A phishing campaign tied to AI cloud-hosting service Railway has given hackers access to the Microsoft cloud accounts for hundreds of businesses, according to researchers at Huntress.
Rich Mozeleski, product manager for Huntress’ identity team, told CyberScoop the campaign is currently tied to a smaller actor and approximately a dozen IP addresses, but has managed to compromise hundreds of targets in the past few weeks.
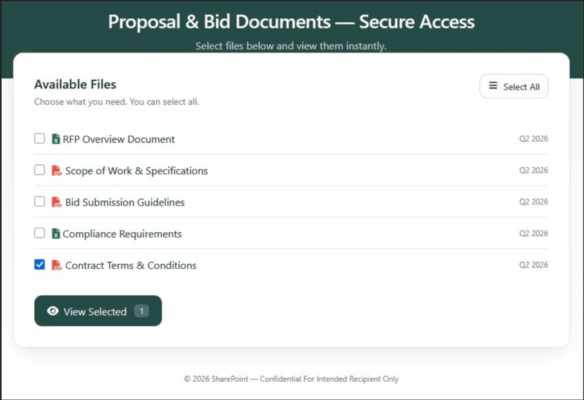
In early March it was compromising a few dozen targets a day, but starting March 3, there was a “massive increase” in that tempo. Mozeleski said that in addition to being more sophisticated than usual, there were no identical emails or domains used, leading researchers to suspect that they may have been generated through artificial intelligence tools. The templates ranged from traditional email lures to QR codes and co-opted file-share sites.
“Just the amount of it was like Pandora’s Box had opened, and the efficacy was just through the roof,” Mozeleski said.
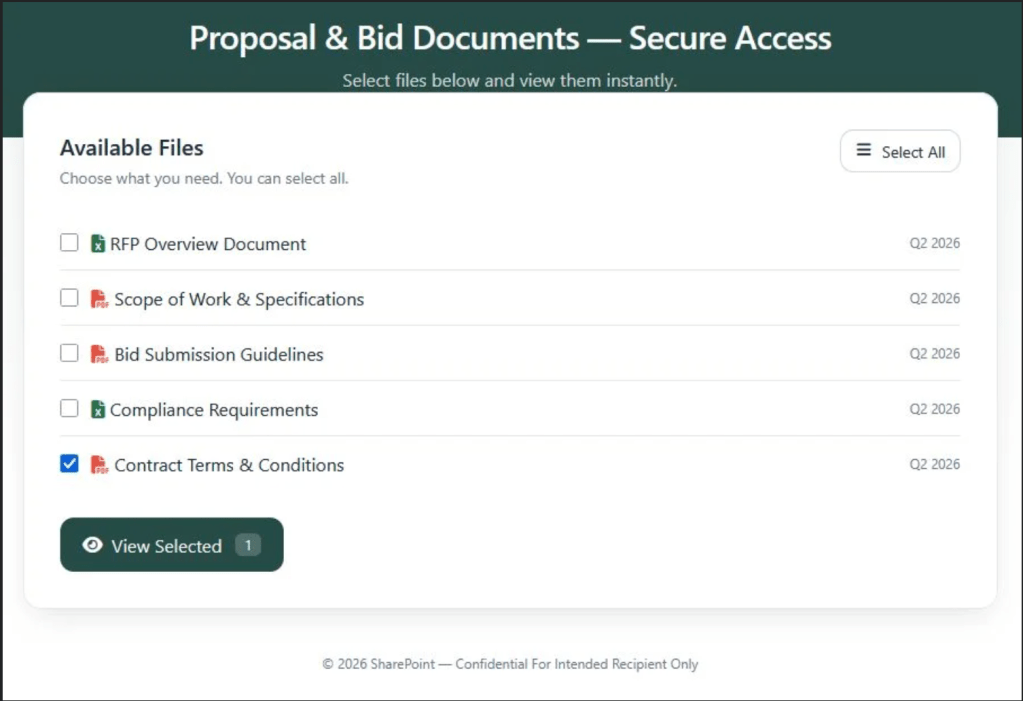
A custom file download phishing lure used in the campaign. Researchers believe the attackers used AI to generate unique lures at scale. (Source: Huntress)
The phishing campaign exploits Microsoft’s authentication flow for devices such as smart TVs, printers and terminals, which gives the attacker valid OAuth tokens for that account for up to 90 days without needing a password or multifactor authentication.
