their use of AI… The post Building secure AI data pipelines with CryptoBind appeared first on JISA Softech Pvt Ltd. – Read More – JISA Softech Pvt Ltd
New academic research has identified multiple RowHammer attacks against high-performance graphics processing units (GPUs) that could be exploited to escalate privileges and, in some cases, even take full control of a host. The efforts have been codenamed GPUBreach, GDDRHammer, and GeForge. GPUBreach goes a step further than GPUHammer, demonstrating for the first time that – Read More – The … Read More “New GPUBreach Attack Enables Full CPU Privilege Escalation via GDDR6 Bit-Flips – The Hacker News” »























![[Webinar] How to Close Identity Gaps in 2026 Before AI Exploits Enterprise Risk – The Hacker News](https://attackfeed.com/wp-content/uploads/2026/04/webinar-cerby-wZRKDG.jpg)