Ultimately, Huntress has seen hundreds of its customers fall for the phishing scams, though they claim to have prevented post-compromise activity in all cases. But they also believe their customers represent only a small fraction of the likely total victim set, which could number in the thousands.
The affected entities span a range of sectors: construction and trade companies, law firms, nonprofits, real estate, manufacturing, finance and insurance, healthcare, government and public safety organizations were all among the 344 victims detailed in the Huntress blog.
To protect customers, Mozeleski said Huntress issued a conditional access policy update Wednesday to 60,000 Microsoft cloud tenants on emails coming from Railway domains, an act he described as “not anything we’ve ever done before.”
Weaponizing vibe-coded infrastructure
Researchers believe the attackers were weaponizing Railway’s Platform as a Service — built to help non-coders build websites and tools — to spin up credential harvesting infrastructure for the campaign.
By using compromised domains and pumping out bespoke lures, the phishing emails avoid most commercial email filtering solutions. It’s not clear if they used Railway’s AI tool or a separate one to generate the lures. Either way, all the attacks Huntress has observed are coming through Railway.com IP infrastructure.
In response to questions from CyberScoop on Friday, Railway solutions engineer Angelo Saraceno said the company is aware of the incident and was first contacted by Huntress on March 6 regarding phishing traffic originating from a specific IP address and three domains. “The associated accounts were banned and the domains were blocked,” Saraceno said.
“Our heuristics are built to catch correlations: repeated credit cards, shared code sources, overlapping infrastructure,” he wrote in an email. “When a campaign avoids those signals, it gets further than we’d like.”
Saraceno called Railway’s fraud detection “a balance” between catching bad actors and getting flooded with false positives, pointing to an incident in February when fine-tuning in the company’s automated abuse enforcement system led to a customer outage.
Earlier Friday, Mozeleski told CyberScoop that Huntress continued to see more than 50 compromises a day tied to Railway phishing domains. When asked what more Railway could have done to prevent abuse of their platform, he said vetting and validation on the free use of their product could be improved. He pointed to products with similar trials, like MailChimp and HubSpot, that have controls and oversight in place so users can’t “go pump in a million contacts and start spamming.”
“Do not allow anybody to come in, start a trial, spin up resources, and start using your infrastructure” for cyberattacks, he said.
One of the more striking contrasts of the campaign was the use of AI to create phishing infrastructure akin to a state-sponsored threat actor or advanced cybercriminal group in service of a garden-variety phishing scam.
It bolsters warnings coming from cybersecurity experts that low-level cybercriminals — often called “script kiddies” for their reliance on automated hacking tools — are poised to become one of the biggest beneficiaries of the generative AI era. Last month, John Hultquist, chief analyst at Google’s Threat Intelligence Group, said that he expects that AI tools will help “smaller cybercriminal outfits more than state-sponsored hackers.”
Testimonials on Railway’s website tout the service’s ability to deliver “vertical auto-scale out of the box”, while another said it “makes spinning up self-hosted third-party tools almost effortless.”
It may also give them a leg up on victim organizations that have more restrictive internal policies around the use of AI for cyber defense.
“We are seeing crooks as the first movers of AI,” said Prakash Ramamurthy, chief product officer at Huntress. “They don’t have any qualms about PII, they don’t have any qualms about model training … and this incident, just in the sheer pace at which it has evolved, is kind of a testament to that.”
The post An AI-powered phishing campaign has compromised hundreds of organizations appeared first on CyberScoop.
–
Read More – CyberScoop